
Alert
Summary This machine involves exploiting an XSS vulnerability in a markdown file upload feature to perform directory traversal, leading to the discovery of an .htpasswd file. Cracking the hash wit...

Summary This machine involves exploiting an XSS vulnerability in a markdown file upload feature to perform directory traversal, leading to the discovery of an .htpasswd file. Cracking the hash wit...

Summary The machine on involves exploiting a Flask web app vulnerable to CVE-2024-23334 in pymatgen. Uploading a malicious CIF file with a reverse shell grants initial access as the app user. Port...

Summary The machine involves exploiting an Active Directory environment. Initial enumeration reveals valid users via Kerbrute and SMB shares. Credentials for the user rose are provided, allowing a...

Summary Install Kerbrute on Kali ARM64: clone, modify Makefile (add arm64), compile, verify. Enables Kerberos brute-force testing. └─# git clone https://github.com/ropnop/kerbrute.git Cloning int...

Summary Scrambled begins with enumerating a Domain Controller, discovering valid users via Kerbrute. Forcing Kerberos authentication with impacket-smbclient reveals an SMB share containing a PDF h...

Summary An attacker enumerates SMB, finding a share with UserInfo.exe. Decompiling it reveals LDAP credentials (support\ldap). LDAP queries expose the support user’s password in the info field. Us...
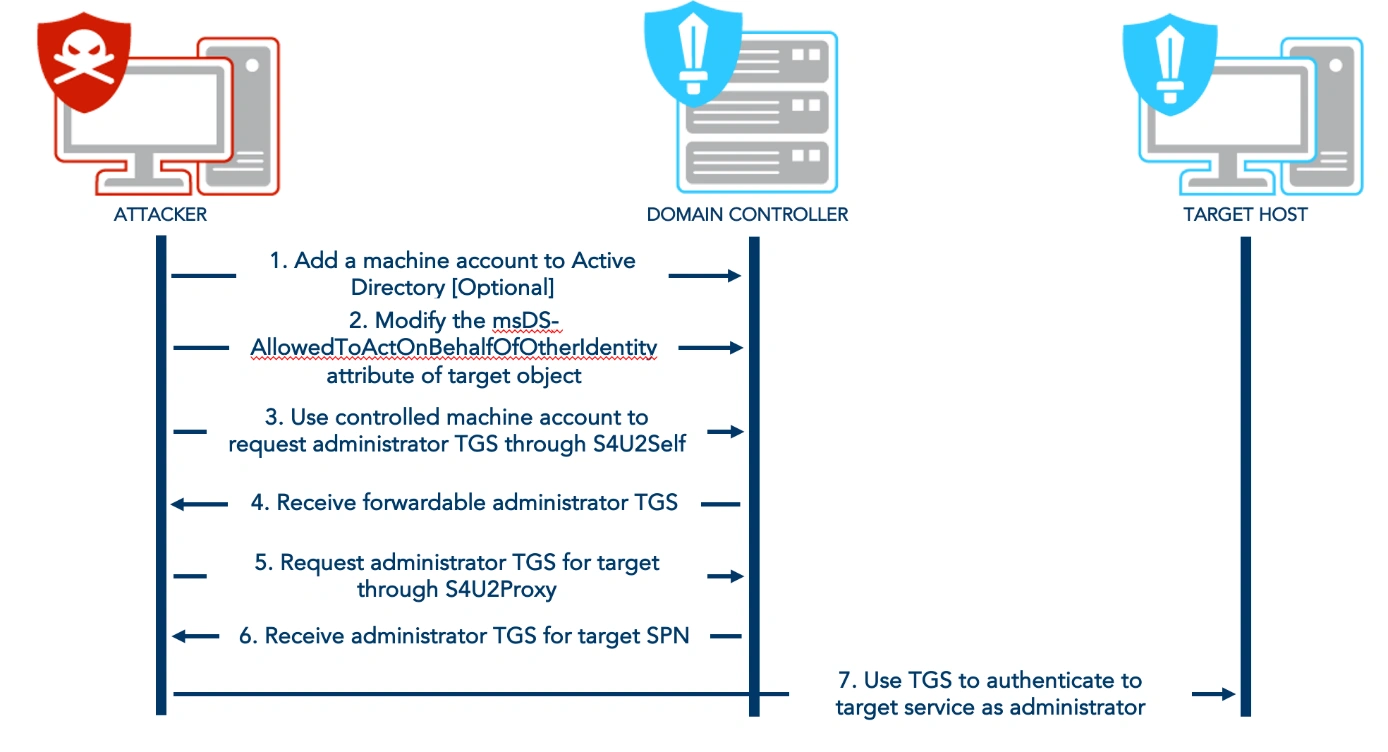
Summary Resource-Based Constrained Delegation (RBCD) is a feature in Active Directory (AD) that allows a service to delegate access to another service on behalf of a user. Creating a Machine Acco...

Summary The machine begins with port scans revealing SSH (22), HTTP (80/64999). The web app on port 80 uses IronWAF, with a vulnerable room.php parameter (cod) allowing SQL injection via UNION-bas...

Summary A pfSense firewall (HTTPS) with default credentials (admin:pfsense) on port 443 is vulnerable to CVE-2014-4688 (graph injection). Exploiting via Metasploit grants root access. Sensitive fi...